Secure Every Identity. Across Every Environment.
Apply privilege-centric identity security for every use case, from Agentic AI to Zero Trust.
Contact UsOne Platform. Every Identity.
Every Environment.
You can’t secure connected risk with disconnected tools.
The BeyondTrust Pathfinder Platform unifies PAM, ITDR, Secrets Management, CIEM, and Secure Remote Access—so you can see, understand, and control identities as a single, connected system across every domain.








Secure Every Identity
Human | Non-Human | AI Coworkers & Workloads
Protect Every Environment
Endpoints | Access | Secrets | On-premises | Cloud & SaaS | Identity Infrastructure | OT | Workloads
Identity Intelligence Engine
Reporting | AI Analysis | AI Chat | MCP Integration
Enforce Least Privilege with BeyondTrust Apps
Identity Security Insights® | Entitle | Secure Remote Access | Endpoint Privilege Management | Password Safe®
Validated by Experts,
Celebrated by Customers.
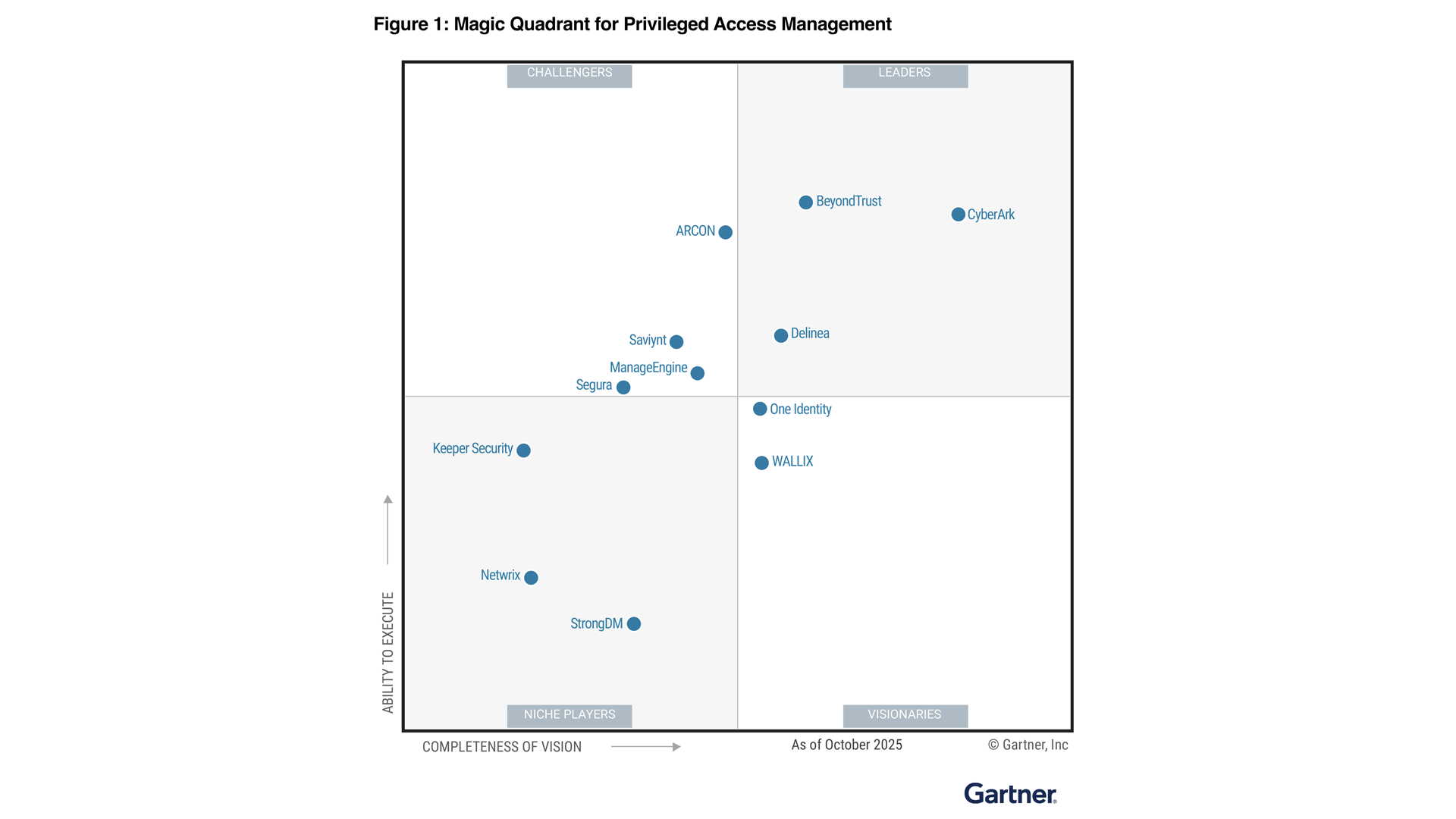
Named a Gartner® Magic Quadrant™ Leader for PAM, a Forrester Wave Leader for PIM, a GigaOm Leader for CIEM, and a KuppingerCole Leader for ITDR. 75% of the Fortune 100 trust BeyondTrust to secure their most sensitive privileges.
Our Ecosystem,
Your Advantage.
Your Advantage.







BeyondTrust integrates with the platforms you already run. Extend privilege controls across your identity, cloud, ITSM—and security stack, without ripping and replacing what works.
Find a PartnerStart seeing privileges clearly—and securing them everywhere.
Contact an expert to get a demo, or for product or pricing details.