Managed security service providers (MSSPs) are IT service businesses that specialize in providing security-as-a-service offerings for their customers. While MSPs (managed services providers) have been around for 25+ years, MSSP practices gained momentum in more recent years.
What’s the Difference Between MSSPs and MSPs?
MSSPs function similarly to MSPs (Managed Service Providers), but are primarily focused on security, while MSPs provide a broader range of IT services and are generally less focused and less specialized with regard to cybersecurity. Additionally, while MSPs frequently establish their own network operation center (NOC) from which they monitor and administer customer operations, MSSPs typically establish a security operations center (SOC), which is responsible for protecting the infrastructure (networks, applications, databases, servers, etc.). Some MSSPs may manage multiple SOCs.
What are the Benefits of Using Managed Security Services?
Managed security services offer the following benefits to customers:
1. Scale up security
2. Layer on the needed expertise where there is an internal IT skills gap
3. Understand the best solutions in the market
4. Apply their know-how of having tackled similar challenges for diverse client environments
5. Increase visibility into threats while expediting a security response (by having visibility into threats across multiple customers, an attack on one customer can allow MSSP adapt security to better protect its other customers)
An MSSP can take over security, step in to fill in-house skills and resources gaps, or provide back-up as needed. Trends such as decentralization, increased remote work, and a prolonged cybersecurity skills gap have all served as catalysts for growing demand for the services of MSSP vendors, in recent years.
What are Managed Security Service Providers (MSSPs) Used for?
Managed Security Service Providers (MSSPs) are used for deploying, configuring, and/or managing the following technologies:
Intrusion prevention systems (IPS)
Web content filtering
Identity access management (IAM)
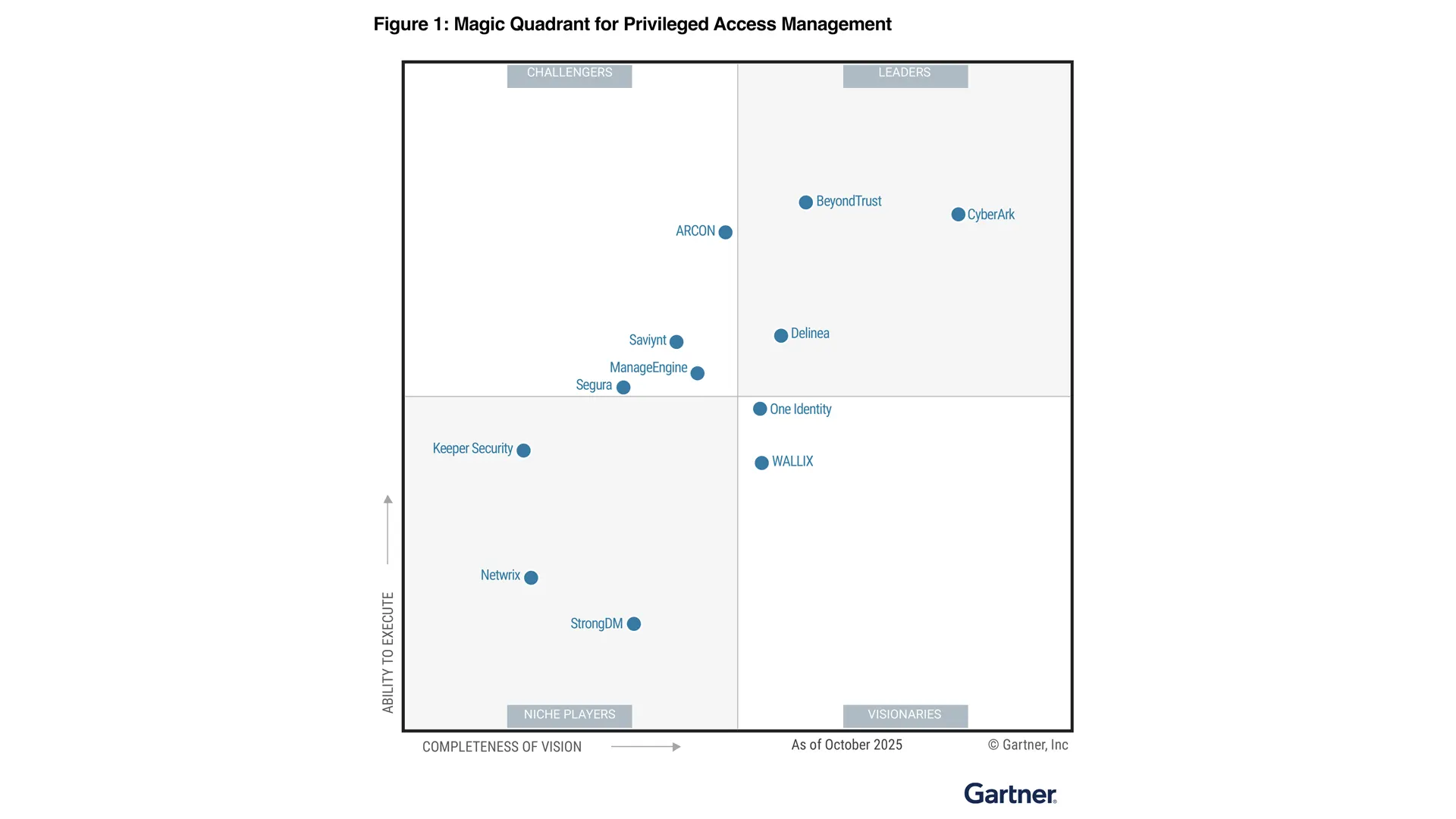
Privileged access management (PAM)
Vulnerability scanning
Patch management
Anti-virus (AV)
Anti-spam
Firewalls (UTMs, NGFWs, etc.)
VPN
Data loss prevention (DLP)
Threat intelligence
What Kinds of Services Do MSSPs Offer?
An MSSP may offer a broad, generalized suite of security capabilities and services, or it may specialize in one or a few core focus areas, such as IAM, privilege management, or threat intelligence. MSSP services may include:
Risk assessments and gap analysis
Policy development and risk management
Solution scoping
Solution/tool research and requisition
Solution implementation
Management of security systems
Configuration management
Security updates
Reporting, auditing, and compliance
Training and education