Linux today makes up roughly 85% of the server market in public-facing sites and it’s the standard for all cloud environments hosting mission critical data and systems. Many organizations adopt risky day-to-day practices with their Linux endpoints that expose them to cyberthreats from external attackers and insiders.
Credential sharing, root abuse or misuse, inconsistent manual processes, overreliance on open-source tools to manage systems, excessive rights, and limited visibility into privileged account use are all common practices that increase an organization’s exposure to risk from both cyberthreats and non-compliance.
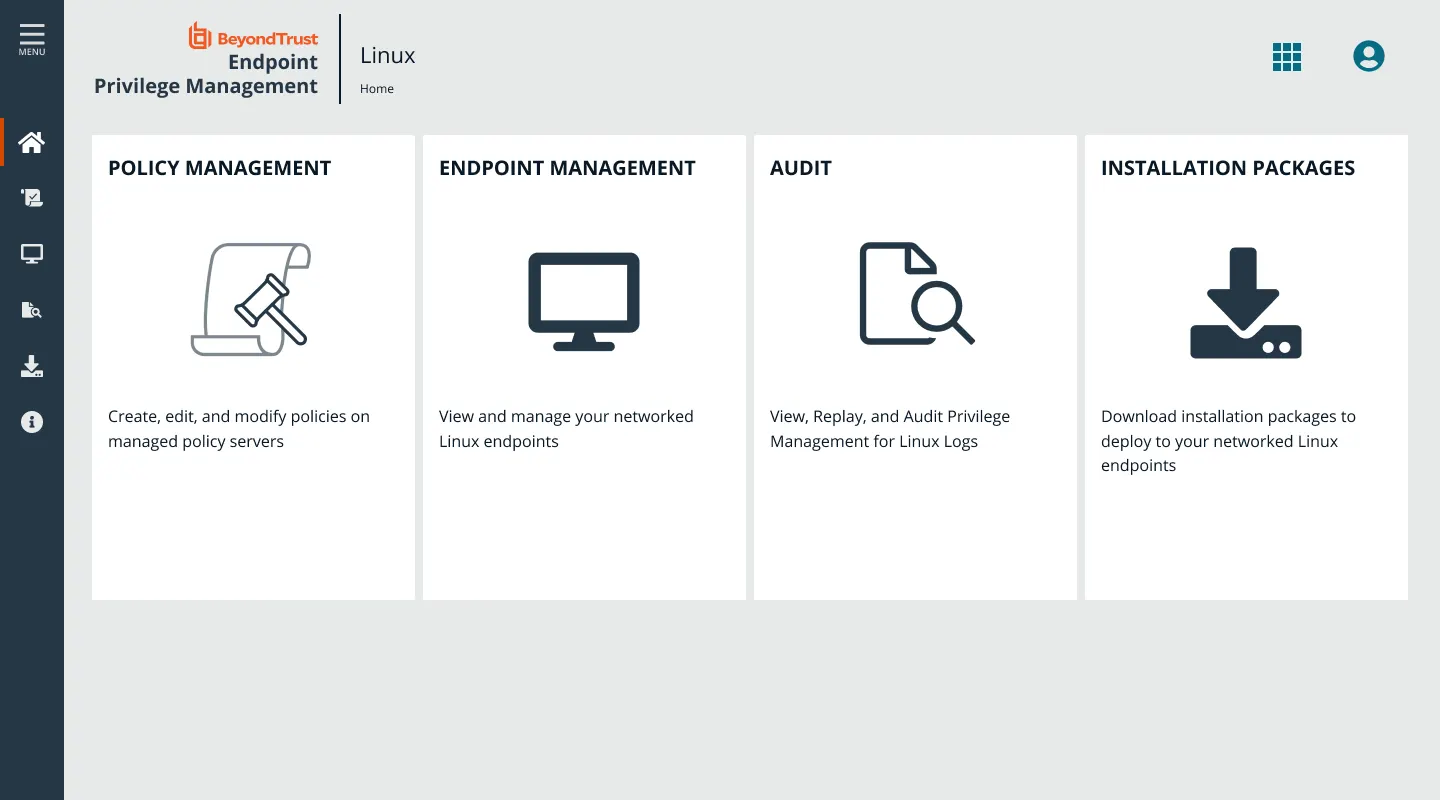
Endpoint Privilege Management enables you to intelligently manage and control privileges across your Linux estate, putting an end to credential sharing, root abuse/misuse, and excessive rights. With fine-grained visibility into all your user activity and centralized management, you can monitor privilege elevation and streamline oversight of your estate.