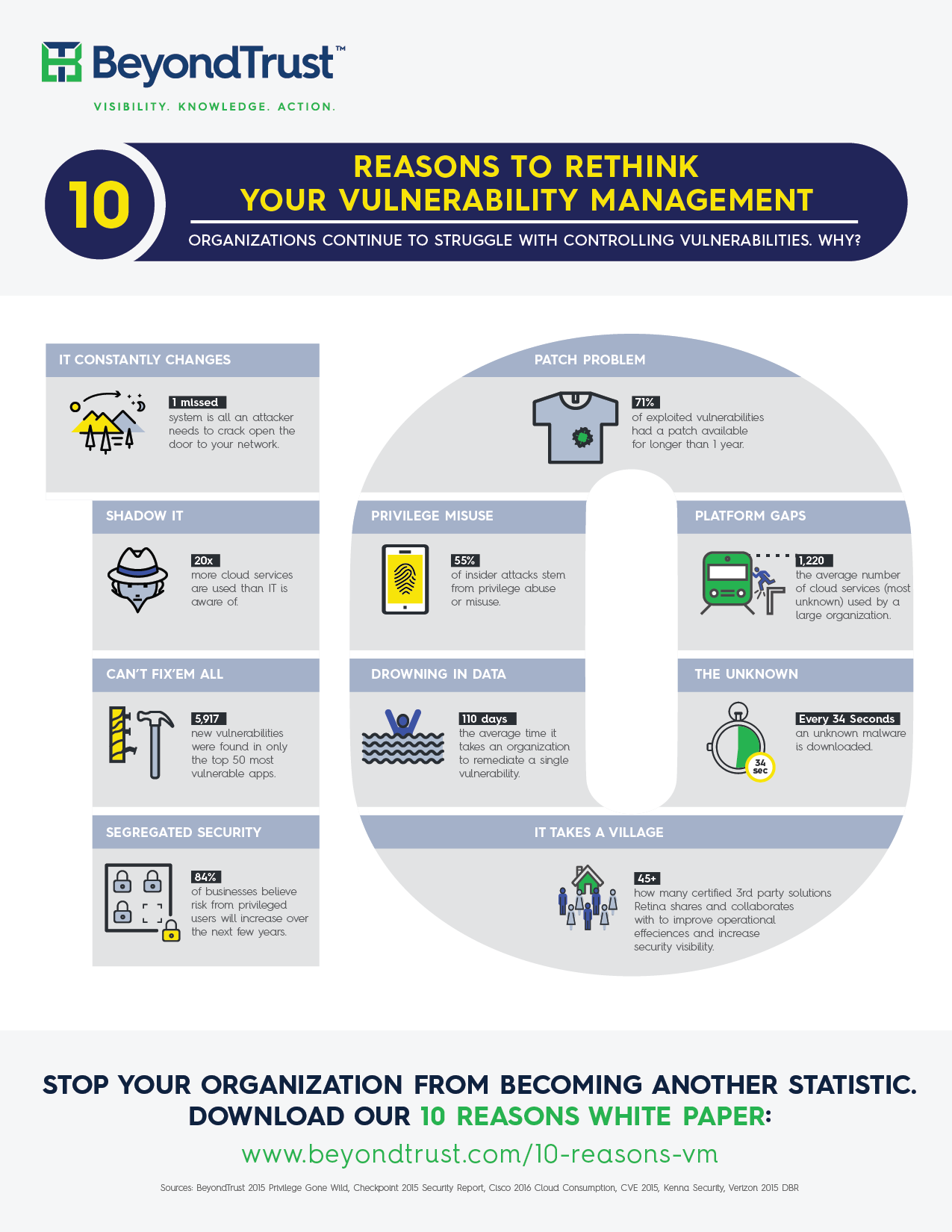
 Vulnerability management is a foundational component in our ongoing war against cyber terrorism. When working properly it can help us discover what’s connected to our networks, put context around what systems and applications are most at risk, eliminate and track threats over time, and communicate our progress to varied stakeholders across our organizations. Are you getting the most out of your vulnerability management program? If not, it’s time to rethink what you’re doing.
Need help? Download our latest white paper, 10 Reasons to Rethink Your Vulnerability Management, and see how Retina’s cutting-edge capabilities can keep you steps ahead of the bad guys.
For more, contact us today!
Vulnerability management is a foundational component in our ongoing war against cyber terrorism. When working properly it can help us discover what’s connected to our networks, put context around what systems and applications are most at risk, eliminate and track threats over time, and communicate our progress to varied stakeholders across our organizations. Are you getting the most out of your vulnerability management program? If not, it’s time to rethink what you’re doing.
Need help? Download our latest white paper, 10 Reasons to Rethink Your Vulnerability Management, and see how Retina’s cutting-edge capabilities can keep you steps ahead of the bad guys.
For more, contact us today!

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








