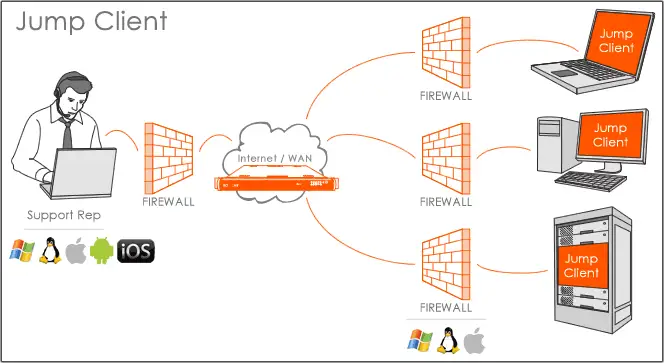
Jump™ Enables Remote Access, Regardless of Network Location
Provide Attended or Unattended Remote Support
Jump Clients let you control remote computers even when you don’t control the remote network.
Simply install a Jump Client on each system you need to access and you'll be able to control it wherever it goes—without requiring the person on the other end of the session to be present.
Multi-Platform Access, Including Android and iOS Devices
Jump Clients can be installed on Windows, Mac, Raspberry Pi, or Linux computers, as well as Android phones and tablets. You can access them from any platform BeyondTrust supports, from any location.
Support can now be delivered from a laptop or other mobile devices, promising productivity regardless of technician location.
Management and Mass Deployment of Jump Clients
Jump Clients can be mass-deployed to Windows, Mac, and Linux desktops or servers. To help with finding and identifying computers later, add a group name and comments when you deploy them.
Create a default installer, or use mass deployment scripts to pull in variables from other sources to modify the Jump Client parameters during installation. Additionally, you can programmatically retrieve a Jump Client installer via a REST API so that it can be part of automated processes, such as system provisioning or incident response.
Integrated for Your Systems Management
Support organizations can improve service levels, centralize support processes, and strengthen compliance by integrating BeyondTrust with their systems management platform.
Once integrated, BeyondTrust enables technicians to offer proactive system support to all Jump Clients directly from the systems management tool.
BeyondTrust can be launched from the ticket or system record. At the end of the session, BeyondTrust updates the ticket with details from each remote support session, including links to session recordings, file transfer details, work notes, system information, and post-session survey results.
Controls Govern Grouping, Permissions, and Interactions
Leverage Jump item roles to determine how users are allowed to interact with Jump Clients. Roles can be at the individual account level or at a group level.
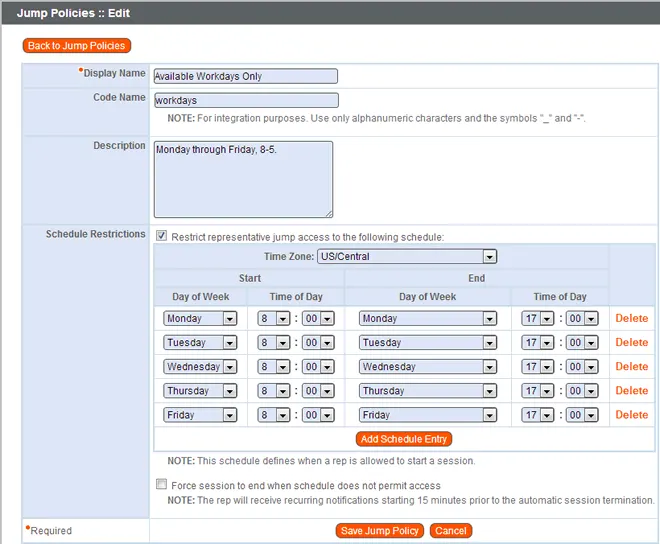
Jump Policies can then be applied to control when certain Jump Clients can be accessed by implementing schedules, or requiring a valid ticket ID to be entered prior to starting a session.
A Jump Group is a way to organize Jump Clients, granting member varying levels of access either individually or by means of group policy.
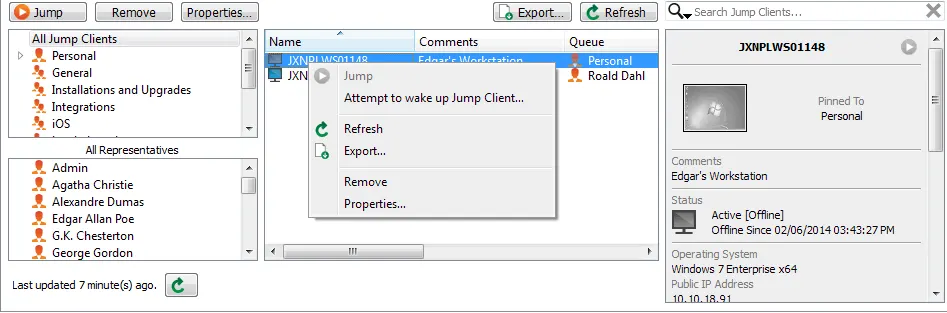
Wake-On-LAN Support for Jump Clients in a Network
Support organizations can save on power costs by powering computers off after hours. With BeyondTrust, powering systems on/off can be handled remotely with Wake-On-LAN (WOL) support.
With Wake-On-LAN support, you can broadcast WOL packets through another Jump Client on the same network. Use of Wake-On-LAN depends on user permissions and may not be supported in all environments.
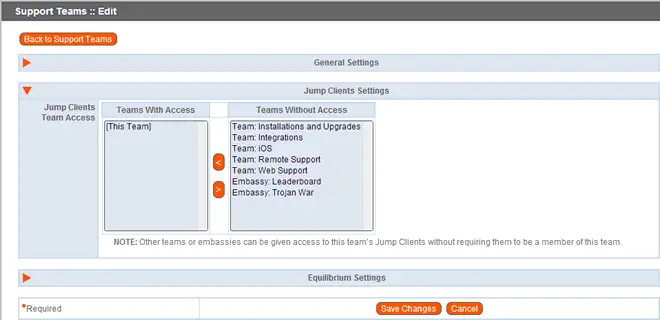
Sharing Jump Clients Across Support Teams
For scenarios in which multiple groups need to access the same group of desktops, you can share a team’s Jump Clients across support teams. Group policies determine how members of each team can interact with the remote computer.
Sharing Jump Clients gives both internal reps and vendors access to the same system without complicating team structures.
Endpoints to Define How Sessions Begin
When you use Jump Clients to access servers and backend systems, you want to launch right into remote control. No one is present on the other end of a server for you to interrupt. But when accessing remote desktops, you may want to display a prompt in case an end user is present.
Support Session Policies define how a session begins based on the endpoint being supported.
With policies at the Jump Client level, you can choose to display a prompt if the remote desktop is one at which an end-user may be present. If the endpoint is a server, you can set the session policy up with no prompt.
Once Connected, Powerful Tools Are at Your Fingertips
When connecting to a remote desktop or server, BeyondTrust puts powerful tools at your disposal, including:
Command shell
File Transfer
Multi-monitor support
Privacy screen
Reboot
Registry editor
Scripts
Special actions
System information
UAC elevation
Jump Technology, Defined
Jump Clients are a component of our patented Jump Technology. Jump Technology enables customers to access computers, servers and network devices any time 24/7.
Jump Client
Access thousands of remote desktops and servers no matter where they are or what operating system they run.
Jumpoint
Access almost any system on a remote network without a pre-installed client.
Jump Zone Proxy
A secure proxy lets you access remote computers on isolated networks without exposing them to the internet.
Shell Jump
Support switches, routers and other network devices to secure, auditable SSH/Telnet functionality.
Embedded RDP
Use Microsoft Remote Desktop Protocol securely across networks without VPN tunnels or open listening ports.
Intel® vPro™ Technology
Use Intel vPro Technology to power a remote pc on/off, reboot to BIOS, reimage a remote computer and access remote desktops regardless of operating system state.
Jump Technology is one of the ways BeyondTrust satisfies the needs of multiple support groups and scenarios.

