
When it comes to getting widespread adoption of security solutions, there’s a group of users who are often overlooked: the IT Admin users. You might think – “of COURSE they will be on board with any solutions that make their enterprise more secure. It’s core to their jobs!” Think again.
There's something unique about the role of the IT Administrator – in order to be successful, they have to be organized and move quickly. With hundreds of systems to monitor and a high- stakes task of ensuring system uptime and productivity, there is simply no time to waste with changes in workflow or disruptions, like new processes that add steps instead of streamlining them.
The adoption of privileged password management and privileged session management (PPM/PSM) hinges on full user adoption. IT Admins, like the database administrators, push back because the new PAM solution forces a different workflow which affects their job productivity. And typically, admins/departments that push back tend to get rolled out last. The risk is that areas of the business remain exposed because Admins either can’t find a way to make it work for them, or they work around your new PAM solution.
So, when it comes to deploying PPM/PSM solutions, you have to not only consider technical ability: usability for your IT Admins is equally important. Most commercially available PPM/PSM offer similar capabilities: password rotation, application password management, SSH key management, and privileged session monitoring and recording (often for an additional fee). The real differentiator is not in what these solution providers offer, but in how power users like IT admins have to use them.
By allowing IT Admins to work in the same way they currently do, using the same tools, but with the silent benefit of auditing, logging, etc. – it’s invisible to them and your organization is now more secure.
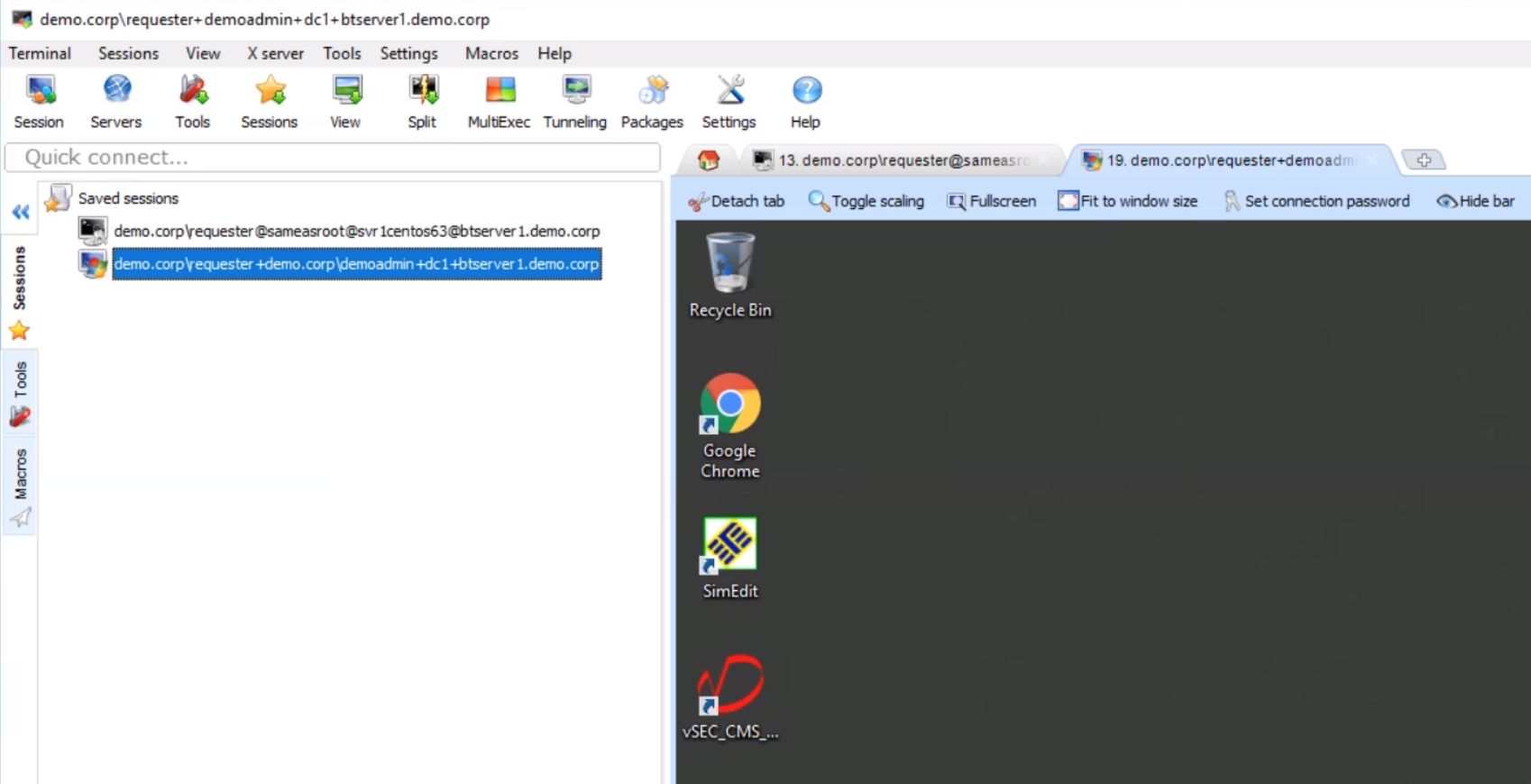
BeyondTrust PowerBroker Password Safe can help make user adoption both convenient and less expensive in the long-run. PowerBroker Password Safe includes a capability called DirectConnect, which removes the web interface equation from the end user. With DirectConnect, IT Admins can store shortcuts in their existing toolsets. We do not change the way Admins work; we provide a secure way for them to continue their work.
Storing and launching sessions could not be easier. A simple connection string is entered in any SSH or RDP client, for example, PuTTY, MobaXterm, Microsoft Remote Desktop Connection Manager, mRemoteNG, Devolutions Remote Desktop Manager.
In addition to making user adoption convenient, Password Safe’s licensing and deployment can also save your organization money. Password Safe’s licensing for the application proxy is favorable – competitive solutions require a CAL for every user that uses the application, making the total cost of ownership much higher. Password Safe requires a single device CAL, saving you both time and money. Additionally, privileged session management and application management are included – there are no extra charges for critical functionality. When you’re considering your options for a new privileged password management solution, all of these savings and conveniences add up.
To learn more about how we can help you address various privileged password and session management challenges, download our latest white paper, “A Technical Solutions Guide for Privileged Password and Session Management Use Cases.”

Martin Cannard,
Martin has been helping organizations solve challenges in the privileged account management and identity and access management space for over 24 years. At Dell Software, Martin managed a team of Solution Architects, focused on designing and implementing solutions in the Privileged Account Management (PAM) space. Prior to joining Dell, Martin was Sr. Product Manager for Novell Privileged User Manager, a privilege management application acquired from Fortefi, an organization where he served as Vice President, Corporate Development. Prior to this, he was Program Manager of Client Technologies at Symantec where he was responsible for many ground-breaking field and channel enablement applications. Additionally, Martin managed the European QA group at Axent Technologies and has held various management positions in consulting, systems development, and operations. Martin is a regular speaker for security events, and webinars.








