Using Privileged Access Management for Advanced Control and Protection of Assets Within Your Environment
The simple phrase, “All your base are belong to us” from the arcade style Sega Genesis game, “Zero Wing” has evolved into a meme (check out the meme here!) that has come to mean a loss of control, or a sinister takeover of something that you believed should be under your control. The topic of this blog will be to take that meme and apply it to assets in your network environment, and to offer some suggestions that will, hopefully, prevent your environment from being victimized.
This is a very serious concern for any technical environment, and although I may use some fun memes like the one mentioned above, I assure you – I take this very seriously. The evolution of privileged access management (PAM) has led to new levels of maturity that incorporate previously unavailable controls, and some steps to take advantage of this will be outlined below.
"All of Your Server Are Belong to Us"
Whether it is 1) a case of someone encrypting your servers and holding them for ransom, 2) an unauthorized external access to your systems, 3) an inadvertent configuration error that allows someone to gain access to information that they should not have, 4) a zero-day exploit, or a backdoor that was unknown in your environment — the one thread of commonality is that someone accessed a system that they should not have accessed.
Sometimes, the first indication that a company's servers were compromised OR unauthorized access has taken place is from a third-party source, or an email demanding ransom. This is the true doomsday scenario for most organizations because it brings with it a loss of credibility, brand damage, and impacts revenue and shareholder value.
Step one is to look at the problem – understand the only way to prevent these potential threats to your company is to do everything in your power to control access within your environment. This may require a modification to the way that PAM is viewed within an environment, and how it is structured in the organization.
The Traditional Model of Privileged Access Management Within an Organization
When the concept of privileged access management was first defined, PAM was usually a subset of Identity and Access Management (IAM). On a personal level, I think this was because the program was new, the requirements were not fully understood, and IAM was a familiar territory within most companies.
IAM has been the traditional home of all things related to "identity" – such as user logins, credentials, password management, and both general and strict user access controls. The bulk of the focus in most environments has always been on users, and what level of access they were granted. The flaw in this model is that, in a lot of cases, very little focus was directed toward the assets that were being managed – and whether they were truly catalogued to understand the risk involved with user access to them. The following diagram is an abbreviated version of a traditional technology organization in relation to PAM:
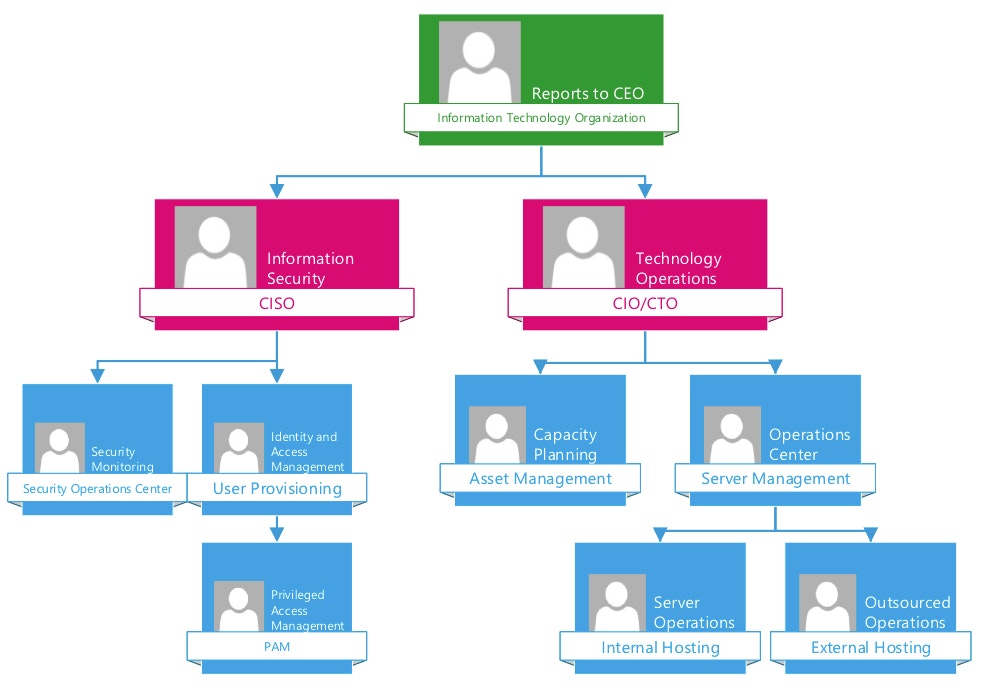
Note that in the above model, PAM is a sub-component of IAM, and that asset management is handled under an entirely separate organization. This is a very common model for organizations, and I believe it's because as new disciplines evolve – they are generally tacked on to existing organizations until they mature.
It's Time to Change the Traditional Model of Privileged Access Management
PAM as a discipline has matured significantly over the past 20 years – and although it was widely conceptual in most organizations until recent years – it has matured to the point where it should be repositioned in relation to the traditional models. Years have been spent learning the minute details of how users are provisioned, developing reliable sources of information, ascertaining asset characteristics (servers, OS types, patch monitoring, data housed on the servers, etc.), and how these elements come together to make an informed decision related to privileged access. This ground-up approach provides organizations with the ability to truly trust and understand information about identity and assets accessing their network.
Looking at the maturity of PAM, and how it has evolved over many years, it is time to consider a paradigm shift in how organizations view PAM in relation to other parts of their technology organization. With this paradigm shift, some principles can now only be implemented due to the long-term maturity of PAM:
- Access to anything in the technology environment is a privilege
- A complete and accurate record of all assets in the organization is required
- The activity on and the health of all systems must be continuously monitored
- A complete record of all access to systems in the organization is required
- Control over who can do what on all systems must be strictly enforced
Each of these common-sense principles aligns with virtually every regulatory or compliance program in the world. Beyond that, those simple statements are no longer aspirational goals, they are achievable metrics with the evolution and maturity of PAM tools. PAM has been developed from the ground up within most technology organizations, and this required that the minutia of all systems and users be documented and understood. These details may now become the foundation of any technology organization.
In order to truly recognize the strength of a mature PAM program, the time has come to restructure the organization to leverage these tools. A mature organizational chart should come to look something like this:
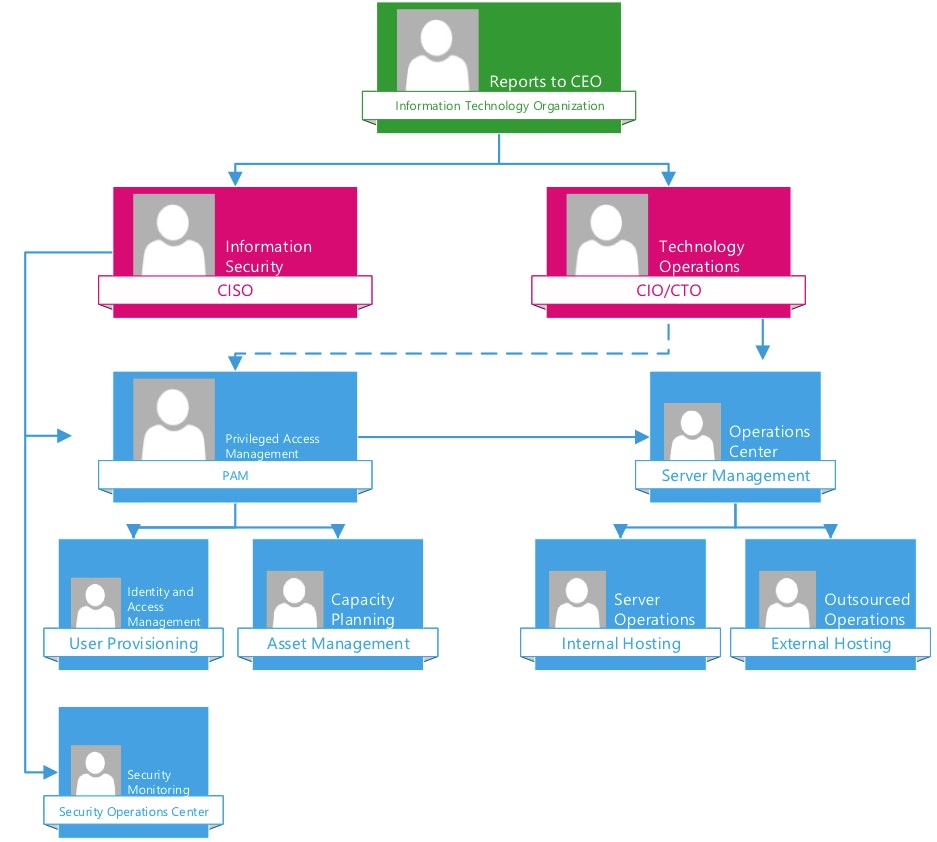
By modifying the traditional model in this way, access to anything and everything within the environment is controlled by PAM tools, and PAM becomes the gateway to all system access.
“Who”, “What”, and “Where” are the three most critical components when making decisions related to PAM. A strong security profile is achieved by moving Asset Management (“Where”), and Identity Management (“Who”) under PAM, and continuously working to guarantee the accuracy of asset and identity information becomes key to success. This model depends on the accuracy of information related to identity and assets to function properly.
The Integrated Risk-Based Privileged Access Management Model
As the new organizational structure matures, organizations can begin to incorporate other tools and data into their PAM decision making process. The overall goal is to evolve PAM into a risk-based model for privileged access. An example of this would be applying risk-based privileged access controls using PowerBroker for Unix/ & Linux (PBUL). This approach has been discussed in the security industry as “Attribute Based Access Control” or ABAC, where multiple factors are used to determine the risk level of any privileged activity. In this case, risk is calculated, and based upon a fully configurable evaluation of the risk, various actions can be performed.
An activity can be scored based on the ‘Who’, ‘What’ and ‘Where’ – with each having a separate value that when combined – can be used to determine the overall risk level of the activity. Policy code can be written to evaluate each factor separately, or combined, and actions can be taken depending on user determined values. This score is factored in where desired to calculate an overall risk for the activity.
For example:
A low-risk user executes the ‘id’ command on a development Linux server:
user rank (0) + server rank (0) + command rank (0) = Total risk (0) and this is considered a “Low Risk Activity”.
Or
A high-risk user executes the ‘shutdown’ command on a critical production server:
User rank (500) + server rank (5000) + command rank (5000) = Total Risk (10500) and this is considered an “Extremely High-Risk Activity”
Each factor (“User”, “Command” and “Server”) can be configured with a user defined score, and when all three are added together, this provides a combined risk score. By default, all risk assignments are fully configurable, and set to zero in the absence of any entry. This permits users to add risk levels as they choose to, without the possibility of disrupting activity.
Event thresholds are fully configurable as well, and this lets users determine cut-off points for risk levels, and to configure a nearly infinite number of risk levels. Factors may be added together, or considered separately during policy evaluation. For instance, a policy may be configured to permit privileged activity on servers with a risk ranking less than a specific value, or for users with a trust score above a certain threshold. This gives granular control over policy, and permits situational evaluation at a micro-level within a user environment.
Using a risk based model to control policy alters the paradigm of PAM and reduces the management of policy throughout the enterprise. In this model, all ‘accepted’ commands are fully session logged, and recorded, and control is shifted to look at the overall combination of user activity. This relieves an enterprise of the burden of managing specific commands, servers, and users within individual group policies, and permits privileged activity based on the nature of the server, the character of the user, and the potential for the command to cause issues. Using this method, all privileged activities are approved unless there is a reason to deny them – and this provides the agility that most enterprises are seeking – while still meeting their regulatory requirements.
Using this model, the traditional user group model can be used to assign a maximum ‘risk level’ to any activity by members of a group/team, and this brings the dynamic support necessary to deliver the agility required by the DevOps model to which enterprises are turning. Over time, additional data sources can easily be added to policy to permit the evaluation of even more potential risk factors.
This is one example of how the BeyondTrust PowerBroker PAM platform can be configured to help organizations achieve a better posture with regard to the "Zero Trust" security model that was the subject of a previous blog.
The BeyondTrust Advantage
Looking at the environment from a PAM point of view, if you're already a BeyondTrust customer, you have the following advantages to help prevent exploits to your systems:
- Retina Network Security Scanner: Identifies all network assets in your environment, and to maintain visibility into the health of your environment – confidently defines the borders of your environment, and what you need to protect.
- BeyondSaaS: Meets regulatory requirements and gives you an outsider’s view of your environment. Identifies all open ports, servers, applications, and services that are available from an external source, so you know what each does.
- PowerBroker Password Safe: Uses asset lists, and catalogues all of the identities on all of your servers. Secures all of the credentials that can access your systems with an ongoing process to protect them. Plus, controls a single portal that provides access to the most secure servers with complete monitoring and control over their activities.
- PowerBroker Identity Services: Integrates servers to authenticate to a single source – Active Directory. Users must have the appropriate group memberships, and access levels to access any server in your environment, and you have an audit trail to prove it. Individuals in your organization use a single credential to access all of your systems, and you can carefully control their access.
- PowerBroker for Windows & Mac: Deploys agents on all of your Windows/Mac laptops and servers that can control all administrative activity on your systems. Restricts specific processes from running, or to authorize processes to run based on group policy.
- PowerBroker for Unix & Linux: Deploys trusted agents to all of your Unix/Linux servers, and using the powerful policy language, you have complete control over your environment. Policies are in place that permit privileged activities, or access to credentials on specific servers for specific individuals, or groups for specific reasons. Have a complete record of all activity that takes place during a privileged session, and you review these sessions regularly as part of your compliance program.
- PowerBroker for Networks: Network devices are as vulnerable as servers, so it is important that you apply the same level of control to your routers and switches as you would to your servers. Know who is accessing them, what they are doing, and why they are doing it.
- BeyondInsight, the PowerBroker Central Platform: Reports into a console, all of the PowerBroker products, with a dashboard view of your status in all areas. Have the confidence knowing that access to your systems is protected, and review any activity that takes place.
- Threat Analytics, (part of the central platform): Analyzes behavior and develops a baseline of activity that can be expected in your network. These analytic processes run on a regular schedule, and they provide alternate ways to view the activity that takes place in your environment – identifying anomalies in your environment.
Summary
The controls provided by your BeyondTrust products give you the opportunity to provide a new level of visibility into your network environment. Your PAM program is mature enough that you are prepared to deliver much greater control over the “Who”, “What”, “Where”, and you can also add the “When”, and “Why” as your program evolves.
Let’s review the advantages for BeyondTrust customers:
- Identify all of the assets on your network, and what they do
- Consolidate all of the credentials on your network, and secure them
- Control all user activities within your environment – regardless of the operating system
- Audit all of these activities, and get a single view of your environment
- Analyze behavior and get unusual activity brought to your attention
- Monitor activity and review sessions in real-time using the agents deployed
- Prevent and/or alert when system libraries, or other direct memory functions are accessed via many different methods including syslog, paging, email, or whatever is configured in your environment
The key to avoiding an "All of your server are belong to us" scenario – and potentially losing control of assets within your environment – is to up your game in the privileged access management space. You can do this if you implement a secure system where users access only those servers or applications that they need to access in order to perform their jobs. That access is carefully controlled, and access points are carefully monitored. You can restrict lateral movement between servers, and have the ability to isolate users to specific tasks, or functions once they are on your systems. Placing PAM at the forefront of your environment permits you to use all of the information available to you to make decisions related to access within your environment.
If you are a BeyondTrust customer, you already have one or more of these solutions needed to protect your environment. If you are not already a BeyondTrust customer, and you would like this level of confidence and maturity in your environment, contact us and we’ll be happy to set up a strategy session.
Chad Erbe, Professional Services Architect, BeyondTrust
Chad Erbe is a Certified Information Systems Security professional (CISSP), with nearly 30 years’ experience in a Unix/Linux administration role. Chad has worked in DoD high-security environments, manufacturing, and with large financial services companies throughout his career. This broad experience has lead him to an architectural role with BeyondTrust where he focuses on Privileged Access Management, particularly in the Unix suite of products. Chad also maintains his PCI ASV certification from the PCI council.









