What is IAM (Identity and Access Management)?
IAM (Identity and Access Management), also called identity management, refers to the IT security discipline, framework, and solutions for managing digital identities. Identity management encompasses the provisioning and de-provisioning of identities, securing and authentication of identities, and the authorization to access resources and/or perform certain actions.
Examples of IAM methods include:
Authentication tools such as multi-factor authentication (MFA) and single sign-on (SSO)
Provisioning and deprovisioning processes for onboarding and offboarding employees, assigning levels of access, etc.
Security solutions to ensure that identities are granted the proper level of access and used properly, including privileged access management (PAM)
While a person (user) has only one singular digital identity, they may have many different accounts representing them. Each account can have different access controls, both per resource and per context.
Why Do Organizations Need IAM?
Organizations need IAM because it protects sensitive enterprise systems, assets, and information from unauthorized access or use. An end-to-end IAM implementation will reduce the likelihood and impact of data breaches, and ensure that only legitimate, authenticated users have access. IAM defends an organization’s most critical assets by only allowing authorized access to the following areas:
1. Data and information
IAM aims to prevent unauthorized users from accessing sensitive data related to customers, suppliers, or other proprietary information—whether stored on local servers, in the cloud, or elsewhere. If sensitive data such as personal identifiable information (PII) is exposed, it can cause failure to comply with regulations, loss of reputation, fines, and much more. However, preventing unauthorized data access from occurring in the first place can prevent considerable damage. For instance, a cybercrime group successfully executed a password spray attack on a large software enterprise, due to a lack of proper IAM controls, such as multi-factor authentication and strong password practices, among other issues. The group was ultimately able to exfiltrate proprietary data such as emails and attachments. The likelihood and severity of this data breach would have been lessened with proper IAM controls across the attack chain.
2. Software and applications
IAM also protects systems used by employees, customers, suppliers, partner businesses, etc., from unauthorized access. In the wrong hands, a company’s software and applications can cause considerable damage. For example, an authentication flaw in a file transfer system led to damage that affected an estimated 8,000 organizations, exposing data from large financial institutions, healthcare firms, government agencies, and more.
3. Development, testing, staging, and operational platforms
Additionally, IAM ensures all IT environments used for product and service development, launch, and operations, are secured from unauthorized use. If a bad actor is able to access these development environments, they can then look for ways to move laterally into other accessible systems, tamper with the software in development, exfiltrate secrets and credentials hardcoded within the CI/CD pipeline, and much more.
4. Devices
Laptops, desktops, smartphones, tablets, IoT, and other devices also require strong IAM controls. If not secured properly, they can become an entry point for attackers to reach other areas of the environment or launch an attack. As an example, the notorious NotPetya malware attacks in 2017 first gained a foothold with a user’s stolen Windows credentials. From there, the malware could spread via legitimate systems within the target system, such as Windows Management Instrumentation Command Line (WMIC), Microsoft SysInternals utility, etc. This malware encrypted files, even deeming entire computers unusable in some cases. As we can see, secure IAM controls are vital to protecting endpoints from threats.
5. Locations
Business locations, including private office spaces, data centers, and device storage areas, should be secured with IAM controls as well. Examples of IAM for physical locations include checkpoints where employees must scan their badges or provide biometrics, an audit of activity at all access points, and restrictions such as time limits / geofencing to ensure that employees and visitors do not enter restricted areas unless required of their role.
6. Integrations
IAM controls are also needed to secure integrations, securing data as it is transmitted, received, or stored between different areas. Without proper IAM controls over integrations, organizations can be more susceptible to supply chain attacks, such as the SolarWinds hack that compromised the data, networks, and systems of thousands of public and private organizations.
Key IAM Functions and Policies
IAM includes several types of functions and policies that ensure users have the access they need, and that systems, data, and applications are inaccessible to unauthorized users. Here are a few examples of key activities an IAM system should perform:
Recording, capturing, and authenticating user login information (usernames, passwords, certificates, etc.)
Defining the correct levels of protection and access for sensitive data, systems, information, and locations
Managing the employee database of users and job roles, including how users are identified and the roles they are assigned
Allowing for addition, deletion, and change of individuals and each role’s access rights
Providing a history of login and systems access for audit purposes
Allowing for properly segmented definitions and access controls for every part of the business systems and data
Tracking and reporting on user activities across all systems and data
Enforcing access policies across the systems, information, and other areas protected by IAM
How Do IAM Technologies Work?
IAM technologies work by using a central directory of users, roles, and predefined permission levels to grant access rights to individuals. It assigns these access rights based on which systems, applications, and data are needed for each user to perform their role. There is a wide variety of IAM tools available on the market. Some are centralized platform options that offer access and sign-on functionality in a single solution, while others complement and integrate with existing access and sign-on tools.
IAM Role-Based Access Control Examples
Most IAM software uses role-based access control (RBAC): controlling access to systems and information via predefined roles and responsibilities rather than requiring IT teams to assign individual permissions manually. As users join or change roles in the enterprise, their job role is updated. RBAC then ensures that their access rights are automatically modified to match the new role. However, exceptions can be granted if certain users require special access outside their defined role.
Here is an example of how RBAC operates within an HR department, granting access to different levels of systems and employee data based on each role’s responsibilities:
Identity and Access Management (IAM)
Business Role | Task | Contact Details | Benefits Data | Salary Data | Performance Data |
|---|---|---|---|---|---|
HR Benefits Administrator | Manage employment benefits | Yes | Yes | No | No |
HR Payroll Administrator | Manage payroll and salary | Yes | Yes | Yes | No |
HR Talent Management | Manage training and promotions | Yes | No | Yes | Yes |
Using IAM for Granular Access Enforcement
Sophisticated IAM technology can move beyond simply allowing or blocking access to data and systems. There are many ways to implement IAM policies that precisely define and enforce how individuals access systems and data based on a company’s specific needs. A few examples of granular access enforcement for IAM include:
Restricting access to subsets of data: Specific roles can only access certain subsets of systems, databases, and information.
Only allowing view access: Specific roles can only view data—they cannot add, update, or amend it.
Only permitting access on certain platforms: Some roles may have access to operational systems, but not development or testing platforms.
Only allowing access to create, amend, or delete data—not to transmit it: Some roles may not be able to send or receive data outside the system, meaning it cannot be exposed to other third parties and applications.
Common IAM Tools and Capabilities
Identity access and management tools offer a variety of capabilities, focused on authentication, authorization, and other key processes related to how users access resources across the organization. A few common capabilities included in an IAM system out of the box include:
Centralization of employee data—such as through an HR system, directories (i.e. Active Directory), and more—to define and identify individual users
Tools to add, modify, and delete users
Password management tools and workflows
Integration with or replacement of existing login system(s)
Enforcement of user access rights to certain systems and information
Auditing and reporting for visibility into how systems and information are being used
IAM Solutions and System Examples
There are many technologies to simplify password management and other aspects of IAM. A few common types of solutions that are used as part of an IAM program include:
Single Sign On (SSO): An access and login system that allows users to authenticate themselves once and then grants them access to all the software, systems, and data they need without having to log into each of those areas individually.
Multi-Factor Authentication: This system uses a combination of something the user knows (e.g., a password), something the user has (e.g., a security token), and something the user is (e.g., a fingerprint) to authenticate individuals and grant them access.
Identity Management System: These systems control how user identities are created, maintained, and deleted across the organization, enabling administrators to view and manage access roles and rights from a central platform.
Cloud Infrastructure Entitlement Management (CIEM): The solutions automatically discover and manage cloud permissions and entitlements across multiple cloud platforms such as AWS, Azure, and Google Cloud. CIEM products offer a centralized view into complex, multicloud infrastructure, enabling teams to break down siloes and right-size access to cloud resources across the enterprise.
Identity Governance and Administration (IGA): This discipline includes policies, processes, and technologies for managing how digital identities access organizational resources. IGA solutions provide automated provisioning/deprovisioning for identities and accounts throughout the identity lifecycle.
Customer Identity and Access Management (CIAM): These solutions enable customers to interface with public-facing online services and applications and make updates to their own account and its privacy settings. CIAM products also offer strong security controls that minimize threats such as identity theft, data exfiltration, etc., and adhere to key frameworks related to data privacy such as GDPR.
Privileged Access Management (PAM): This the largest subdiscipline of IAM and entails the practices and technologies for managing, controlling, and auditing privileged accounts / credentials, secrets, and more. PAM tools are essential for implementing least privilege across an organizations, and play a critical role in minimizing the attack surface and blast radius of attacks.
IAM technology can be provided on-premises, through a cloud-based model (i.e. identity-as-a-service, or IDaaS), or via a hybrid cloud setup. Practical applications of IAM, and how it is implemented, differ from organization to organization, and is also shaped by applicable regulatory and compliance initiatives.
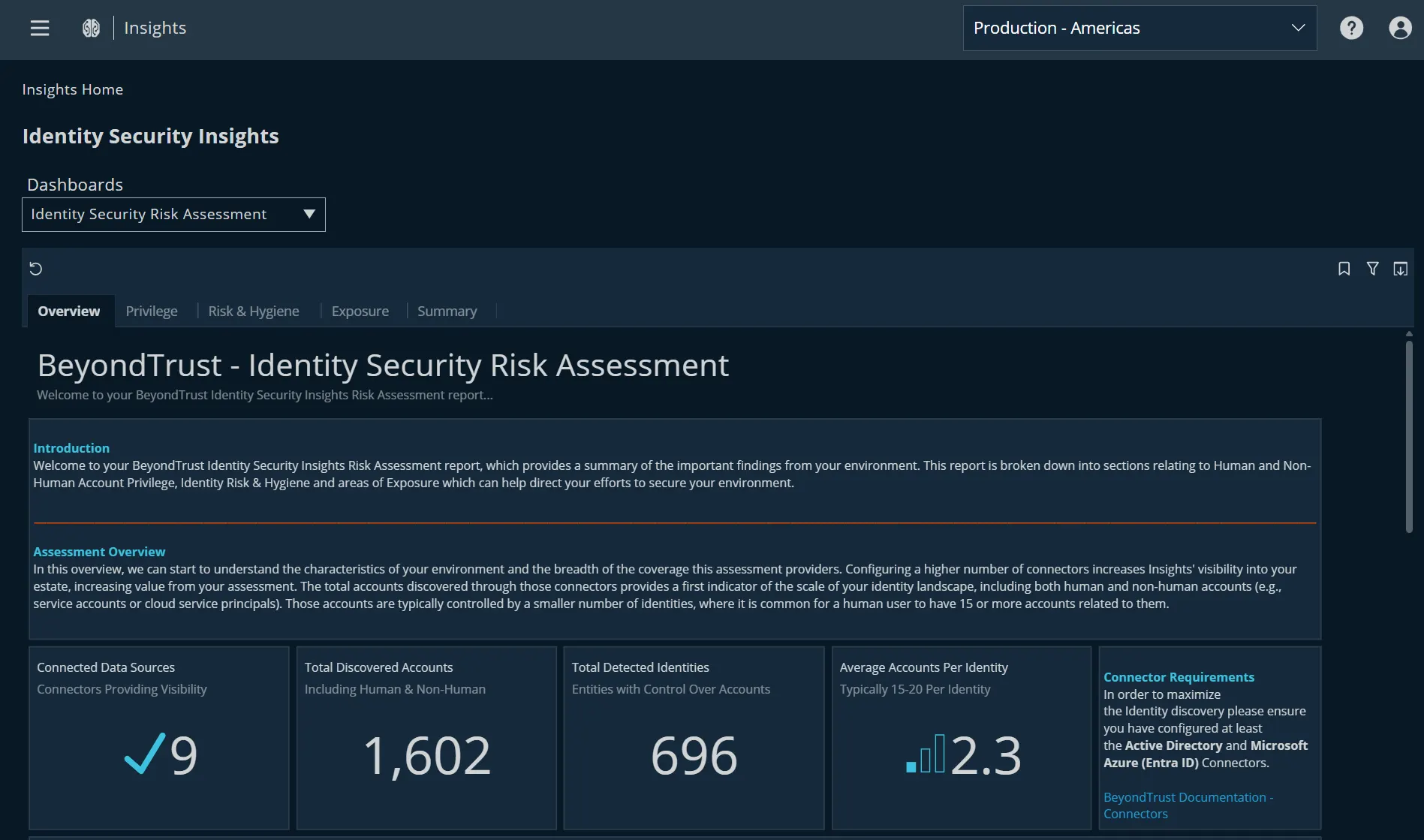
Get a Free Identity Security Risk Assessment to Reveal IAM Gaps
Are there gaps in your existing IAM strategy? Find out with a full view of the identities and privileges across your connected systems.
Integrating IAM and PAM for Comprehensive Access Management
While some folks treat privileged identity management (PIM)—also called privileged access management (PAM) or just privilege management—as a sub-category within IAM, others consider PAM its own entity. Nevertheless, for holistic identity governance that controls both non-privileged and privileged identities, IAM and PAM both need to be mature programs that work and communicate with each other.
While IAM enables organizations to provision/de-provision identities, authenticate them, and authorize their access to resources and certain actions, it lacks the ability to layer on granular controls (such as enforcing the security principle of least privilege) for privileged identities and privileged access and permissions.
With an IAM solution alone, permissions and privileges are generally granted in broad strokes to far too many people, accounts, applications, etc. So, while IAM solutions allow IT teams to address ‘who has access to what?’, PIM/PAM solutions must be layered on to address such questions as “is that the appropriate amount of access?”, and “are those privileged activities appropriate?“
Privilege misuse or abuse is recognized to be a key ingredient of many security breaches. For numerous years in a row, BeyondTrust’s annual Microsoft Vulnerability reports consistently uncovered that 75% of Critical Microsoft vulnerabilities could have been mitigated by removing admin rights. As such, integrating the critical PAM piece with an IAM implementation is essential. The higher the degree of the integration between identity and access management with privilege management, the more streamlined the control and auditing over all privileged and non-privileged accounts and access.
Identity and Access Management Next Steps
IAM is a central practice for protecting sensitive business data and systems. Implemented well, IAM provides confidence that only authorized, authenticated users can interact with the systems and data they need to effectively perform their job roles.
While any IAM implementation will start with an audit of an organization’s needs (defining roles, access requirements, etc.) and the creation of a policy, there are many different IAM tools and solutions that can help you execute on an IAM program. Any tools you select should meet the use cases for your environment.
Also consider prioritizing tools that provide highly automated workflows to simplify IAM administration, as well as identity management tools that integrate well with other systems and security technologies (such as PAM). The more seamless the tool fits within your existing environment and tech stack, the more likely you are to close security gaps and improve business operations.
Discover additional resources and research about identity security and IAM.