 UPDATE (5/16/17, 11:15pm EST)
As of audit revision 3274, here is an updated list of related WannaCry/WannaCrypt vulnerability audits. Use Retina or free Retina Community to scan your systems now.
Check for the SMBv1 vulnerability on all affected platforms:
UPDATE (5/16/17, 11:15pm EST)
As of audit revision 3274, here is an updated list of related WannaCry/WannaCrypt vulnerability audits. Use Retina or free Retina Community to scan your systems now.
Check for the SMBv1 vulnerability on all affected platforms:
- 62804 - Microsoft Security Update for Windows SMB Server (4013389)
- 63900 - Microsoft Security Update for Windows SMB Server (4013389) - Remote (** Note, requires Retina 6.2.1. or higher **)
- 63901 - Server Message Block Version 1 (SMBv1) Detected - Local
- 63902 - Server Message Block Version 1 (SMBv1) Detected - Remote
- 63899 - WannaCrypt Ransomware Detected
- 62790 - Microsoft Security Update for Windows - March 2017 (4012212/4012215) - Windows 7
- 62797 - Microsoft Security Update for Windows - March 2017 (4012213/4012216) - Windows 8.1
- 62791 - Microsoft Security Update for Windows - March 2017 (4012212/4012215) - 2008R2
- 62801 - Microsoft Security Update for Windows - March 2017 (4012214/4012217) - 2012
- 62798 - Microsoft Security Update for Windows - March 2017 (4012213/4012216) - 2012R2
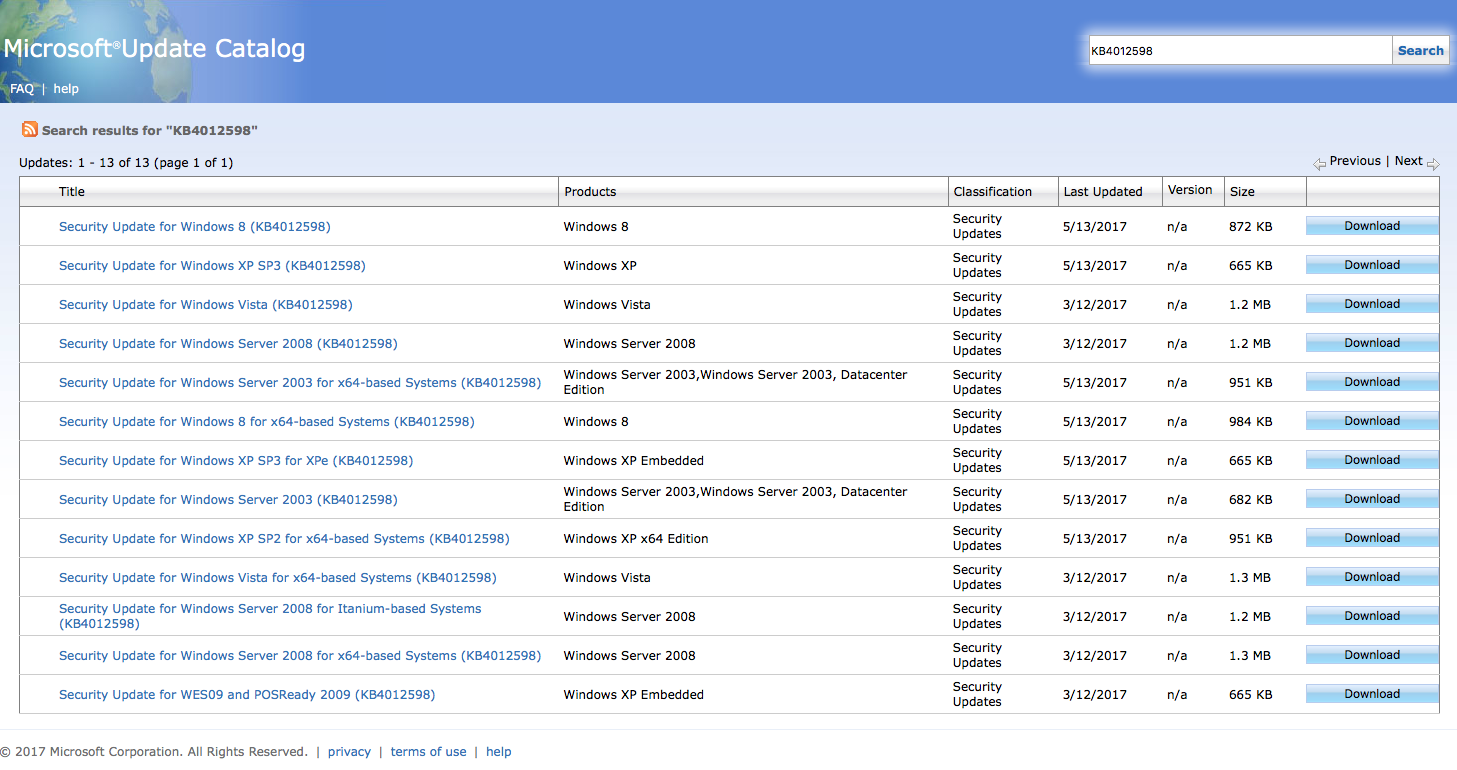
- 63833 - Microsoft SMB Server Vulnerability (4012598) - XP
- 63834 - Microsoft SMB Server Vulnerability (4012598) - Server 2003
- 63835 - Microsoft SMB Server Vulnerability (4012598) - Windows 8
- 63833 - Microsoft SMB Server Vulnerability (4012598) - XP
- 63834 - Microsoft SMB Server Vulnerability (4012598) - Server 2003
- 63835 - Microsoft SMB Server Vulnerability (4012598) - Windows 8
ORIGINAL (5/12/17, 11:00pm EST) According to CNN, a worldwide ransomware attack named "WannaCry" is occurring across 99 nations in just 11 hours using an exploit “EternalBlue” targeting Microsoft Windows that was patched in March and leaked from the NSA. The ransomware, “WannaCry”, is infecting computers and raises the ante every six hours of non-compliance with payment terms. The initial cost is just $300 but quickly escalates if firms ignore the ransom. As of this posting, the United Kingdom has had sixteen National Health Service organizations infected and hospitals have been canceling non-critical appointments in order to deal with threat. In total 45,000 systems. Spanish Telefonica has been hit by the weaponized worm-able ransomware as well making it one of the largest company experiencing the current threat. While the cyber-attack is primarily in Europe and Asia (Russia allegedly being hit the hardest), it is just a matter of time before the threat propagates to the United States and infects other Windows systems on the internet that are not patched. In order for organizations to protect themselves, make sure your Windows assets are patched for MS17-010. If you still have Windows XP, there is no patch or permanent mitigation strategy since this operating system is end of life. Some security tools may help but the risk will never be truly remediated. It is one of the primary reasons organizations need to remove and update these assets. The security update will stop the infection but not remediate the risk if you have already been compromised. If you are not sure if you are at risk, please download a copy of Retina Community from here and scan using these audits:
- Vista / 2008: 62804 - Microsoft Security Update for Windows SMB Server (4013389) - 4012598
- Windows 7: 62790 - Microsoft Security Update for Windows - March 2017 (4012212/4012215) - Windows 7
- Windows 8.1: 62797 - Microsoft Security Update for Windows -March 2017 (4012213/4012216) - Windows 8.1
- Window Server 2008 R2: 62791 - Microsoft Security Update for Windows -March 2017 (4012212/4012215) - 2008R2
- Windows Server 2012: 62801 - Microsoft Security Update for Windows -March 2017 (4012214/4012217) - 2012
- Windows Server 2012R2: 62798 - Microsoft Security Update for Windows -March 2017 (4012213/4012216) - 2012R2

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








