What is Digital Identity?
A digital identity is a one-to-one relationship between a human and their digital presence. A digital presence can consist of multiple accounts, credentials, and entitlements associated with an individual. Digital identities note the presence of individuals or entities within applications, networks, on-premises systems, or cloud environments. They may represent a person, organization, application, or device used for authentication, authorization, automation, and even impersonation during runtime. Some refer to a digital identity as a “digital entity” or simply an “identity,” depending on the context.
Digital Identity vs. User
A user refers to the actual person operating a resource to whom the digital identity is assigned. Systems then associate the identity with subsequent activities. Users and digital identities possess a one-to-many relationship regarding accounts.
Identity theft or compromise can have serious implications for individuals and organizations. A compromised identity can potentially allow a criminal to gain access to data, systems, and other resources available to the victim.
Digital privacy is also an important concept to note. It refers to having one’s identity, and personal information related to one’s identity, concealed and only accessible to those authorized by the identity. Data privacy and digital privacy protections are important for protecting identities. Many regulations, such as EU GDPR, HIPAA, etc. have explicit mandates around how organizations collect, transmit, and handle data to protect identities and their personal information.
In this post, we will cover the following:
What are digital identities?
Common use cases for digital identities
Common identity attack vectors and threats
Best practices for safeguarding identities
Major disciplines concerned with identity security
Identity vs. Digital Identity
An identity is generally defined as who you are and the characteristics that distinguish you from others, while the concept of a digital identity is a standardized representation of an individual in a computer resource.
“Identity” in the digital world
An identity in cyberspace is a literal projection of an individual and their interactions within a computer resource.
Identity is typically used to illustrate a one-to-one relationship between a human being and their digital presence. This presence, however, can have multiple accounts, multiple credentials, and an infinite number of entitlements in its electronic format. For example, consider the accounts associated with a user’s enterprise identity.
There may not be a human individual associated with a digital identity. One of these non-human digital identities (NHIs) can represent a defined resource, an asset, or even an automated robot process. This extended definition allows a complete computerized entity to take on a life of its own. Thus, a system can assign it an identity, even though these non-human entities do not “think.”
Some may use "digital identity" and "identity" interchangeably in cyberspace and digital realms, though the correct terminology depends on the context. Identity might be a reference to indicate a broader, all-encompassing definition of a human or non-human object’s presence. However, we can also use it synonymously with a narrowly defined digital identity, such as an account, a password, or another designated user identifier.
Common Types of Digital Identities
Common types of digital identities include:
Human digital identities allow human users to gain access or privileges within a network. Human identities can be further broken down into employee identities, partner identities, vendor identities, and customer identities.
Machine identities (non-human / non-person identities) are a mechanism allowing any non-human entity to be authenticated within systems. These can include applications, software robots, agentic AI, or device identities (server, desktop, IoT, etc.)
Cloud Identities enable users and non-human entities to access resources in the cloud. These identities and accounts can be highly dynamic and may often have some form of privileged access.
Workforce identities encompass employees, contractors, and vendors and are used to perform operations for running an enterprise, agency, or other company.
Customer identities are used to consume a service (usually SaaS) and/or application through a website.
“The implementation of our digital identities in the business world has become an essential prerequisite for doing even the basic tasks in most enterprises. Everything from walking into an office building and scanning a badge, to punching a time clock at a construction site requires identities, access, and privileges.”
Morey J. Haber & Darran Rolls
Digital Identities vs. Accounts: What’s the Difference?
An account is an example of a digital identity, but a digital identity is not always an account. The concept of a digital identity instead represents the presence of a user within a resource—a presence not always associated with an account.
An account, or user account, is used to operate within a computer or network environment. Typically, access to an account requires identity authentication, such as submitting a password or credential.
Accounts often have complex relationships with identities. Systems typically define accounts locally, group them together, or manage them with an identity infrastructure such as directory services. The level of privileges and role-based access depends on the security model of the system implementing them. This may vary significantly from one implementation to the next.
Enterprises can assign a wide variety of identities. Accounts can use a wide variety of techniques to enforce credentials, control entitlement, and govern access. If an unauthorized party compromises a single account, they can use it to steal the entire identity and its privileges. This is especially possible when an unauthorized party compromises an account with administrator access or some other high-level application privilege.
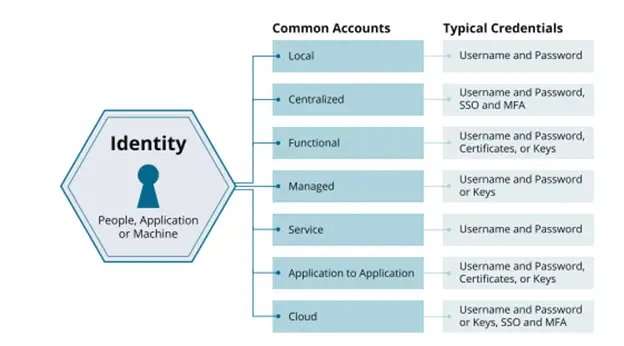
Figure 1: The relationship between identities, accounts, and credentials.(Haber & Rolls, Identity Attack Vectors, 2022)
What are Identity Attributes?
Identity attributes classify ownership and can vary depending on the information collected. Some attributes are static, such as usernames, passwords, or legal names. Others are dynamic, potentially unidentifiable data points, such as browser activity or location data.
Some also refer to identifiable information as “resolvable” data, and unidentifiable information conversely as “non-resolvable.” The attributes contained in an identity allow for attestations, authentication, and authorization of a corresponding account to interact with a resource. Interactive or automated entitlements, permissions, privileges, and rights enable these interactions.
The concept of an "identity" also denotes various aspects for business and personal use, when owned by a human being. These two types of identities should typically never be mixed, especially when using IT resources for one use case or another. In other words, your digital identity when using business applications should be different than when using personal applications. Mixing them increases the likelihood of a breach, malware, or ransomware attack.
Which Types of Digital Identifiers are Used by Digital Identities?
Digital identifiers are data at the root of a digital identity, and different types of digital identifiers are used to attribute behavior on an application, system, or website to an individual, with or without information revealing their real identity.
Digital identifiers can vary depending on the resources being accessed. Within corporate networks and resources, employees will have direct identifiers (names, birthdates, job titles, etc.) used to track their interactions. On the web, browsing data, shopping behavior, and other activities are used to assemble a digital identity—often without the inclusion of any personal identifiers. Rather than leveraging personal information, websites use anonymous identifiers like IP addresses or randomly generated IDs to track activity.
Digital identifiers may include:
Usernames and Passwords: Static identifiers required to log into email, bank accounts, social media, etc.
Birthdates: A common digital identifier used to verify an identity.
Purchase or Search Histories: Browsing and shopping activity tracked and attributed to an individual, then made into a digital identity "profile".
Government-Issued Identifiers: Social security numbers (in the U.S.), driver’s licenses, and other documentation.
Digital Identity Management for Today's Organizations
Today's organizations must deal with an exploding number of digital identities, driven significantly by the need for users to access software-as-a-service (SaaS) and cloud-hosted applications, and the increase in machine identities and third-party resources. These resources exist across the organization, meaning every individual user requiring access will also need a digital account to represent them.
Currently, it is also popular to utilize services like Google, Microsoft, Apple, or Facebook to register and authenticate a digital identity into a third-party resource. This identity is then hosted and managed elsewhere. Real-world use cases include authentication into services like PayPal and Amazon for financial transactions based on attributes stored in the unfederated account. These instances pass identity information from a directory service to a system with no knowledge of, or storage requirements for, the identity being authenticated.
This increase in identities and accounts is ultimately leading to a larger identity attack surface. According to the Identity Defined Security Alliance, 86% of organizations experienced at least one identity-related security incident in the past year.
What are the Risks of Digital Identities?
Digital identities are at risk of identity attacks, which occur when threat actors want to compromise an identity and impersonate it for their own agenda. Their goal is to disrupt the one-to-one relationship of a person to their identity and then compromise the integrity of the identity-to-account relationship. Therefore, the risk surface encompasses all the methods to disrupt these relationships. This threat model applies to both physical and electronic identities.
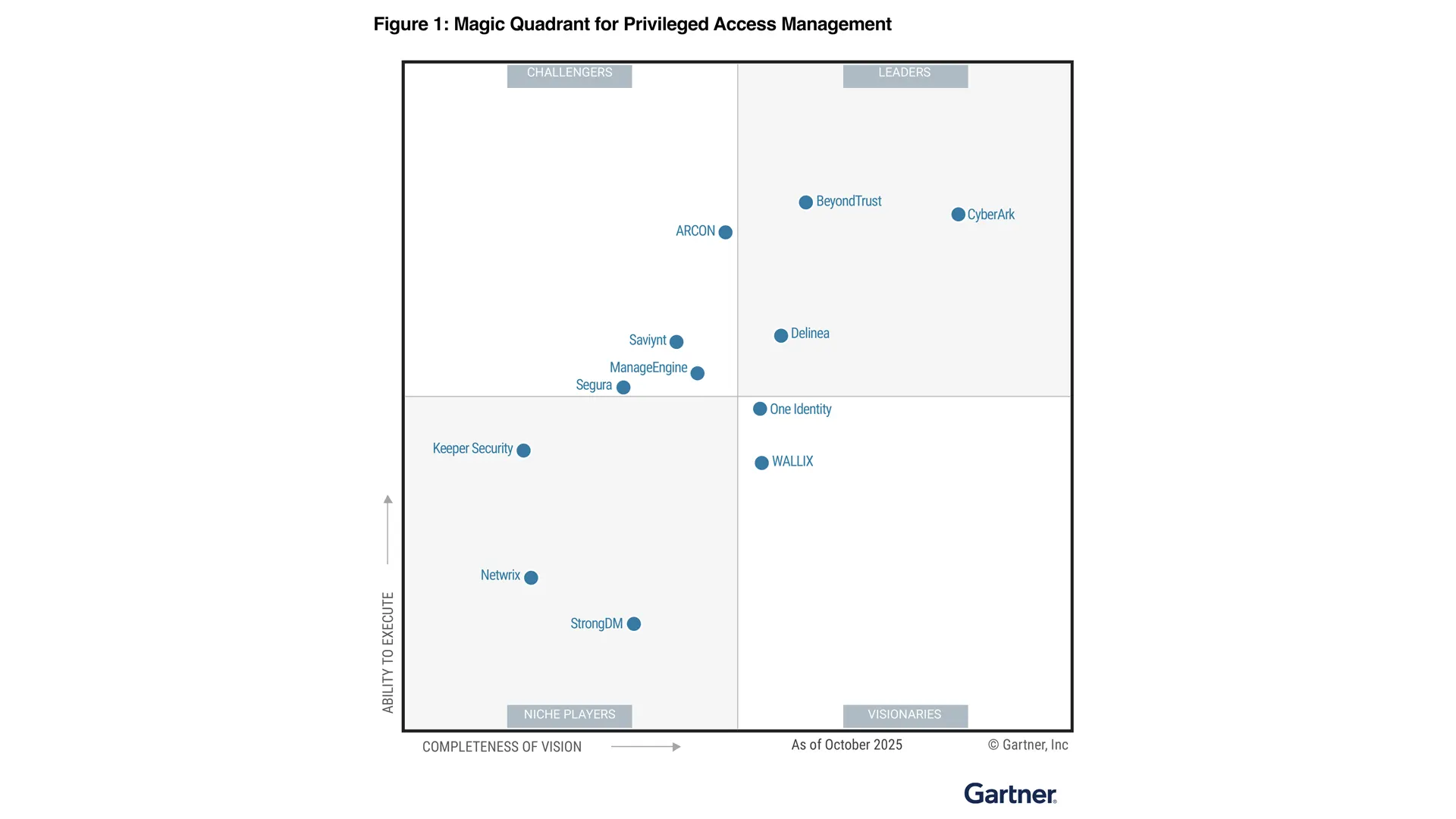
In the context of corporate cybersecurity, privileged identities (identities with elevated access or permissions to corporate resources) are a high-value target for cybercriminals. Non-privileged identities may still possess access to some resources, but are unable to affect change or move between resources like privileged identities can. The discipline of managing these privileged identities is called privileged identity management (PIM), or privileged access management (PAM). PIM/PAM is particularly crucial in the cloud, as cloud identities can blur the distinction between privileged/non-privileged identities.
Common exploit methods include:
Vulnerability Exploits: Flaws or incongruences in software that lead to the exploitation or complete ownership of an account.
Misconfigurations: If configuration hygiene is poor, attacks can find ways to hijack or create accounts from incomplete setup processes.
Privileged Attacks: Password/credential theft, typically due to poor account hygiene, is a common method threat actors use to gain access. Threat actors often seek to exploit privileged access to directly obtain data. Alternately, they execute privilege escalation or lateral movement to amass more access and/or data and to gain control over more accounts.
Social Engineering: Threat actors will exploit trust or other social methods to obtain sensitive information, including identifiers. Phishing is a common social engineering exploit involving email subterfuge.
How to Protect Digital Identities
Organizations can better protect their digital identities with a suite of technologies and tools, including the following:
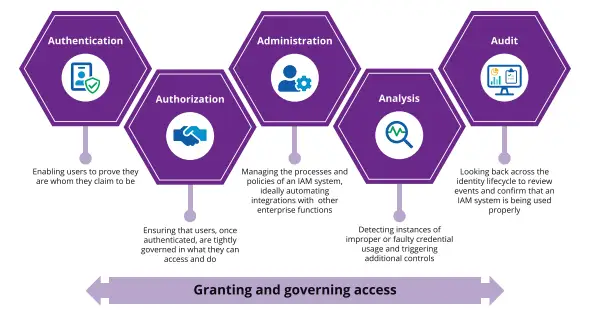
Identity and Access Management (IAM), also known as identity management (IdM), refers to a collection of identity-related enterprise policies and technologies. These IAM practices ensure only the right identities can access the right resources at the right times for the right reasons/context. IAM solutions can enable single-sign-on (SSO) to a range of systems and applications, via streamlined workflows and processes.
The Five Core Tenants of Enterprise IAM (The Five A's) include:
Authentication: Proving users' ownership of a digital identity.
Authorization: Granting limited user access to resources based on governance policy.
Administration: Managing the individual IAM systems themselves.
Analysis: Tracking user behavior and leveraging solutions to detect anomalies, faulty credentials, or other set parameters.
Audit: Maintaining a full audit trail and using it to better understand the health of the IAM program.
Privileged Access Management (PAM) is a critically important and specialized area within IAM. It focuses on controlling and auditing the elevated (privileged) access and permissions across identities, users, accounts, processes, and systems within an IT environment.
Identity Governance and Administration (IGA) is another important identity management concept and deals with the orchestration of digital identity management across an enterprise.
Identity-as-a-Service (IDaaS) refers to IAM services hosted in the cloud.
Identity Threat Detection and Response (ITDR) provides identity insights, threat intelligence, and identity security and management controls across multiple types of toolsets. ITDR proactively prevents identity-based threats and also helps companies pinpoint and mitigate attacks. This approach is crucial for protecting the integrity of identity-based systems themselves.
Identity Security, or identity-based security, encompasses all the above disciplines (IAM, PAM, IGA), and more. Identity security centers on safeguarding digital identities, privileged accounts, and other identity-based entities from cyber threats, both internal and external. Doing so relies on authenticating the identity of individuals as they request access. Within corporate resources, there is significant emphasis on identity verification, authentication, and authorization. In some sectors, security protocols have evolved to incorporate biometric data, such as fingerprinting and facial recognition.
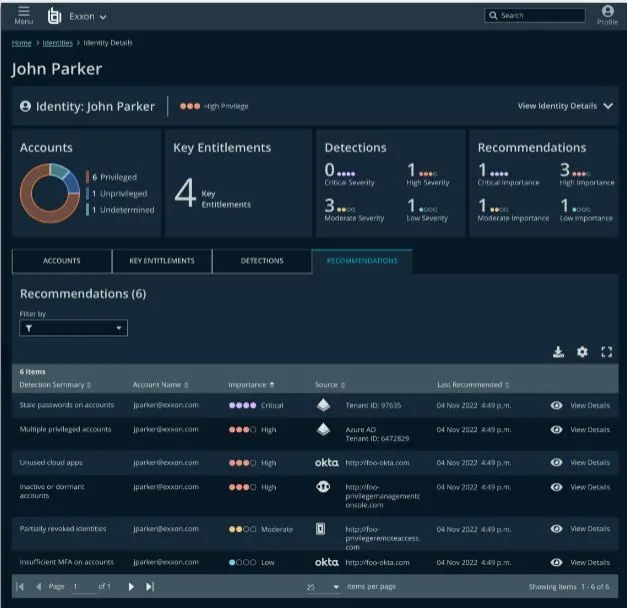
Gain Decisive Control Over Your Identity Attack Surface
Illuminate and harden all identities across Active Directory, Okta, AWS, Ping, and more. Ensure least privilege. Stop-in-progress attacks. Get started now.