The Qualys research team has discovered a heap overflow vulnerability, CVE-2021-3156, in sudo that allows any unprivileged user to gain root privileges on Linux without requiring a password. Even a user “nobody” can get root access to a Linux server without a password.
The CVE-2021-3156 vulnerability, introduced in 2011, was fixed in the latest version, sudo 9.5p2, and released on January 26, 2021.
Some key findings on the vulnerability:
- The exploit has been hiding in plain sight for nearly 10 years
- The exploit allows any Linux user to gain root access without a password
- The researcher was able to develop 3 different exploits for this vulnerability and obtain root access on Ubuntu, Debian, and Fedora using various versions of sudo
- Other OS’s and distros are probably at risk
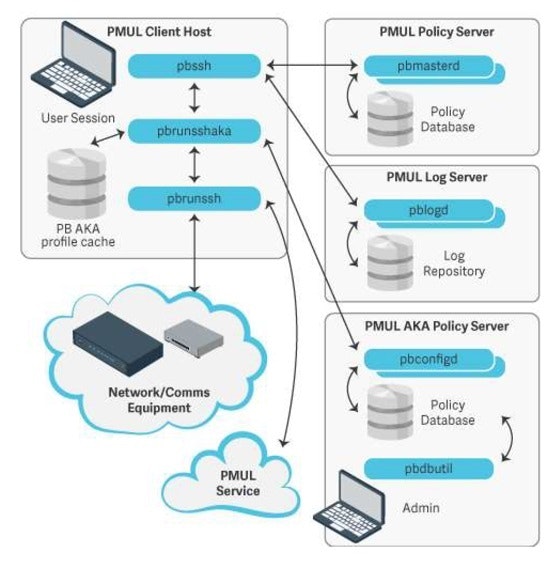
BeyondTrust strongly encourages Privilege Management for Unix & Linux (PMUL) customers to run pbrun instead of sudo. Pbrun is a command in PMUL that elevates the rights of a standard user so they can run a command as a privileged user, but without needing a root account. Sudo is a basic tool that does a similar function, but with limited capabilities.
The major difference is that BeyondTrust pbrun is distributed with every instance of our Privilege Management for Unix & Linux solution, whereas sudo is open-source and is distributed with every version of Linux. Learn more about sudo in this blog from security expert, Derek A. Smith.
BeyondTrust has assessed the risk of this bug and confirmed that Privilege Management for Unix & Linux is not at risk since the product does not leverage sudo to elevate privileges.
How to Eliminate the Risk of Sudo Vulnerability CVE-2021-3156
Privilege Management for Unix & Linux customers can remove the risk of CVE-2021-3156 if they take the following steps:
- Delete sudo and sudoedit binaries from your Linux servers, if you are not using sudo
- Use pbrun, rather than sudo
- Upgrade to the latest version of sudo v1.9.5p2, if you are still using sudo in addition to the BeyondTrust solution
For those Linux users who are not using Privilege Management for Unix & LInux, we suggest the following:
- Delete sudo and sudoedit binaries from your Linux servers, if it’s not being used
- Follow the technical advisories provided by your OS vendor, example here
- Consider using BeyondTrust Privelege Management for Unix & Linux to elevate privileges across your estate, instead of sudo
Understanding the Limitations of Sudo
While sudo has its merits and use cases, larger and more complex organizations will be familiar with its many limitations. For instance:
- Sudo does not provide efficient centralized administration and management
- Sudo does not have advanced reporting and analytics for a comprehensive audit trail
- Sudo is complex to manage in large enterprises
- Sudo does not provide centralized identity and group management
While some organizations who have outgrown sudo will try to make it work by layering on capabilities from privilege management solutions, others look to replace it entirely. BeyondTrust can help organizations with both of these scenarios.
Why Security-Conscious Enterprises Replace Sudo with BeyondTrust Privilege Management for Unix & Linux
Designed to help enterprises mitigate threats against Unix and Linux, BeyondTrust Privilege Management for Unix & Linux is an advanced enterprise product that empowers the move to the cloud. The solution offers many key advantages over sudo, enabling enterprises to:
- Gain clear, unobstructed visibility and a comprehensive audit trail of everything that happens in their cloud and on-premise environments, including centralized keystroke logs, session recordings, and all other privileged events
- Scale without limits; BeyondTrust’s largest deployment involves an enterprise using our solution to secure more than 130,000 endpoints, protecting and giving visibility to their SaaS infrastructure
- Centralize identity and group management with Active Directory Bridging and avoid the hassle of managing and auditing shared or local accounts
- Configure the solution to fit any business environment or vertical, including healthcare, retail, finance, legal, energy, and cloud
- Integrate BeyondTrust Privilege Management for Unix & Linux with existing password management solutions
- Send information from every event to Splunk or other security information and event management (SIEM) solutions
- Monitor file and policy integrity, making it easier to pinpoint, audit, and reverse (if unwanted) changes to critical policy, system, application, and data files
To learn more about Privilege Management for Unix & Linux, contact us today.
If you are a PBsudo/PMUL Basic customer, please contact Support.
Learn more about Solving Your Unix/Linux Security & Administration Challenges

Colin Bretagne, Senior Product Manager
Originally from South Africa, Colin has worked and lived in 3 countries. Through his career, he has worked his way from a Support Engineer to a Technical Manager, before arriving in Montreal Canada in 2009. Colin has extensive experience in hardware and software and has achieved certifications in HP, Novell, Microsoft, Linux, and Pragmatic Marketing. In his spare time, Colin enjoys Rugby, Judo, and is a qualified FA Soccer referee.










