What is Endpoint Security?
Endpoint security refers to tools and policies that prevent, detect, and contain threats targeting endpoints. Endpoint threats can involve external attacks as well as insider threats, which may be either malicious or unintentional in nature. A compromised endpoint can give an attacker a foothold within an environment. From that foothold, the threat actor can launch further attacks on systems to access data and compromise additional endpoints via lateral movement.
This glossary post will explore:
What is an Endpoint in Cyber Security?
An endpoint in a cyber security context is any physical or virtual device or hardware that connects to the corporate environment. An endpoint will either use a TCP/IP (v4 or v6) address or another protocol for networking (wired or wireless).
Some examples of endpoints include:
End-user devices, such as desktop PCs, laptops, tablets, and smartphones
Servers
Medical devices, including mHealth endpoints
IoT devices and sensors
Industrial control systems (ICS)
Point-of-sale (PoS) devices
ATMs
Printers
Network switches
Routers
Wearables
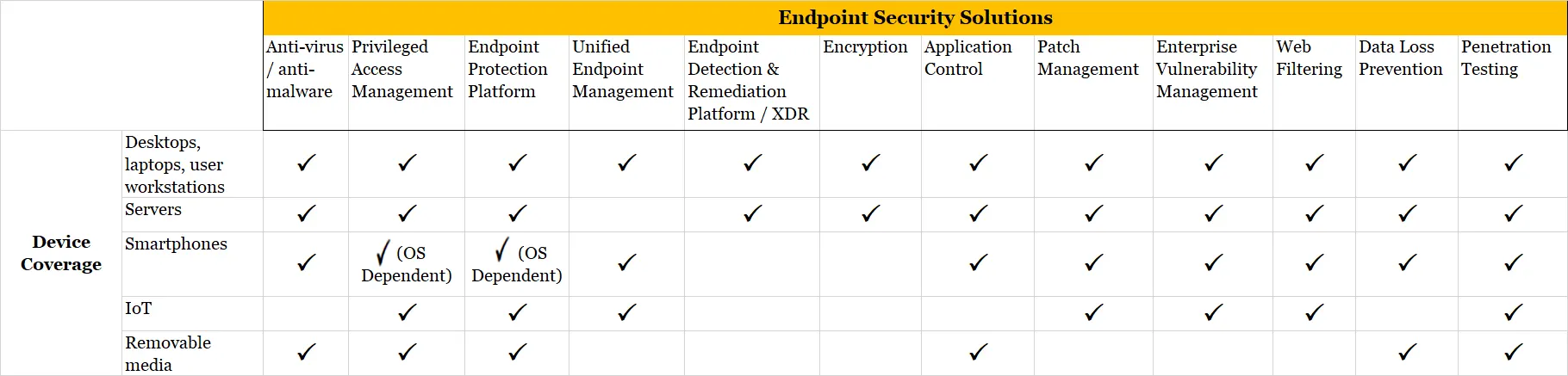
Some endpoint security tools and management technologies function across a variety of endpoints. Other solutions are device or platform-specific (Windows, macOS, Unix, Linux, Android, iOS, Azure, AWS, Google Cloud, etc.)
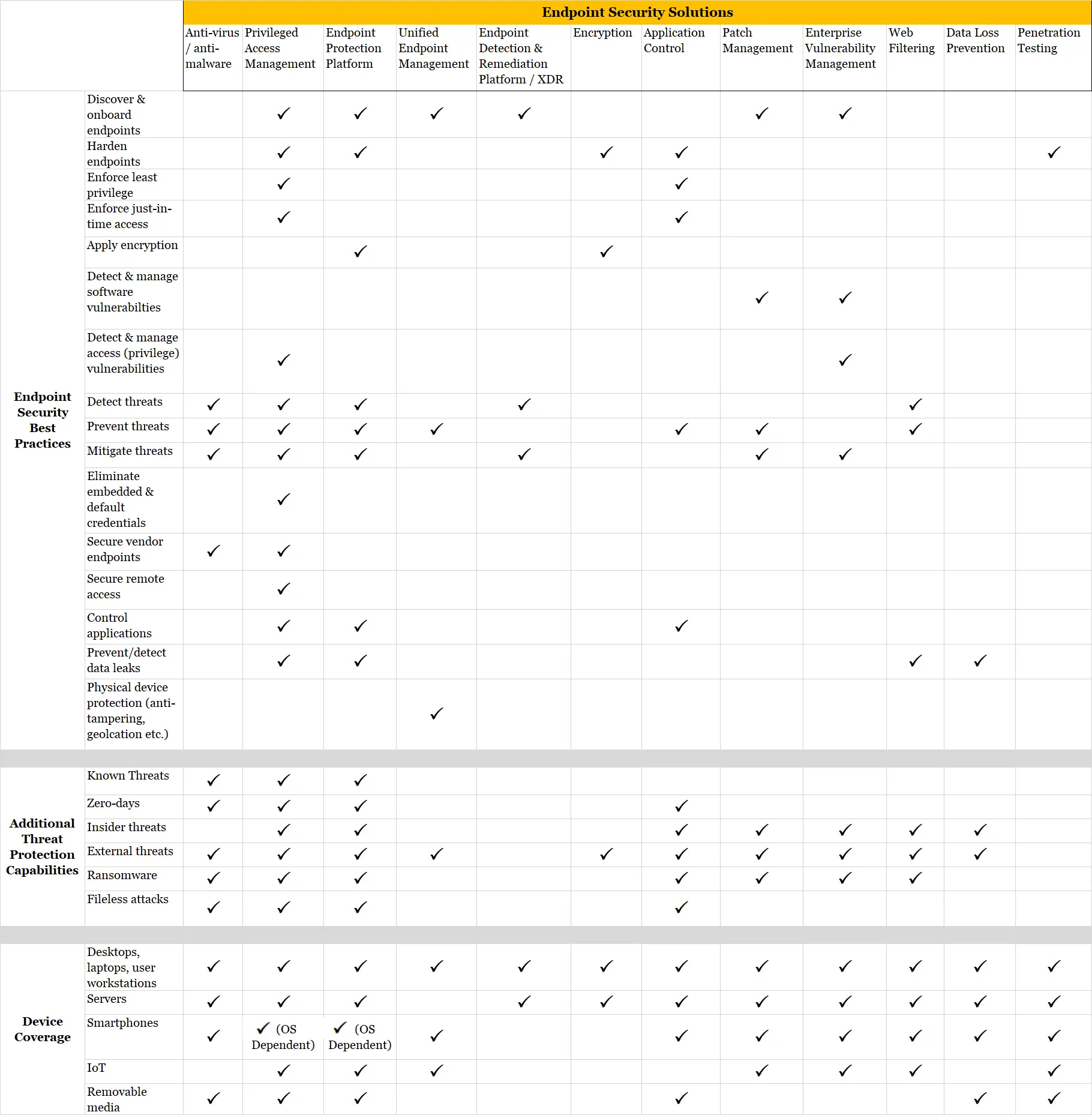
The grid below roughly breaks down the device coverage across some common types of endpoint security solutions. Coverage may vary even between different vendor product offerings within a solution space.
Why Enterprise Endpoint Security is Important
Endpoint security is important because endpoints have become a common foothold for attackers who want to gain access to organizations. According to the Verizon 2025 Data Breach Investigations Report, 'server is the most common asset in a breach and is now present in 95% of them'. We also see increased risk associated with a variety of systems and devices. According to BeyondTrust’s Microsoft Vulnerabilities Report 2025, Elevation of Privilege is the most common vulnerability used to exploit Windows systems. Despite this common attack path, users on Windows systems tend to have over-privileged access via local admin rights, as this high-privilege state gets assigned to users by default. Additionally, there has been an increase in MacOS users, and because of this, attackers are turning their attention to MacOS devices. In 2024, security researchers observed nearly two dozen new macOS malware families. Linux systems are increasingly at risk as well, with the number of Linux Kernel CVEs published increasing by 20% YoY, when comparing 2024 to 2025.
Altogether, these factors point to an increased need for endpoint protection across a variety of different devices.
The Benefits of Endpoint Protection
With the right mix of endpoint security tools, strategies, and technologies tailored to their environment, organizations can realize the following benefits:
Improve security: This is the most obvious benefit. Enforcing least privilege and managing vulnerabilities drastically reduces the threat surface. Applying JIT access controls condenses threat windows. Employing signature-based tools keeps endpoints safe from known threats. Implementing this layered strategy drives down the risk of security incidents and data breaches that may arise from external or internal threats.
Enhance endpoint performance: Eliminating superfluous privileges and hardening devices translates into fewer misconfigurations, incompatibilities, security incidents, and other issues that may cause disruption. Preventing malware infection or endpoint compromise by an unauthorized user also protects against endpoint instability.
Simplify compliance and auditability: Restricting features in accordance with least privilege and endpoint hardening practices reduces complexity. This also makes it easier to perform auditing activities and prove compliance. Implementing security controls like session monitoring and management and vulnerability assessments may also provide instant visibility and reporting necessary for compliance efforts. The more tightly an endpoint system is integrated, and the better the visibility across the endpoint universe, the more straightforward the path to compliance.
Enable the enterprise: A strong endpoint cybersecurity posture enables the enterprise in a number of ways. With the right tools, IT can securely enable more types of endpoints and a heterogeneous infrastructure. It can also empower you to pursue business-enabling changes for the environment, including the roll-out of new technologies. For instance, organizations with robust endpoint protection were well-prepared for the seismic shift to remote work during the coronavirus pandemic. Increasingly, companies assess cybersecurity posture before entering a partnership with another company. Most acquiring companies evaluate the cybersecurity posture of their potential acquiree as well, as they aim to avoid any security surprises.
When to Implement Endpoint Protection
Endpoint security is one of the broadest cybersecurity categories and is needed by most modern organizations. It overlaps, integrates with, and complements network security, data security, identity security, and application security. Many IT security solutions provide capabilities that cover multiple security categories across endpoint, network, data, and identity-based models.
A corporate IT network is essentially a linkage of endpoints. This means endpoint integrity and security may be prioritized before implementing security at the network layer.
How Endpoint Security Software Operates
Endpoint protection tools work in a variety of ways to secure endpoints, whether connected to the network or with transient interconnectivity.
Types of endpoint security software may be:
Centrally managed via agentless technology
Installed as client or agent on individual endpoints
Cloud-based
Involve a combination of the above implementations
Protection for individual consumers focuses on technologies deployed on the device. Enterprises, on the other hand, should heavily rely on centralized management across the corporate network. This enables the administration of patches, configuration changes, deployment of policy updates, gather logs, and more.
The Differences Between Rules-Based, Signature-based, and Behavior-based Security
Endpoint security strategies can use rules-based, signature-based, and/or behavior-based security to detect, prevent, and/or mitigate threats in the following ways:
Pattern matching and signature-based (traditional antivirus, vulnerability management, etc.): Relies on threat signatures to block known threats. They may also use heuristics to block suspicious code or actions that share similarities with known threats.
Rules-based and enforcement of advanced policies (privileged access management, endpoint firewalls, encryption, etc.): Applies rules and policies that enforce security best practices, such as least privilege, block lists and allow lists, endpoint firewall rules, and more. The results are predictable based on rule-matching processing.
Behavior-based (endpoint detection and response, etc.): Modern endpoint protection may apply advanced behavioral analysis, machine learning, and even some forms of artificial intelligence to identify threats or inappropriate access. These solutions can process information locally or rely on management servers to aggregate information for advanced detection and response.
Strategies for securing endpoints encompass such practices as endpoint hardening, endpoint isolation, endpoint lifecycle and policy management, and more. These are typically signature and rule based.
14 Common Endpoint Security Threats
There are many challenges that put an organization’s universe of endpoints at risk. Examples include evolving cyber threats, complex and diverse endpoint environments, corporate misalignment of security technologies to threats, and an ever-more stretched IT team.
Many technologies deployed as part of an endpoint security strategy provide overlapping capabilities in some areas while leaving gaps in other areas. Overlapping features may also cause incompatibility issues and produce unpredictable results or degrade endpoint stability.
The 14 most common endpoint security threats present with enterprise endpoints include:
Lack of visibility into the endpoint estate
Overwhelming number and diversity of endpoints
Threat actors
Overprovisioning of privileges / privileged access
Endpoint vulnerabilities
Deficiencies in native OS security and tool sets
Shadow IT
Insider threats
Immature password lifecycle management and authentication
Inadequate encryption
Lost or stolen endpoints
Insecure remote access pathways
The use of personal devices (BYOD)
Vendor access / vendor endpoints
Let's explore each of these challenges further:
1. Lack of visibility into the endpoint estate
Most organizations struggle to understand the scope of their endpoint estate, let alone how to manage it. An organization may have millions of endpoints, and even tens of thousands of undiscovered or unknown endpoints that connect to the network.
2. Overwhelming number and diversity of endpoints
The sheer number and diversity of corporate endpoints present massive challenges and make it hard to standardize security. Non-traditional endpoints proliferate. IoT devices, such as sensors, security cameras, healthcare devices, wearables, etc., are pervasive.
Many IT teams struggle to discover and securely onboard legitimate devices at scale. Compounding this issue, IoT and edge computing devices commonly have hardcoded credentials, software or firmware that cannot be updated, and other severe security drawbacks. The devices may use unsafe or uncommon protocols, and even have built-in backdoors. Because many legacy IoT devices have little computing power, they most likely cannot run security software or host an agent.
Over the last decade, sophisticated attacks waged on operational technology (OT) and industrial control systems (ICS) have been a growing concern. ICS endpoints were traditionally “air-gapped,” meaning they were isolated from internet-facing networks. These critical infrastructure endpoints are becoming increasingly connected, and thus, exposed to cyber risk.
ICS endpoints can include:
Programmable logic controllers (PLCs)
Supervisory control and data acquisition (SCADA) systems
Remote terminal units (RTUs)
Intelligent electronic devices (IEDs)
Human-machine interfaces (HMI)
The rise of the virtual desktop is another challenge. Virtual desktops share many of the risks as physical desktops, but their dynamic and ephemeral nature adds further complexity.
3. Threat actors
hreat actors continue to learn new tricks and acquire more sophisticated tools with powerful AI, ML, and automation capabilities. Modern cybercriminals can easily scale attacks across tens of thousands of endpoints and target across organizations, types of devices, and many other ways.
Attackers can readily acquire toolkits off the dark web, with nation-state caliber tools. These tools can be anything from credential hacking tools and password dictionaries to advanced, polymorphic malware that incorporates machine learning. In addition, malware is ever improving at evading antivirus and other security defenses and blending in with normal processes.
Even phishing, particularly spear-phishing, attacks are getting more savvy. Spear phishers may use scanning tools to mine relevant data across vast resources. They may then leverage machine learning to craft phishing messages that target their victim with eerie precision.
While the vectors used by threat actors are too broad to cover here, one worth mentioning is Living off the Land (LotL) attacks. LotL attacks refers to the leveraging of tools or features that preexist within the target’s environment. These are considered fileless attacks because no execution of files (i.e., malware) is needed to perform their illicit activities. LotL attacks essentially turn a system's own native applications and commands against itself. PowerShell scripts, VB scripts, WMI, and PsExec., and Windows script host executables are common culprits in fileless attacks.
Finally, another potential threat that has lurked on endpoints for decades but gets little attention today is spyware. While this unwanted software is often merely an annoyance, it can compromise privacy, leak data, and potentially perform other malicious actions.
4. Overprovisioning of privileges/privileged access
Managing privileged access on endpoints is critical because endpoints typically have far more privileged access and default system privileges than necessary. Almost every single cyberattack today involves the use of privileged access.
Different operating systems create and manage default privileges differently. Here are a few examples:
In Windows systems, the Administrator account holds superuser privileges, and each computer has at least one local administrator account. Typically, local admin rights far exceed what most users need. Organizations should remove administrative rights from most non-IT users, and some endpoints should be configured with only guest account access.
In Linux and Unix-like systems, the superuser account, called ‘root,’ has unrestricted access to all commands, files, directories, and resources. Organizations should eliminate root access and put tight security controls and session auditing around any superuser access. The sudo (“superuser do”) command allows the user to temporarily elevate privileges to root-level without having direct access to the root account and password. This may suffice in some instances, but it introduces its own security and administration issues.
For macOS endpoints, IT may need to create non-privileged accounts for users (standard users) and manage the local administrator account.
Often, these privileges are persistent (also called “standing privileges”), meaning they are constantly in an active state, ready to get used or exploited. Each instance of excessive privilege risks a privilege-based attack. It also risks a lateral attack. Threat actors exploit privileges to gain an initial foothold, sometimes using indirect, unknown, or otherwise hidden privilege escalation pathways to do so, then escalate privileged access to other endpoints and assets across the corporate network. An Illumio study found that 'most IT and cybersecurity leaders (net: 90%) have detected a security incident involving lateral movement within the past 12 months.'
5. Endpoint vulnerabilities
Endpoint vulnerabilities represent one of the largest security exposures. Most mid-to-large-sized organizations will have thousands of software vulnerabilities strewn across their endpoints due to the infeasibility of remediation. These vulnerabilities can pose a significant threat to organizations. The Verizon 2025 Data Breach Investigations Report cited that "exploitation of vulnerabilities [were] present in 20% of all breaches we analyzed—a 34% increase from last year."
However, fixing a vulnerability on an endpoint can pose its own risks, such as downtime. So, organizations must assess the risks and benefits of remediation. Many enterprises know about various vulnerabilities within their systems and leave them untouched; they might even stay present for multiple years.
Here are the three main types of vulnerabilities found on endpoints:
Firmware vulnerabilities: Firmware is the code/software built into a specific hardware that enables the operation of basic device-level functions. On some devices, firmware is loosely considered to be the device’s operating system (iOS for Apple iPhones). Because they enable the operation of basic functions, firmware vulnerabilities can be dangerous. Some firmware vulnerabilities essentially give a threat actor root access to a device, undermining security features like encryption. Firmware vulnerabilities have become a concern with the proliferation of devices like IoT and smartphones; however, they can also arise in mature vendor products.
Operating system (OS) vulnerabilities can be errors in code or shortcomings of actual features that may pose a risk, such as permitting unnecessary access. Common operating systems found in enterprise environments include Windows, macOS, Unix, and Linux.
Application vulnerabilities are bugs or weaknesses in installed applications. Vulnerabilities could include anything from privilege application vulnerability to backdoor root access, to embedded default credentials. Unlike with firmware and OS systems, end users often have the privileges to install unvetted applications (known as shadow IT). This poses an elevated risk.
Misconfigurations: While not a traditional software vulnerability like the other entries in this section, misconfigurations similarly create security weaknesses that attackers can exploit, or that allow innocent users to inadvertently cause harm. Misconfigurations may not only hamper operations but may also introduce attack vectors. Poor configuration settings could involve open ports, outdated exceptions, insecure protocols allowed, etc.
6. Deficiencies in native OS security and tool sets
As mature as Windows is, many of its OS tool sets are basic and fall far short of the security needed within enterprise environments. Native Windows security components provide only basic protections. These include Windows Defender Antivirus, Windows Firewall (called Windows Defender Firewall in Windows 10), and Local Administrator Password Solution (LAPS). These native technologies are also often disabled within enterprises. On the other hand, Windows BitLocker encryption is often an important part of corporate endpoint security.
Linux has some advanced auditing capabilities, but that's far from enough. The sudo program enables users to elevate system privileges on Unix and Linux systems, without receiving root access. Sudo helps mitigate threats given no alternative. However, sudo itself has many limitations and introduces its own security risks. Put simply, sudo falls woefully short of the enterprise-class privileged access security needed for these environments.
macOS systems have traditionally lagged in security, management, and monitoring tool sets, though security has received a bigger focus from Apple in recent years.
7. Shadow IT
Shadow IT refers to any IT technology within a corporate environment that IT does not provision. Users either install it on the endpoint themselves or access it via the cloud. It can refer to an unauthorized device that the user has connected to the network. When end users self-provision applications or connect unauthorized endpoints to the network, it can introduce several security and operational issues. Shadow IT may be incompatible or interfere with other network systems, suffer from dangerous vulnerabilities, have excessive privileges, and may even introduce a backdoor.
8. Insider threats
Insider threats have always presented one of the most significant risks to corporate endpoints and networks. This is because internal users (employees, vendors, contractors, etc.) already have access on the endpoint. Authorized users tend to fly under the radar of many traditional threat detection solutions. An employee could infect their device by inadvertently opening corrupted content from a phishing email. They could also visit a malicious website that initiates a drive-by download of malware.
If the insider is ill-bent and possesses high levels of privileged access, they can easily inflict catastrophic damage. Insider threats, when they happen, tend to be the most harmful; IBM's Cost of Data Breach Report 2025 found that the average cost of malicious insider attacks was USD 4.92M.
9. Immature password lifecycle management and authentication
Endpoints almost always require credentials, and many of these are privileged. Privileged credentials allow the user (human or machine) to perform powerful functionalities or access sensitive devices or applications. As a result, an attacker can obtain instant access to the network with the right credentials in hand.
Unfortunately, poor password management practices are commonplace within enterprise environments. Here are just a few:
Manually managed credentials, resulting in poor practices (short passwords, uncomplex passwords, and password reuse). The shorter and less complex the password, the easier it is for automated tools to crack it. If a duplicated password becomes compromised, a threat actor can use those stolen credentials to compromise any endpoints that share the same credentials. Personal devices typically have much lower cyber defenses than enterprise endpoints. When employees repeat the same passwords across their personal endpoints and work environment, it poses a considerable risk to the corporate network.
Default and hardcoded passwords may be present in IoT, legacy applications, and various networked devices. Attackers can also find these passwords embedded within compiled code. If the same default password gets reused across a device model, they can then use that information to compromise all similar devices.
Credentials are often shared between users, particularly to perform IT administration tasks. This both heightens the risk of password exposure and makes it almost impossible to trace endpoint activity to a single user. A clear session activity trail is a requirement for many common compliance and audit initiatives.
10. Inadequate encryption
Encryption cracking tools are getting increasingly powerful. Yesterday’s encryption standards can’t always withstand modern attacks. Without proper encryption, an unauthorized user or threat actor can easily read and compromise data should they gain access.
11. Lost or stolen endpoints
In the age of mainframes and desktop computing devices, stolen devices were a rarity. However, once devices went mobile, the number of lost or stolen enterprise devices soon skyrocketed. Stolen or lost devices can create security and compliance risks, especially if the information or access provided by the device is sensitive. The potential for security, legal, and brand fallout increases substantially if the organization fails to properly secure the device.
12. Insecure remote access pathways
A growing mobile and remote workforce means endpoints commonly operate outside the network perimeter. These endpoints often connect remotely via home networks and unmanaged Wi-Fi. RDP, VNC, and SSH protocols can provide basic remote access. However, these tools often get stretched beyond their appropriate use cases, which poses serious security and operational ramifications.
An employee should never use VPNs to connect to corporate networks from their personal devices (BYOD). Vendor endpoints and internal endpoints that need to perform privileged access remotely require more robust technologies. VPNs can’t granularly control, monitor, or report on privileged access—only access in general.
Attackers sometimes plant remote access technologies on targeted endpoints (such as a vendor or IT service provider support systems). The attackers then leverage the remote access on those devices as a jumping-off point for attacks on the vendor/IT service provider’s customers.
Many cyberattacks leverage remote access as a vector, so it’s a critical security piece to get right.
13. The use of personal devices (BYOD)
The use of personal devices for work introduces risks and challenges. A personal device may lack many of the endpoint protections and hardening that corporate-provisioned devices receive. It’s also possible that family members or housemates share the device and have accounts on it. Any of these users’ activities could imperil the corporate network. Bring-Your-Own-Device (BYOD) and VPN should never mix, yet organizations frequently allow protocol tunneling via these methods.
Another complication that occurs with bring-your-own-device deployments is what to do if a device gets lost or stolen. The device owner may object to a remote data wipe because it threatens the potential loss of personal content. This may have high personal value (such as family pictures or videos). However, if that device has any potential to be in the wrong hands, it's in the company's best interest to disable it instantly.
14. Vendor access/vendor endpoints
Vendor access represents perhaps the weakest cybersecurity link for most organizations. IBM's Cost of a Data Breach Report 2025 found that supply chain attacks took the longest of all attack types to resolve at an average 267 days to detect and contain.
VPNs and many other commonly used technologies don’t provide the granular access controls needed. Many organizations are unable to identify the vendor endpoints accessing their systems, let alone monitor or control what is occurring during the sessions. Do the vendor’s own security standards meet those of your enterprise? How do you enforce and validate that? Do some of a vendor’s employees use personal devices to access your network? What happens if the company terminates employees or they leave—could their access remain as an orphan account? The risks arising from vendor endpoints are massive, yet many organizations grant far too many privileges to their vendors.
Since vendors play such an important role for most organizations, getting the vendor access security piece correct is imperative.
10 Best Practices for Securing Endpoints
Organizations should follow a variety of best practices to secure their endpoints, as no single strategy or technology is sufficient on its own to protect your entire, heterogeneous endpoint universe from all threats. Some strategies (endpoint hardening) and technologies (privilege management) may be effective security controls against the vast majority of threats on any type of endpoint. Other strategies (remote wiping, anti-theft protection, etc.) and technologies (antivirus) may only work or be applicable for specific types of endpoints.
Every enterprise should adopt the following endpoint security best practices for defense-in-depth protection:
Define, communicate, and consistently apply your endpoint protection policy
Discover and onboard, or deny access to, endpoints
Endpoint hardening
Enforce least privilege
Apply encryption to protect data stored on the device and in transit
Identify, prioritize, and remediate vulnerabilities
Implement threat detection, prevention, and mitigation
Protect devices from physical threats
Secure vendor endpoints and remote access
Integrate your endpoint security technologies with each other and across the rest of your security and IT stack
Now, we will further break down each of these best practices:
1. Define, communicate, and consistently apply your endpoint protection policy
Your endpoint protection policy is a living, evolving document that should be part of your overarching IT security policy. It should programmatically define best practices and how to apply them. The policy should define strategies, technologies, and data ownership. An example of this is BYOD. If your organization allows BYOD, the policy should clearly define which data the company owns and which belongs to the end user. The policy should detail what should happen in case of a lost or stolen device.
Any personal device used for corporate access should also have some form of mobile device management installed on it. MDM can enforce the separation of personal and corporate resources and provide other security functionalities. Your policy should also clarify the protocols surrounding vendor controls. It should define the security controls you will put around vendor access. IT should also define the security controls you expect each vendor to implement around their own endpoints. Finally, ensure there is a method in place to measure, test, and audit all of these policies to ensure they are functioning as desired.
2. Discover and onboard, or deny access to, endpoints
The next step involves finding and inventorying every endpoint that connects to your network and onboarding them. This includes applying your organization’s security policies to the endpoints after they are discovered. Discovery and onboarding should be a continuous process. In some cases, this step will occur proactively, such as when IT is provisioning a device for a user or deploying a server. In other cases, this will occur reactively, such as when a new, unknown device touches the network. IT should also properly register all devices, then monitor for identifying issues and necessary updates and reconfirming overall health status.
3. Endpoint hardening
Endpoint hardening involves removing or disabling unnecessary programs, access, embedded or other features to condense the attack surface. It is a continuous process performed throughout the lifecycle of technology—from initial installation, through configuration, maintenance, and support, to end-of-life decommissioning. Endpoint hardening practices vary by endpoint, with more complex and powerful endpoints generally requiring more steps. Organizations should always harden endpoints before connecting them to the internet or corporate networks. Application and operating system hardening are two of the most important aspects of endpoint hardening.
OS hardening can entail:
Removing unnecessary drivers, file sharing, libraries, software, services, and functionality
Encrypting local storage
Tightening registry and other systems permissions
Implementing privileged user controls
Application hardening can entail:
Restricting app-to-app communications
Removing or turning off unneeded features
Eliminating embedded credentials and replacing them with API calls
Endpoint hardening is really a subset of actions aligned with the principle of least privilege (PoLP), described below.
4. Enforce least privilege
Since most malware requires privilege to execute, least privilege controls can prevent attacks from compromising an endpoint in the first place. Even if an attacker successfully breaches an endpoint, least privilege ensures that the attack stays contained. Malware and cybercriminals typically need privileged access to move laterally around the environment. Reducing privilege to the minimum level means that even if attackers gain a foothold, they are essentially marooned.
Further, users should only be able to log into privileged accounts when absolutely necessary, and for only the finite moments when needed. This is especially crucial for roles such as Administrator, Domain Admin, or Root. By leveraging this just-in-time privileged access, you condense the threat window by limiting the duration of time when privileges are actually available for use and exploitation.
The ability for least privilege to work across three dimensions makes least privilege arguably the most important and powerful security best practice. It can prevent attacks from landing and executing, limit and prevent movement, and restrict privilege availability based on time. Least privilege can protect against both known and unknown threats, whether they originate internally or externally.
5. Apply encryption to protect data stored on the device and in transit
To minimize the risk of data leaks, the strength of encryption should at least meet the requirements of applicable regulatory standards. More sensitive data (for instance, health data or superuser credentials), may necessitate higher levels of encryption than less sensitive data. Even if a device gets stolen or an email gets intercepted, if robust encryption is in place, the data will be unreadable. Many regulatory and compliance initiatives do not consider the theft or loss of adequately encrypted devices a reportable data breach. This includes the HIPAA Breach Notification Rule.
6. Identify, prioritize, and remediate vulnerabilities
The vulnerability management process involves scanning for and assessing the impact of known vulnerabilities (i.e., CVEs). Next, the vulnerabilities must be compared against the operating system, firmware, custom software, and commercial applications that are running on your endpoints. Your organization should have a mature patch management program. It also needs a strong policy that dictates desired software configurations and how any changes should occur if needed. Also, ensure devices are running supported versions of firmware, software, and applications (etc.).
In some cases, risk-benefit analysis may dictate that no remediation action be taken. This often happens when a vulnerability poses a low risk, but the fix for it may disrupt many endpoints or impact mission-critical systems. Vulnerability remediation can entail applying a patch, performing a configuration change, eliminating embedded or default credentials, etc. Aside from patch management, vulnerability management may also involve pen testing and threat hunting. Pen testing typically involves third-party security professionals and tools probing for vulnerabilities across your endpoints that are exploitable.
In the absence of a working exploit, a vulnerability by itself is just a theoretical risk. However, once an exploit has been architected for a vulnerability, it becomes a threat. Threat hunting refers to the process of proactively seeking out threats by looking for indicators of compromise (IoCs). When threat hunting, you assume that an attack has already occurred and a threat actor is active in your environment.
7. Implement threat detection, prevention, and mitigation
Many viruses, ransomware, and other malware threats are already known and documented. This knowledge should be applied to block, quarantine, remove, or mitigate these threats. While signature-based threat protection can only protect against known malware threats, it remains an important line of defense, as well as a requirement for all regulatory compliance mandates.
8. Protect devices from physical threats
This entails such security controls as:
Implementing anti-theft technology on the devices (i.e., smartphones, PCs).
Enabling GPS location awareness and providing security cables for laptops.
Restricting physical access to the locations where employees use or store the devices.
For instance, you may want to enforce that employees lock laptops in a secure cabinet in an area under constant human and/or video surveillance.
9. Secure vendor endpoints and remote access
Organizations should strive to achieve the same security best practices they uphold within their perimeter beyond their perimeter. This means ensuring just-in-time protocols. Only the right identity using the correct, properly hardened endpoint should have access to the right resources within the right context. To ensure this with the vendor account/endpoint, you need to apply basic identity management and privileged identity controls. Important controls include:
Enforcing least privilege
Applying multi-factor authentication
Rotating passwords and using one-time passwords (OTPs)
Implementing session management and monitoring to audit and control all vendor/remote access-initiated session activity
10. Integrate your endpoint security technologies with each other and across the rest of your security and IT stack
When evaluating any new IT security tool, there are some important questions you should ask yourself first. How does this tool integrate with the rest of my security ecosystem? Does it create synergies, or does it create more complexity and administration issues? Any new tool/solutions should naturally fit within, and become an integrated part of, your IT and IS environment. The more holistic your picture of risk, the more rapidly you can resolve potential threats.
14 Effective Endpoint Security Software and Tools
Effective endpoint security technologies, ordered by priority, include:
Antivirus / Antimalware
Privileged Access Management (PAM) solutions
Endpoint protection platforms (EPP)
Endpoint management
Endpoint detection and remediation (EDR) solutions
Encryption
Application control solutions
Patch management solutions
Vulnerability management (VM) solutions
Web filtering solutions
Data Loss Prevention (DLP) solutions
Penetration (Pen) testing solutions
Endpoint firewalls / host-based firewalls
Anti-spyware
Now we will further break down each of these technologies:
1. Antivirus / Antimalware
Antivirus and antimalware solutions are the most traditional and well-recognized forms of endpoint protection. AV / antimalware typically works by scanning traffic to a device and/or the device’s content for patterns that match a database of virus signatures. While many IT thought leaders have touted the demise of AV, it remains widely deployed.
Basic antivirus software provides detection and protection against known threat signatures. Today, most AV and anti-malware solutions have evolved to incorporate some advanced protection methodologies that incorporate heuristics, behavioral analysis, and even machine learning. Teams typically install enterprise AV / antimalware solutions on a wide array of devices, including servers, desktops and laptops, gateways, and more. In most instances, they centrally manage these solutions, which may include “next-generation AV,” from the corporate network. Some devices, such as smartphones, require specialized AV solutions that work at the device level only.
Many endpoints, such as IoT, lack the computing necessary to install and run AV. As a side note, cloud-based AV deployments may be of some use in these cases. Other well-known drawbacks of solutions in this class include:
Device or network performance degradation when the solution is running
High numbers of missed threats
Numerous false positives and security alerts that hinder IT’s ability to respond to what is important
‘Next generation’ AV solutions tend to avoid some of these issues by leveraging cloud processing and foregoing the use of bloated agents. Some solutions also include sandboxing capabilities. A sandbox essentially quarantines an unknown/suspicious program and runs it in isolation to see if malicious characteristics present themselves.
2. Privileged Access Management (PAM) solutions
PAM solutions, a key requirement of zero trust initiatives, manage privileges for users (human and machine), endpoints, systems, applications, and processes. They also monitor and record activity that occurs during privileged sessions. Organizations can deploy PAM solutions on-premises, in the cloud, or hybrid. Complete PAM platforms offer the following three functional areas:
Privileged Credential/Password Management solutions (i.e., Privileged Account & Session Management solutions) enable automated discovery and onboarding of all privileged accounts. They also enforce secure access to privileged credentials and secrets and audit all privileged activities. By enforcing password security best practices across all types of credentials (passwords, secrets, SSH keys, etc.), Privileged credential management solutions eliminate or mitigate threats. Examples include password reuse, embedded passwords and DevOps secrets, pass-the-hash (PtH), and stolen credentials. Session monitoring and management capabilities empower organizations to audit all activity and pause or terminate suspicious sessions.
Endpoint Privilege Management solutions, also known as Privilege Elevation and Delegation (PEDM), combine least privilege management and advanced application control capabilities to condense the endpoint attack surface. These solutions can protect against sophisticated attacks from fileless malware/living off the land (LoTL) attacks, ransomware, and zero-day exploits. Some can also enable passwordless administration (the ability to perform administrative functions on an endpoint without privileged credentials) and enforce a just-in-time access model. Endpoint privilege management functions within Windows, Mac, Unix and Linux systems, network devices, IoT, and more.
Secure Remote Access solutions apply least privilege and robust audit controls to all remote access sessions required by employees, vendors, and service desks. The granular privilege control and specialized security capabilities of this software far transcend that of VPNs, which it often replaces. Vendor credentials can be securely managed (rotated, encrypted, etc.) from a centralized vault and injected when needed. The vendor never sees them. These PAM solutions also provide granular auditing.
Together, these PAM functionalities can help implement a zero-trust endpoint security approach.
3. Endpoint protection platforms (EPP)
Endpoint protection platforms generally offer a multilayer set of security technologies managed through a centralized console. These solutions aim to protect against multiple threat vectors across an enterprise’s endpoint estate. Many EPPs leverage the cloud to perform analysis, eliminating any processing hit to endpoints. Vendors can often deliver endpoint protection platforms as SaaS and manage them remotely. They can also install these solutions directly on devices that have central management software hosted on a server.
EPP solutions typically perform scanning of files via an advanced AV/antimalware engine that protects against signature-based attacks. This engine also incorporates behavioral analysis to expand threat protection. EPPs usually incorporate endpoint firewalls that help tightly control network traffic through specific ports on the individual endpoints. These solutions may also incorporate basic application control (allowlisting, blocklisting), sandboxing, and machine learning capabilities.
4. Endpoint management
Endpoint management encompasses a range of solutions and processes around managing the lifecycle of endpoints. Endpoint management solutions may be capable of centrally discovering, onboarding, registering, provisioning, updating, monitoring, and troubleshooting endpoint devices. Solutions in this category include mobile device management (MDM), enterprise mobility management (EMM), and unified endpoint management (which may integrate a number of capabilities, including MDM, EMM, etc.). Point solutions, like MDM and EMM, work across certain types of mobile devices. UEM solutions, on the other hand, strive to wrap lifecycle management capabilities around a diverse array of devices. UEM solutions may cover servers, desktops, mobile devices, IoT, and more.
Endpoint management solutions play a key role in optimizing device performance, ensuring correct configurations, and establishing a consistent baseline of device hygiene. These solutions also allow for remote management. They can even wrap security controls (such as remote data wipe, anti-tampering, and geo-tracking) around devices. This provides protection in the event that a device gets lost or stolen.
5. Endpoint detection and remediation (EDR) solutions
Endpoint detection and remediation solutions continuously inspect files and applications that enter a device to extend protection beyond simple signature-based threats. This includes protection against some types of ransomware, zero-day threats, fileless malware, and more advanced attacks.
In contrast to EPP solutions, EDR solutions can provide intrusion detection and a deeper level of advanced threat analysis and forensics. Thus, EDR tools play a bigger role in containing and responding to a security incident or breach event once it has already occurred. However, one of the drawbacks of EDR solutions can be a high number of false positives and security alerts.
Increasingly, IT service providers offer managed detection and remediation (MDR), which provides the customer with capabilities backed by a team of analysts. More recently, EDR has been evolving into XDR. XDR solutions incorporate data sources beyond the endpoint, such as traffic analysis, so they provide a more holistic and context-informed approach than EDR.
6. Encryption
Encryption is the encoding of data so that it is unreadable and unusable without the correct decryption key. As encryption cracking tools have become more powerful, encryption methodologies have had to evolve to ensure data security. Encryption capabilities are important components of many endpoint security solutions (including PAM, DLP, and endpoint firewalls). They are also important native solutions on device firmware and software. Typically, endpoint encryption software either protects individual files or provides protection across the entire hard drive—known as full disk encryption.
7. Application control solutions
Application control solutions secure endpoints, most commonly end-user devices and servers, by preventing them from executing unauthorized applications. Traditionally, these solutions make use of allow lists, block lists, and greylists. Greylisted applications are applications that have been identified, but have not been added to allow or block lists. Special security rules may be put in place so that greylisted applications can run in some circumstances, as needed.
Application control solutions may also be able to enforce granular control over application usage. For instance, application control could allow a specific user/endpoint to execute a certain function of an application. At the same time, it can disable or block the execution of other application functions for that user/endpoint. Cloud-based reputation services may also be leveraged to determine whether an application is safe to run.
Application control can be sold as a point solution, or be included in other platforms, such as endpoint privilege management, or next-generation firewalls (NGFWs). Integration within these other platforms often allows for natural augmentation of the capabilities that provide advanced application protection. Application control solutions must be finely calibrated. They need to enable the seamless use of authorized applications for legitimate use cases while still preventing against malware, ransomware, and other threats.
8. Patch management solutions
These help automate the process of downloading and applying patches to software. In some instances, your IT team may need to manually apply the patches. However, automating the patching process as much as possible helps organizations scale to meet the thousands of vulnerabilities across their endpoint estate. When dealing with a dangerous vulnerability for which an exploit already exists in the wild, time is of the essence, so automation is key. Patch management is a core part of vulnerability management and is often tightly integrated with enterprise vulnerability management solutions.
9. Vulnerability management (VM) solutions
Vulnerability management solutions provide a proactive approach to discovering, analyzing, and remediating vulnerabilities. Drawing from vulnerability databases (CVE, etc.) these solutions perform vulnerability scans that deliver a snapshot of the vulnerabilities found across the endpoint environment. VM solutions put context around the risk, weighing it against the mitigation options for the vulnerability. This helps the organization evaluate the scope and level of risk posed by the threat.
Vulnerability scans generally only represent a moment-in-time snapshot, though some scans that are low-impact on resources may run continuously. Scans often need to run on sensitive resources that require privileged access. These are called credentialed scans as they require injection of credentials to be run. An enterprise-privileged credential management solution should be to inject the credentials into the VM solution. This will accommodate the highly sensitive and privileged nature of such scans. Credentialed scans tend to uncover more dangerous threats than credential scans.
Vulnerability scanning is often highly automated. Some VM solutions can scale across the entire IT infrastructure. However, human input is typically required to determine and initiate the best course of action. Of course, most vulnerability management solutions are dependent on databases of known vulnerabilities (signatures) and provide limited, if any, protection against zero-day threats.
A good vulnerability management tool continuously receives updates on the latest vulnerability signatures.
10. Web filtering solutions
Web filtering solutions (URL filtering, etc.) put controls around the sites that users can access via their browsers. This helps to mitigate the human element of threats. Organizations can block content by category and/or blacklist certain URLs. Employees reaching a blocked page will typically see a message informing them why their access to the request page has been restricted. Web filtering solutions can secure endpoints by preventing them from visiting malicious sites that pose a risk of infection. Web filtering can also block content that a company deems inappropriate. In some settings, such as K-12 schools, this is a compliance requirement.
11. Data Loss Prevention (DLP) solutions
DLP solutions aim to prevent leakage or unauthorized transmission of data. DLP is an important endpoint data protection technology. The solutions analyze context and content to help ensure only the right individual or systems can access the data. Some use cases for DLP include preventing a user from:
Uploading or downloading unauthorized information from a USB
Accessing a sensitive file attachment in an email when using a personally owned device
Emailing a sensitive document (such as containing financial results) to an individual who is not authorized to receive it
Inappropriately sharing sensitive content with a teammate or other individual over a messaging app—even if the organization authorized the app
An organization can deploy DLP across many types of endpoints and systems, including end-user devices, servers, and gateways. These solutions leverage encryption, rules-based structure, and database fingerprinting to make fast, accurate decisions about the legitimacy of data access requests. DLP solutions can also send alerts of inappropriate data access requests to the appropriate IT or compliance personnel.
12. Penetration (Pen) Testing solutions
Pen testing allows security teams and researchers to simulate attacks against an environment and probe for potential vulnerabilities. This process yields information useful for hardening the organization’s defenses. Pen testing is a proactive methodology that is part of an overall vulnerability management program. Some vulnerability management solutions may have built-in pen testing features. Pen testing is a useful way to find potential threats that other tools may miss. The practice can also contribute to a better understanding of how potential changes to IT infrastructure and endpoint configurations could create new attack pathways.
13. Endpoint firewalls/host-based firewalls
Endpoint firewalls (i.e., personal firewalls) are software that runs on endpoints. This is in contrast to the types of firewalls (stateful, packet filtering, next generation, etc.) more closely associated with network security. Teams may install endpoint firewalls on desktops, laptops, and servers. Endpoint firewalls inspect traffic, apply rules, and perform behavioral monitoring. This allows them to protect the endpoint from malware and attacks that originate either within or outside the corporate network. A web application firewall (WAF) is a subtype of endpoint firewalls. WAFs are used to secure endpoint-hosted applications and web services, such as WordPress, from SQL injections and other malicious attacks.
14. Anti-spyware
Anti-spyware detects, prevents, and removes unwanted software, including adware. While organizations tend to purchase anti-spyware as an add-on module to their anti-virus solutions, standalone software also exists but is generally consumer-grade.
Comparing Endpoint Security Solutions
Evolving to Modern Endpoint Protection
Today, the protection of endpoints is necessary to prevent, contain, mitigate, and remediate external and internal threats. Solutions and strategies must scale to meet the growing diversity of devices, whether on-premises or remote, employee, or vendor. Most importantly, you should build your endpoint security technology stack with solutions that communicate and collaborate with your broader IT and security ecosystem.