 Here is the flaw: Even if the password is rotated frequently or given for one-time usage it is still exposed to the end user. There is a finite amount of time it can be abused. So how can a secure password management system obfuscate the username and the password to make it completely transparent to the end user? Until now, there has been no solution to mitigate this risk.
PowerBroker Password Safe provides a high-availability solution based on the BeyondInsight IT Risk Management Platform. It automatically stores and rotates passwords for Windows, UNIX, Linux, Databases, and Network Devices. With granular role based access, password policies, session recording, auditing, workflow, and self-service password checkout capabilities, the solution is leading the industry in innovative enterprise password management.
PowerBroker for Windows is a least-privilege solution for Microsoft Windows. It allows for the removal of administrator rights using patented technology to swap the security token of the application, not the user, to elevate the task at hand. This eliminates the need for administrative credentials for most applications (not all) on desktops and servers.
With the release PowerBroker Password Safe 5.4.1, and PowerBroker for Windows 6.7, the need to checkout passwords from Password Safe and paste them into Windows applications using a “Run As” has been completely eliminated. This ground breaking technology removes the entire workflow of checking out a password, coping it to a clipboard (or even writing it down), and entering it into an application for privileged execution.
How Does It Work?
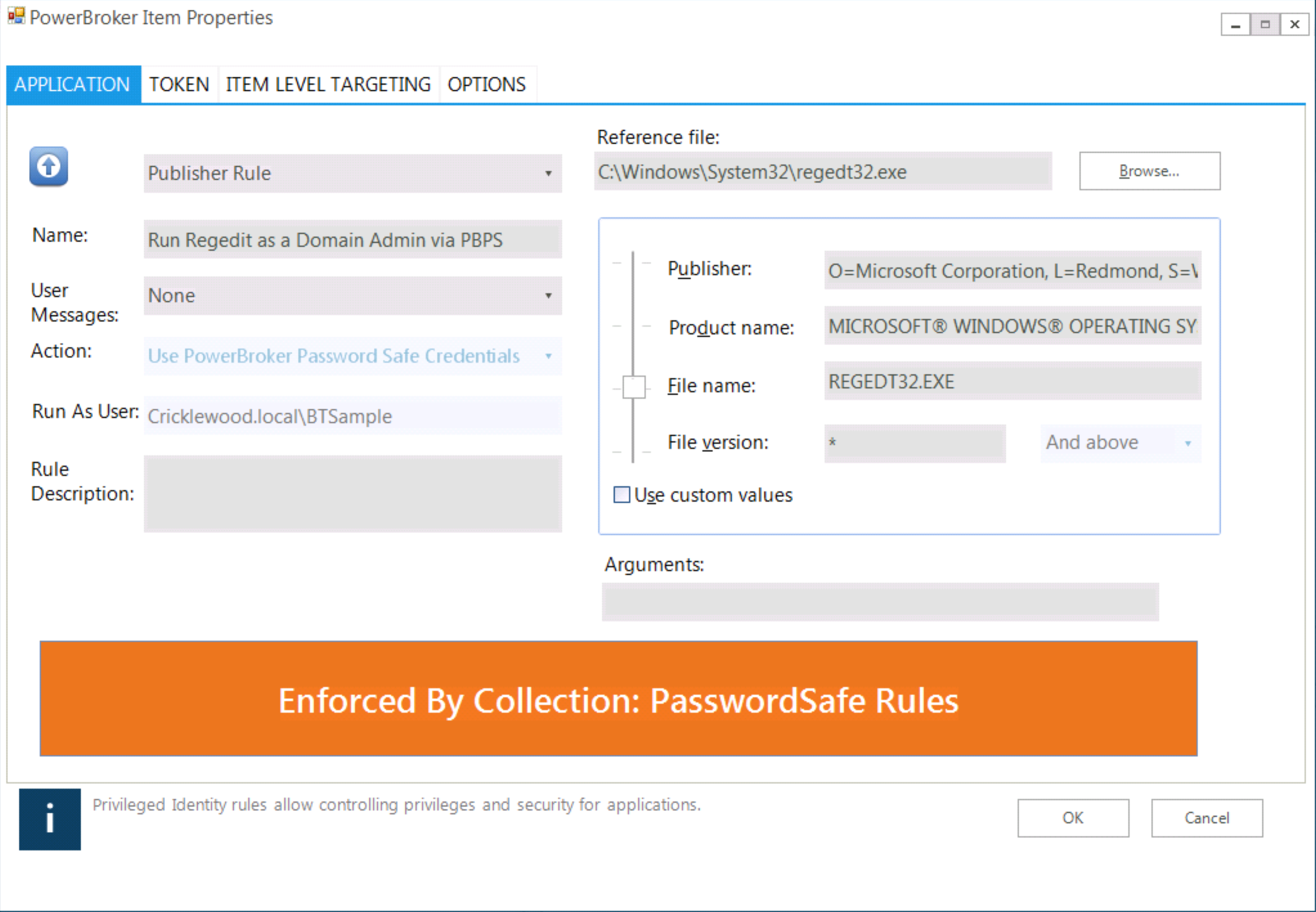
PowerBroker for Windows 6.7 has a brand new action type that allows for the specification of PowerBroker Password Safe as the valid credential type. When a rule is matched (like for Regedit.exe below) the username specified is automatically transmitted to Password Safe and the current managed password automatically sent back to the PowerBroker for Windows agent.
Here is the flaw: Even if the password is rotated frequently or given for one-time usage it is still exposed to the end user. There is a finite amount of time it can be abused. So how can a secure password management system obfuscate the username and the password to make it completely transparent to the end user? Until now, there has been no solution to mitigate this risk.
PowerBroker Password Safe provides a high-availability solution based on the BeyondInsight IT Risk Management Platform. It automatically stores and rotates passwords for Windows, UNIX, Linux, Databases, and Network Devices. With granular role based access, password policies, session recording, auditing, workflow, and self-service password checkout capabilities, the solution is leading the industry in innovative enterprise password management.
PowerBroker for Windows is a least-privilege solution for Microsoft Windows. It allows for the removal of administrator rights using patented technology to swap the security token of the application, not the user, to elevate the task at hand. This eliminates the need for administrative credentials for most applications (not all) on desktops and servers.
With the release PowerBroker Password Safe 5.4.1, and PowerBroker for Windows 6.7, the need to checkout passwords from Password Safe and paste them into Windows applications using a “Run As” has been completely eliminated. This ground breaking technology removes the entire workflow of checking out a password, coping it to a clipboard (or even writing it down), and entering it into an application for privileged execution.
How Does It Work?
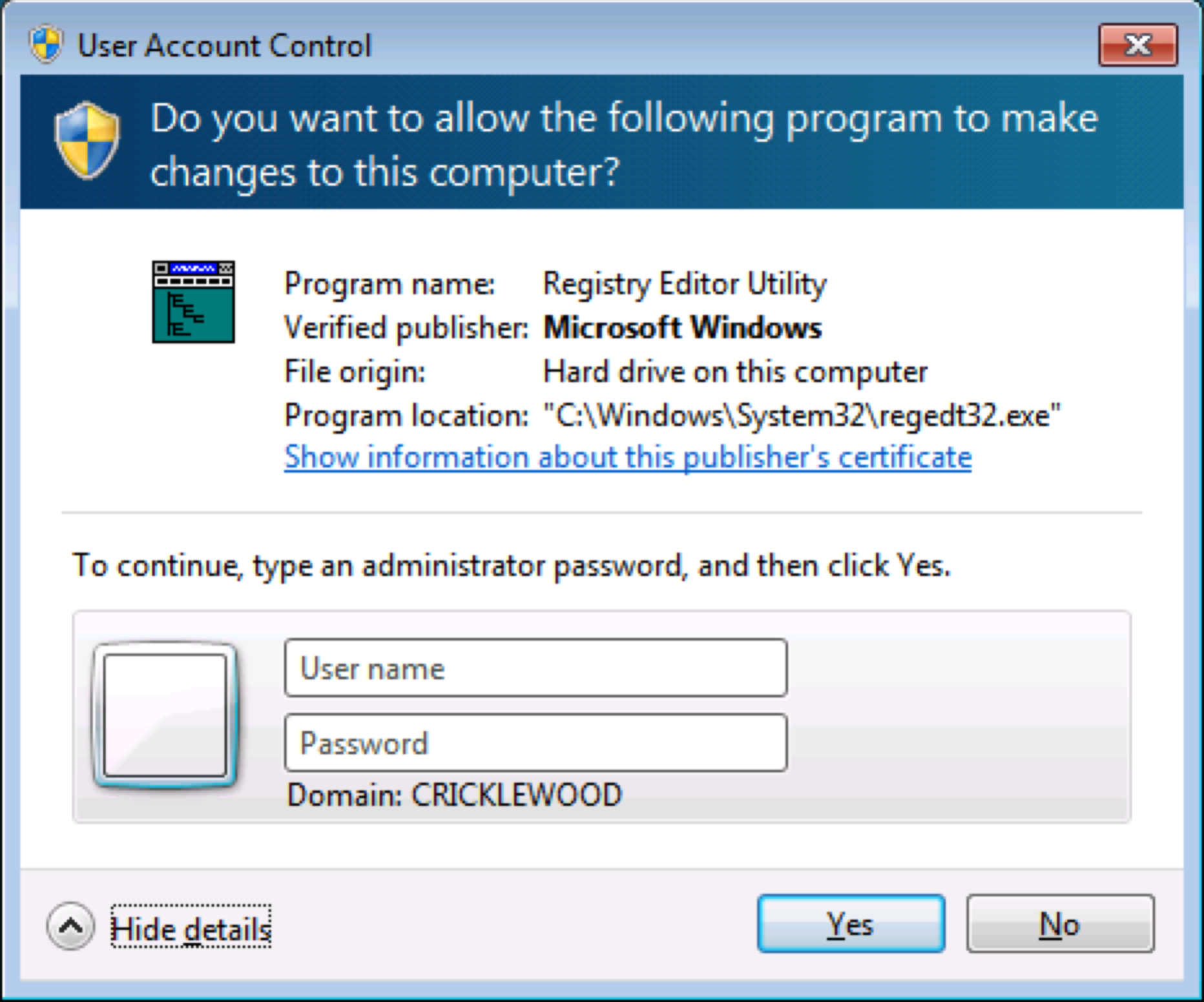
PowerBroker for Windows 6.7 has a brand new action type that allows for the specification of PowerBroker Password Safe as the valid credential type. When a rule is matched (like for Regedit.exe below) the username specified is automatically transmitted to Password Safe and the current managed password automatically sent back to the PowerBroker for Windows agent.
 The username and password are then used to execute the application seamlessly using the “Run As” command with the managed credential. The results are in line with the next generation of privileged password management:
The username and password are then used to execute the application seamlessly using the “Run As” command with the managed credential. The results are in line with the next generation of privileged password management:
- The application can be launched with real domain or local credentials and neither the username or password is exposed to the user.
- Applications are managed from within PowerBroker for Windows, ensuring a proper one-to-one application match by user or asset.
- Passwords are managed and secured via PowerBroker Password Safe. Communications between the two is encrypted for request and transmission.
- The entire workflow of logging into a safe password storage solution, locating the credentials, checking them out, and copying them into an application is completely eliminated.
- All activity for the credentials is logged and can be reported on from within BeyondInsight for both solutions.
- Session monitoring within PowerBroker for Windows can capture the screen and keystrokes while the privileged application is executing even if the session was not started in Password Safe.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








