
“Your Session has Been Locked”
Imagine if you were responsible for the oversight of all privileged sessions, but you could only view them. Or worse, what if you spotted suspicious or detrimental session activity and had the ability to kill the session, but doing so meant that your valid RDP or SSH sessions were killed in the process, leaving other scripts and your IT environment corrupted? What would you do?
Privileged session management is one of many capabilities in the PowerBroker Privileged Access Management Platform. To read more about what use cases our solution can help you solve, check out our technical solutions guide. Download now
When Just Monitoring Isn’t Enough
Monitoring privileged sessions has become an increasingly important function of IT security administrators. But monitoring is not enough. Forrester estimates that 80% of security breaches involve privileged credentials. While most organizations with a privileged access management solution in place have some form of privileged session monitoring, limited functionality leaves IT security admins fighting with their hands tied.
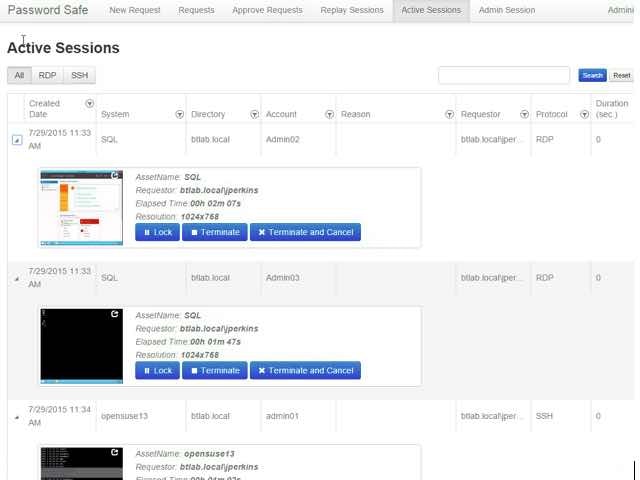
Good privileged session management solutions should allow IT security pros to monitor, record, pause, lock, and terminate a privileged session— in real time.
BeyondTrust’s PowerBroker Password Safe gives IT security managers the ability to safely lock a session without causing collateral damage. Password Safe gives the manager an opportunity to determine whether suspicious or malicious activity has taken place. If the activity is determined to be approved, the security manager simply selects an unlock option to allow the user to resume their session.
With Password Safe, IT security administrators can:
- Request RDP/SSH access to authorized systems only
- Start sessions instantly, or via workflow
- View any active privileged session, and if required, pause or terminate the session
- Use keystroke indexing and full text search to pinpoint data, and then log an acknowledgement of the review for audit purposes
- Avoid Java – Password Safe is a client-less solution with no agents required on the server
- Fully integrate with native tools (MSTSC, PuTTY, etc.)
- Gain full video recording with 100% accountability
Privileged session management is one of many capabilities in the PowerBroker Privileged Access Management Platform. To read more about what use cases our solution can help you solve, check out our technical solutions guide.

Sandi Green, Product Marketing Manager, BeyondTrust
Sandi Green is the Product Marketing Manager for PowerBroker Password Safe, PowerBroker for Windows, and PowerBroker Mac at BeyondTrust. She has over 20 years of sales and solutions marketing experience with technology companies that served a variety of industries ranging from life sciences, human capital management, consumer packaged goods and most recently IT security. When she’s not following the latest trends in Cybersecurity, she’s busy following college football and basketball. Follow her on Twitter at @SandiGreen3.








