 FireEye/Mandiant recently published a blog post, “SYNful Knock - A Cisco router implant - Part I,” describing how attackers are using network devices to implement backdoors within their target environments as a method to by-pass traditional security measures and provide a conduit for data exfiltration and further asset compromise. In addition to a detailed description of the attack, the company also indicated that it had discovered customers in several countries whose Cisco routers had been compromised. Cisco has indicated that these hackers used valid administrative credentials or physical access to the devices to perform their malicious activities.
In addition to weak physical controls, what are some other “gotchas” that you should be aware of when securing your network devices? Our experience says there are four:
1) Using simple/default passwords: The most common user names and passwords for Cisco devices are not necessarily the defaults that come with the device. Most administrators change them. Unfortunately, in most environments they can be guessed or compromised using brute force password attacks.
2) Using shared passwords: The second most common privilege flaw is to use the same passwords across the entire infrastructure and rarely, if ever, change them even if you have outsourced the management of the infrastructure. This problem can lead to a variety of malicious activities including exploiting recent vulnerabilities that can replace the device’s bootstrap loader with a piece of custom malware.
3) Limited password rotation: Excessive password ages due to the fear of changing passwords or a lack of management capabilities.
4) Limited auditing: Not knowing who is accessing network devices or what they are doing is a problem. Additionally if a number of administrators are logging in with shared username/password combinations, tracking specific access activities to an individual is not possible.
Any of these “gotchas” could lead to excessive risk of a breach. The best way to mitigate these risks is to implement an automated solution that:
FireEye/Mandiant recently published a blog post, “SYNful Knock - A Cisco router implant - Part I,” describing how attackers are using network devices to implement backdoors within their target environments as a method to by-pass traditional security measures and provide a conduit for data exfiltration and further asset compromise. In addition to a detailed description of the attack, the company also indicated that it had discovered customers in several countries whose Cisco routers had been compromised. Cisco has indicated that these hackers used valid administrative credentials or physical access to the devices to perform their malicious activities.
In addition to weak physical controls, what are some other “gotchas” that you should be aware of when securing your network devices? Our experience says there are four:
1) Using simple/default passwords: The most common user names and passwords for Cisco devices are not necessarily the defaults that come with the device. Most administrators change them. Unfortunately, in most environments they can be guessed or compromised using brute force password attacks.
2) Using shared passwords: The second most common privilege flaw is to use the same passwords across the entire infrastructure and rarely, if ever, change them even if you have outsourced the management of the infrastructure. This problem can lead to a variety of malicious activities including exploiting recent vulnerabilities that can replace the device’s bootstrap loader with a piece of custom malware.
3) Limited password rotation: Excessive password ages due to the fear of changing passwords or a lack of management capabilities.
4) Limited auditing: Not knowing who is accessing network devices or what they are doing is a problem. Additionally if a number of administrators are logging in with shared username/password combinations, tracking specific access activities to an individual is not possible.
Any of these “gotchas” could lead to excessive risk of a breach. The best way to mitigate these risks is to implement an automated solution that:
- Ensures no device has a default password for administrative accounts
- Guarantees each device has a unique complex password
- Automatically rotates passwords based on age and usage
- Controls and audits all administrative access and even communications to only authorized individuals
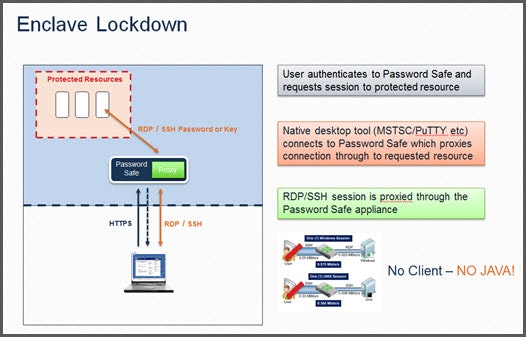 For more information on how Password Safe can help secure your Cisco infrastructure, review the datasheet. If you would like to see a Password Safe demo, request one here.
For more information on how Password Safe can help secure your Cisco infrastructure, review the datasheet. If you would like to see a Password Safe demo, request one here.

Brad Hibbert,
With over 20 years of experience in product strategy and management, Brad leads BeyondTrust’s solution strategy. He joined BeyondTrust via the company’s acquisition of eEye Digital Security, where Brad led strategy and products. Under Brad’s leadership, eEye launched several market firsts, including vulnerability management solutions for cloud, mobile and virtualization technologies. Prior to eEye, Brad served as Vice President of Strategy and Products at NetPro before its acquisition in 2008 by Quest Software. Formerly, at FastLane Technologies, which was sold to Quest Software in 2001, Brad worked extensively with key Microsoft business units on product direction and go-to-market strategies.








