
People blow off steam all the time. They vent to their coworkers, exercise, or play games online during work hours to ease stress and tension. In truth, it is nearly humanly impossible to work 8-hour days, every day, without a break in between. It is not good for your focus and not good for your productivity. With the advent of social media sites, many employers do not fuss if an employee surfs the web from time to time to take a break or even blow off some steam. This includes playing a game or two. Unfortunately, there has been a growing trend to use these sites, and the games that may be hosted on these platforms, to attempt to compromise your computer. Take a look at this:
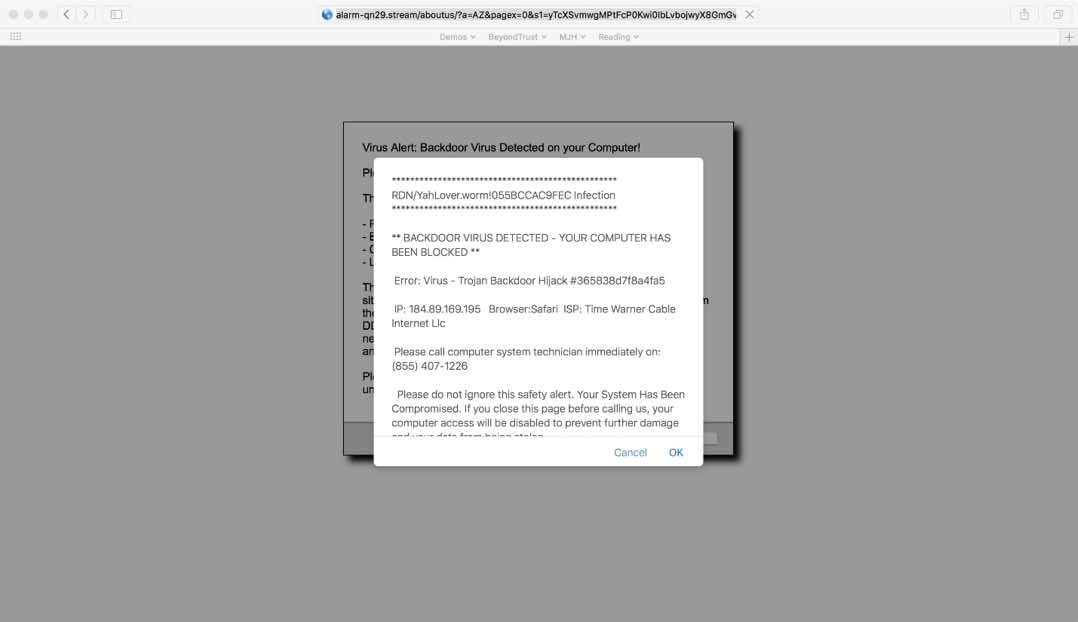
While playing a simple game on a social media site, this web page automatically redirected me through a malicious banner ad that was injected into the site. It was a clever piece of malware that tried to leverage Adobe Flash first and then displayed this auto refreshing page seconds after a drive-by attack failed. In addition, however it was coded, it would not allow me to close Safari on my Mac. It required a "Force Quit" to terminate. Insidious at best and potentially a real threat if I had a vulnerable version of Flash installed or recklessly followed the instructions.
For any organization that allows employees to blow off steam by playing games and does not have a sound vulnerability management and patch management procedure, this simple activity could have been a beach head for a much larger attack. An anti-malware solution or an advanced endpoint protection platform may have stopped the exploit, but that is not the point. The Internet is full of threats and even sites we potentially deem as safe could have malicious banners, flash applications, and content that are completely out of our control and just waiting to attempt to exploit our resources.
If you think the scope of this will not impact your business, consider this recent article on Hacker News. The malicious activity did not target your assets directly (unless you where one of the ones infected) but rather captured keystrokes and used your assets to help mine for cryptocurrencies. Ingenious and insidious – you were helping the threat actors actually make money.
Therefore, for every business that allows employees to blow off steam, consider what games, sites, and social media your team members are using. Ensure the latest security patches are applied to every resource – from the operating system to third party applications to plugins.
If you need help figuring this out, please contact us. BeyondTrust can help with our Retina family of vulnerability management solutions to detect missing security patches and apply patches to ensure your systems never fall victim to a malicious site and someone just trying to take a break.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








