 I’m pleased to announce that BeyondTrust’s Retina Enterprise Vulnerability Management has successfully completed PCI Scanning Vendor Compliance Testing. This means that Retina meets all PCI Security Standards Council requirements to perform PCI data security scanning. This also marks the fifth year that BeyondTrust is an Approved Scanning Vendor (ASV).
I’m pleased to announce that BeyondTrust’s Retina Enterprise Vulnerability Management has successfully completed PCI Scanning Vendor Compliance Testing. This means that Retina meets all PCI Security Standards Council requirements to perform PCI data security scanning. This also marks the fifth year that BeyondTrust is an Approved Scanning Vendor (ASV).
Where Vulnerability Scanning Comes into Play for PCI DSS Compliance
The PCI Data Security Standard (PCI DSS) has been a hot topic in the IT security industry since it was first released in 2004. If you work with a merchant or service provider subject to the PCI DSS, you probably already know that the Standard requires you to conduct quarterly vulnerability scans of systems that store or process card holder data. Here’s the excerpted summary of PCI DSS Requirement 11.2, which mandates vulnerability scanning:
11.2 Run internal and external network vulnerability scans at least quarterly and after any significant change in the network (such as new system component installations, changes in network topology, firewall rule modifications, product upgrades).
If you need a refresher, you can find the full details in PCI DSS v3.
Why Retina is Different from Other PCI Scanning Solutions
BeyondTrust isn’t the only PCI ASV to be authorized by PCI, but I’ll put a stake in the ground as to why BeyondTrust and the Retina vulnerability management solutions are better than the rest. It really comes down to three things:
1. Zero-Gap Coverage for Diverse Payment Card Data Environments
Retina provides vulnerability scanning coverage across network, web, mobile, cloud and virtual infrastructure. Retina can scan any IT asset for vulnerabilities that pose PCI DSS compliance risks. While traditional network scanning is nothing new, many merchants and service providers are looking to virtualization to save costs and increase efficiency. If you happen to be using a VMware environment to house cardholder data, check out the BeyondTrust VMware Solution Guide for the PCI DSS. For information on closing other PCI scanning gaps, read our white paper: Reduce the Cost of PCI DSS Compliance with Unified Vulnerability Management.
2. Integrated Patch Management for Mitigating Vulnerabilities that Jeopardize PCI Compliance
Vulnerability scanning is critical to addressing security exposures in card data systems, but it represents only half the battle; you need to fix the problems that you find. Fortunately, Retina closes the loop on vulnerabilities with integrated patch management capabilities. Via an optional module, Retina connects with Microsoft WSUS and SCCM for patching Microsoft operating systems and applications, as well as applications from other vendors. Patching information can then be shared with Retina’s Regulatory Reporting and Configuration Compliance Modules to prioritize patch management based on risk profile.
3. Unmatched Reporting for Measuring and Proving PCI Compliance
When you use Retina CS Enterprise Vulnerability Management, you automatically have access to the centralized BeyondInsight reporting and analytics console. This gives you access to over 260 standard reports, including several designed for PCI reporting that go above and beyond the specification in the DSS 3.0 standard to truly make assessment “business as usual.”
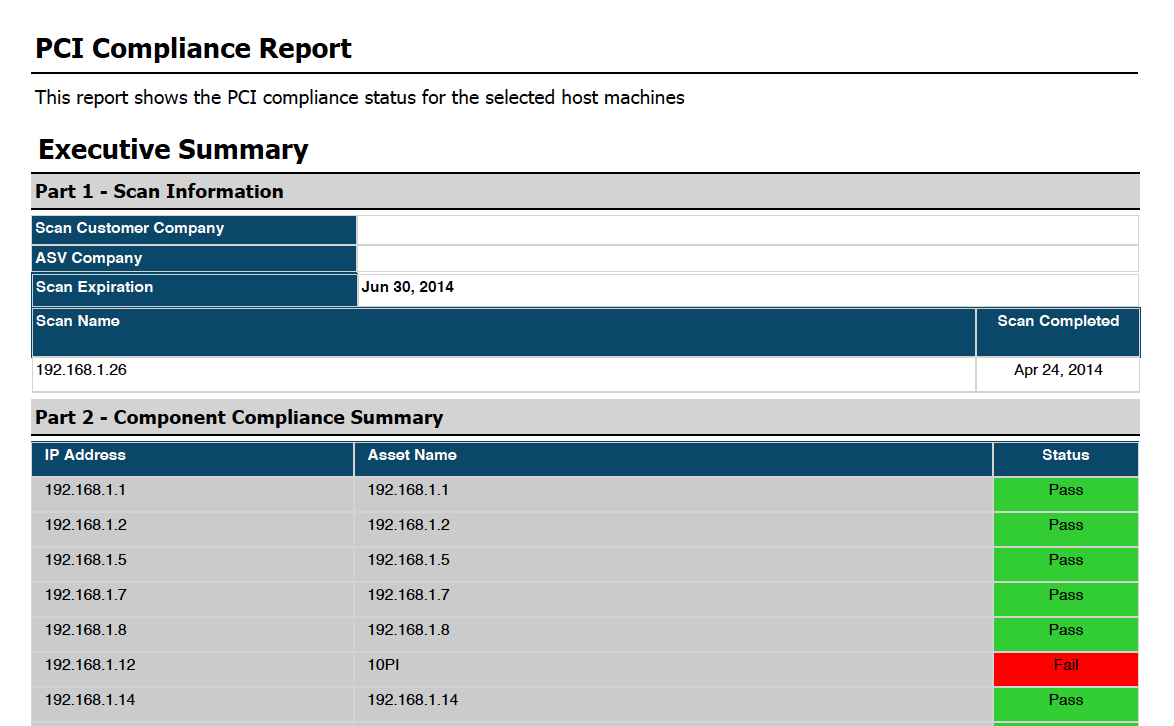
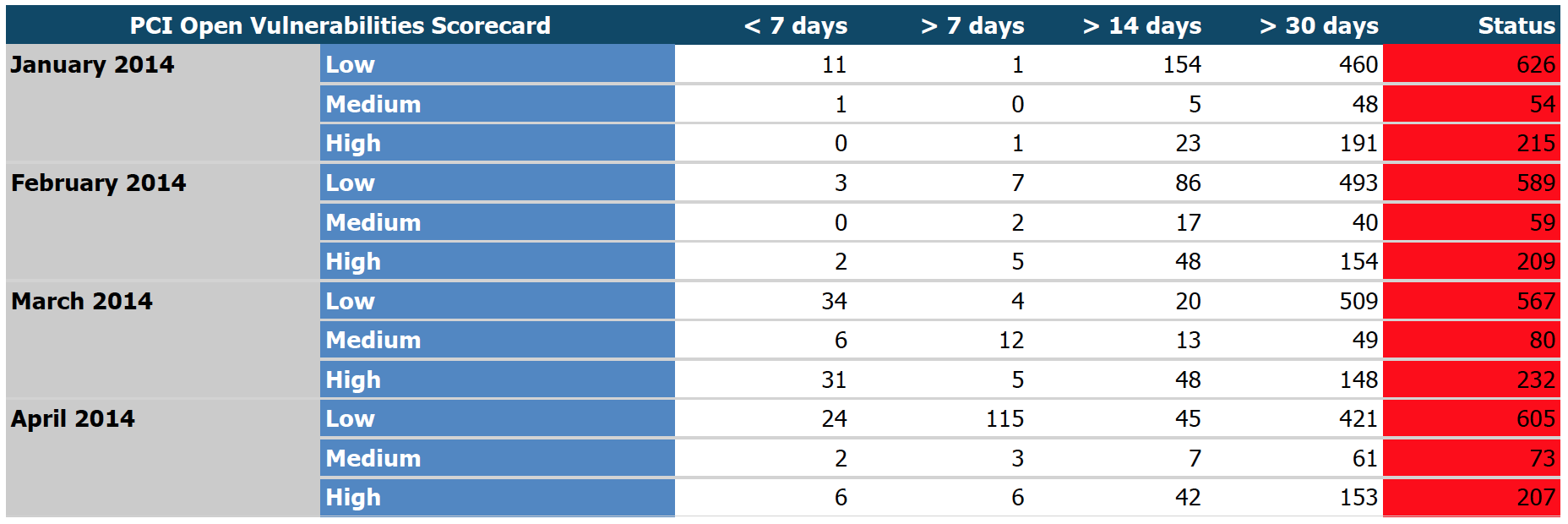
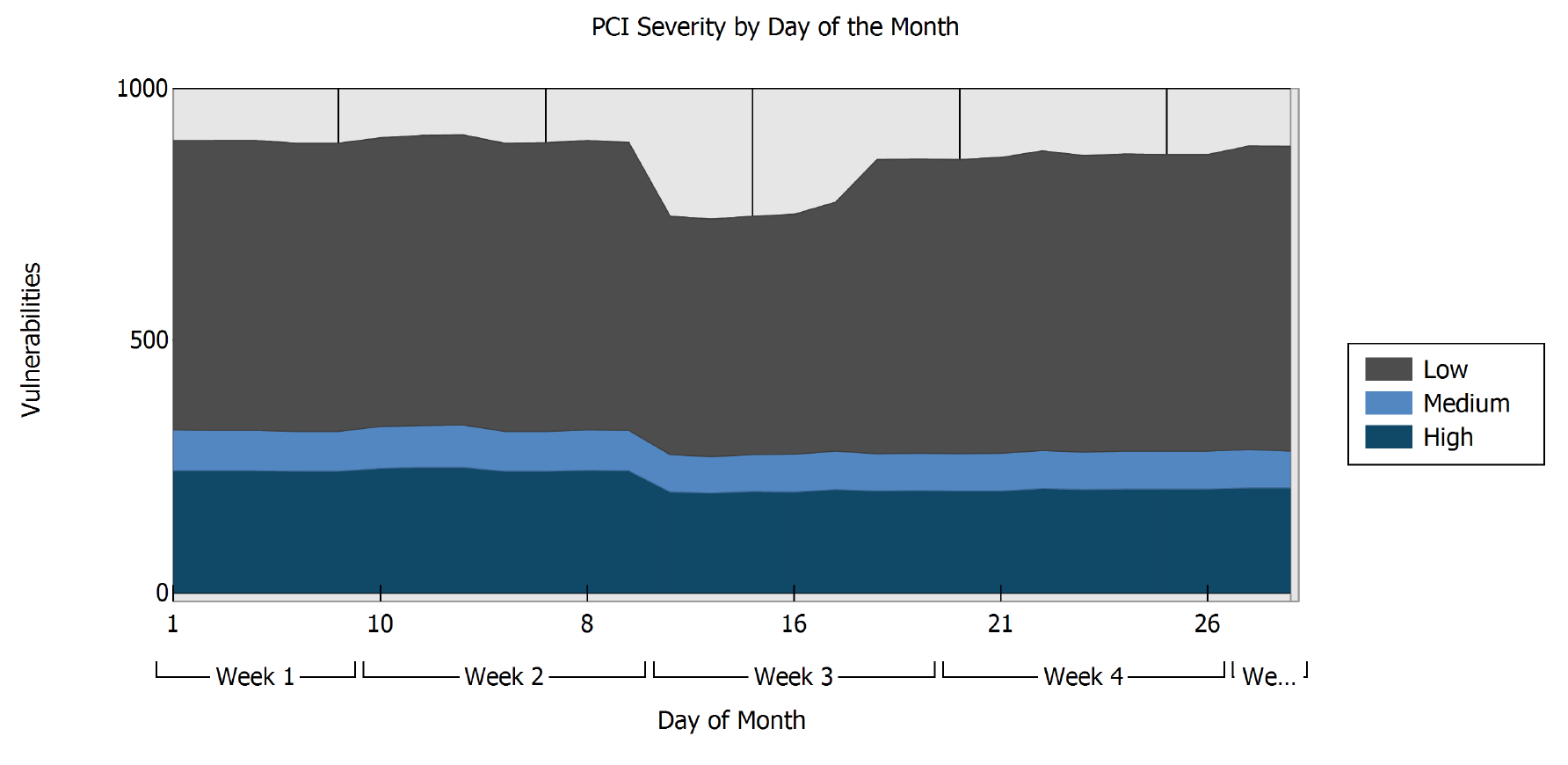
Here are a few examples of Retina PCI reports, many of which offer interactive drill-down and filtering capabilities:
- PCI Compliance Overviews: display pass/fail compliance status for individual assets and asset Smart Groups
- PCI Scorecards: map vulnerabilities to PCI severity level and indicates how long vulnerabilities have been outstanding in the target environment
- PCI Severity Trends: track PCI vulnerability counts by severity over a selectable time period
- PCI Severity Deltas: detail monthly PCI severity deltas (added, removed and existing vulnerabilities)

See How Easy PCI Vulnerability Scanning Can Be
As someone famous once said, don’t take my word for it; try it for yourself:

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








