Find, Control, & Protect Paths to Privilege™
Gain visibility and control over privileged identities, accounts, access, and privilege pathways across your environment - with one, integrated platform. Simplify deployments, reduce costs, improve usability, and supercharge your existing investments with the deepest set of privileged access management (PAM) and identity security capabilities.
BeyondTrust Solution Use Cases
BeyondTrust Identity Security and Privileged Access Management (PAM) solutions are deployed to satisfy a variety of security, service desk, compliance, and industry-specific use cases.

AI Identity & Privilege Security
AI Security Posture Management
Cloud Access
Cloud Infrastructure Entitlement Management (CIEM)

Cyber Insurance

Digital Transformation

Endpoint Security

Enterprise Password Management

Identity Threat Detection & Response (ITDR)

Machine Identity Management & Security

Modern PAM

Operational Technology

Service Desk Efficiency
BeyondTrust Industry Applications
BeyondTrust Privileged Access Management solutions are used to meet a broad array of compliance requirements, regulations, and industry-targeted cyberattacks.

Law Enforcement
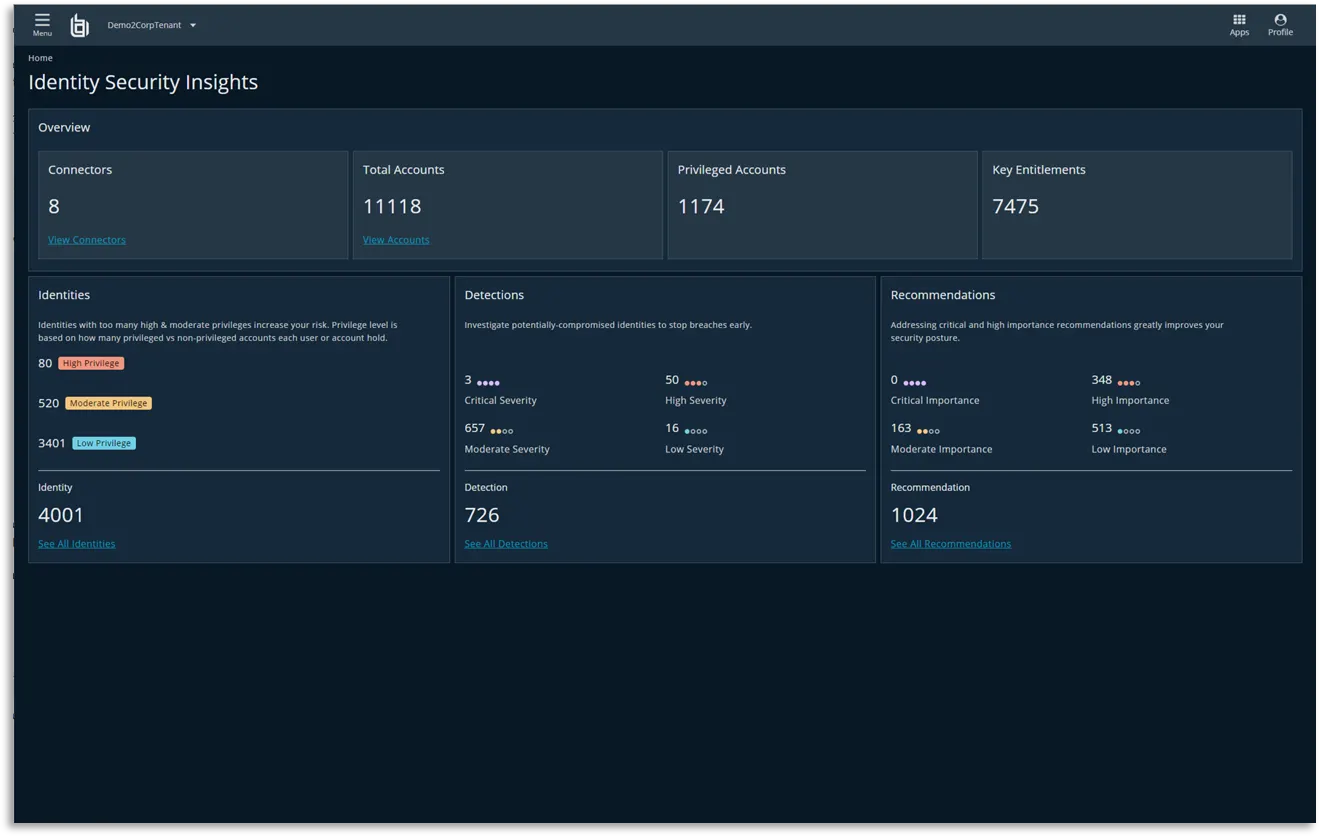
Know Your Identity Attack Surface Inside & Out.
Illuminate Identity-Based Vulnerabilities Across Your Environment
Reveal identity misconfigurations, overprivileged accounts, orphaned accounts, and other Paths to Privilege. Get a free identity security assessment and 30-days continuous identity threat monitoring.
Integration Highlight: ServiceNow
Supercharge ServiceNow ITSM and CSM Workflows
Centralize and improve support by leveraging BeyondTrust's integrations with ServiceNow ITSM and CSM.
Request a Demo

PAM & Identity Security Solutions
Find and protect Paths to Privilege across your enterprise. Sign up to schedule a demo of BeyondTrust.