What is the Cyber-Attack Chain, or Cyber Kill Chain?
The cyber attack chain (also referred to as the cyber kill chain) shows the steps involved in an external attack on an IT environment. Understanding the cyber-attack chain model can help IT security teams put strategies and technologies in place to “kill” or contain the attack at various stages, and better protect the IT ecosystem.
What is the Sequence of the Cyber Kill Chain Model?
The cyber kill chain model was initially developed by Lockheed Martin, which co-opted the term “kill chain”, used to break down the structure of a military attack (either offensive or defensive) into a sequence composed of identifiable stages.
Lockheed Martin’s cyber kill chain breaks down an external-originating cyberattack into a sequence with 7 distinct steps:
Reconnaissance: Intruder picks a target, researches it, and looks for vulnerabilities
Weaponization: Intruder develops malware designed to exploit the vulnerability
Delivery: Intruder transmits the malware via a phishing email or another medium
Exploitation: The malware begins executing on the target system
Installation: The malware installs a backdoor or other ingress accessible to the attacker
Command and Control: The intruder gains persistent access to the victim’s systems/network
Actions on Objective: Intruder initiates end goal actions, such as data theft, data corruption, or data destruction
While the original cyber kill chain model as envisioned by Lockheed Martin is a helpful starting point in trying to model and defend against attacks, as with any security model, keep in mind that every IT deployment is unique, and intrusion attacks do not, as a rule, have to follow the steps in the model.
Over the years, the attack landscape has shifted, and many have argued that the cyber kill chain, while helpful, needed to be updated to accommodate the reality that the traditional perimeter has shifted—some even say it has, in many cases, vanished.
BeyondTrust's Version of the Cyber Kill Chain Framework
In 2017, BeyondTrust published an updated model of the cyber-attack chain, along with guidance on how to dismantle an attack, each step of the way. Here are the key parts of the BeyondTrust Cyber-Attack Chain model, along with tactics to disrupt the attack at each phase.
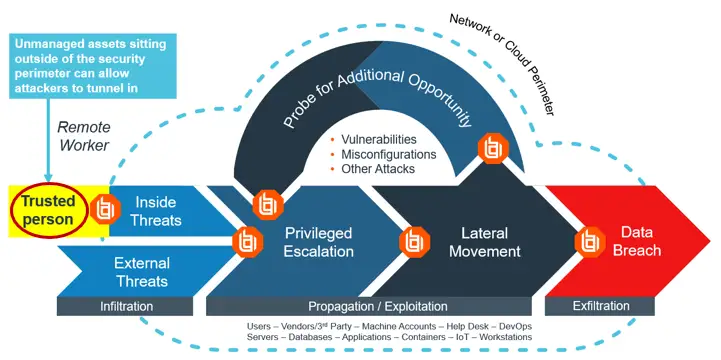
Step One: Perimeter Exploitation
These are the early attempts to gain access to an IT organization's systems and data. Typical techniques include:
Exploiting known vulnerabilities in software and hardware
Social engineering and phishing to gain access to passwords and login information
Malware and downloads that install and grant unauthorized access to the network
Direct hacking—seeking out open ports or other external access points
How to dismantle or contain an attack at this phase:
Identify and remediate vulnerabilities. Numerous security studies have reported that unpatched vulnerabilities are the leading cause of initial exploit. This calls for a thorough vulnerability management program that includes vulnerability scanning and patch management. Pen testing is also a valuable method for proactively identifying risks as a hacker would, to help close any security gaps. Implementing these measure dramatically reduce an organization’s attack surface.
Limit access to sensitive assets. This can be achieved by leveraging vulnerability-based application management (VBAM), which is the capability developed by BeyondTrust to correlate vulnerability data against privileged access requests and permissions, and restrict access based on real-time risk. For instance, if an asset or application has vulnerabilities, you will want to be even more judicious about allowing them to run elevated privileges.
Enforce least privilege: Attackers covet privileges. Often, malicious code and malware cannot execute without a higher level of privileges. By removing admin rights wherever possible and enforcing least privilege, you shrink the available actions that can be performed by an intruder or malicious code.
Step Two: Privilege Hijacking and Escalation
This stage is where an attacker looks to escalate privileges and hijack other privileged passwords/accounts.
How to dismantle or contain an attack at this phase:
Eliminate shared accounts and password sharing. When accounts and passwords are shared, it makes lateral movement and hijacking that much easier. Privileged password management solutions enable organizations to enforce password security best practices, while identifying and eliminating shared accounts and default passwords.
Enforce least privilege. Again, limiting user privileges helps stymie an attacker’s movement at every step.
Monitor and audit all privileged user, session, and file activities. Logging all privileged activity and applying privileged session monitoring and management (which can allow you to pause or kill suspicious sessions), allows you to analyze, alert, report on, and potentially stop any suspicious or unwanted activity.
Step Three: Lateral Movement and Exfiltration
Here, the hacker attempts to move through the system by acquiring more privileges/privileged accounts, and to find other exploits and weaknesses. Ultimately, the intruder zig-zags through the network, user accounts, data, and systems as necessary to achieve their goal(s).
How to dismantle or contain an attack at this phase:
Correlate and analyze user and asset behavior to identify in-process attacks. This step calls on the full integration of privileged access management (PAM) and vulnerability management (VM). The more holistic the threat and behavioral analytics, the more likely you can out-maneuver attackers and stop breaches in their tracks via changing security controls (such as removing rights or access).
How Applying the Cyber Kill Chain Model Improves an Organization’s Security
Although the cyber-attack / cyber kill chains aren’t the only way to understand attack vectors and security risks, these models do provide useful frameworks for reducing cyber exposures. By applying the right layering of cybersecurity controls, organizations can get better at preventing attacks altogether, disrupting in-progress attacks, and minimizing the impact of a breach should one occur.

Evaluate Your Current Security Posture
Use this checklist to measure your current security architecture across all areas of impact and find where gaps might be.