In the era of next-gen technology, it's the often-forgotten basics that provide the best foundations.
By reducing the attack surface and building secure defensible endpoints you'll be in a far better position to stop cyber attacks and keep your data safe.
Now in its 4th year, The 2016 Microsoft Vulnerabilities Report from Avecto provides an important reminder to organizations that we cannot ignore the simple things.
It's common to think that migrating to the latest operating system will improve security, but in isolation, it’s no way near enough to reduce the risk of attack.
In the 2016 Microsoft Vulnerabilities Report despite Microsoft stating it's "designed to be the most secure Windows ever", Windows 10 had the highest proportion of vulnerabilities (395) compared to any other OS.
And it's a similar story with Microsoft Edge. This is Microsoft's newest and supposedly "safer" browser, yet there were 111 vulnerabilities in 2016. Admittedly, the various versions of Internet Explorer only fared slightly better with a total of 109 vulnerabilities but it will probably still surprise many to learn that Edge is a bigger security issue for those not employing least privilege.
The good news? Removing admin rights could mitigate the risk associated with 100% of these vulnerabilities across both Microsoft browsers.
And our report provided plenty more compelling reasons for doing so. Not least that 94% of critical Microsoft Vulnerabilities can be mitigated by removing admin rights, up from 85% last year.
There were 530 vulnerabilities in total last year, 189 of these were critical. By comparison, take a look back to 2013, the year of our first report, and we saw 325 vulnerabilities, 147 of which were critical.
The benefits of removing admin rights should be clear. However, for some, the reluctance to introduce least privilege across a corporation will be down to the perception it’s difficult to achieve, as well as a belief that it will put up barriers and impact productivity.
How to achieve security and freedom
By building up from secure foundations on the endpoint, you can achieve defense in depth without impacting productivity. Removing admin rights is just the start of the journey. Removing privileges without a solution in place to ensure employees can continue to be productive creates an over-locked environment which will only drive calls to the IT helpdesk. This situation often leads to ‘privilege creep’, as admin rights are slowly reintroduced and ‘shadow IT’ workarounds come into play. It’s, therefore, essential to have technology in place to manage user requests and exceptions.
Additionally, malware can still do damage to a standard user account – although there’s a much lower risk of widespread data loss. The malware still has access to everything that the user does on the machine.
Building up layers of defense
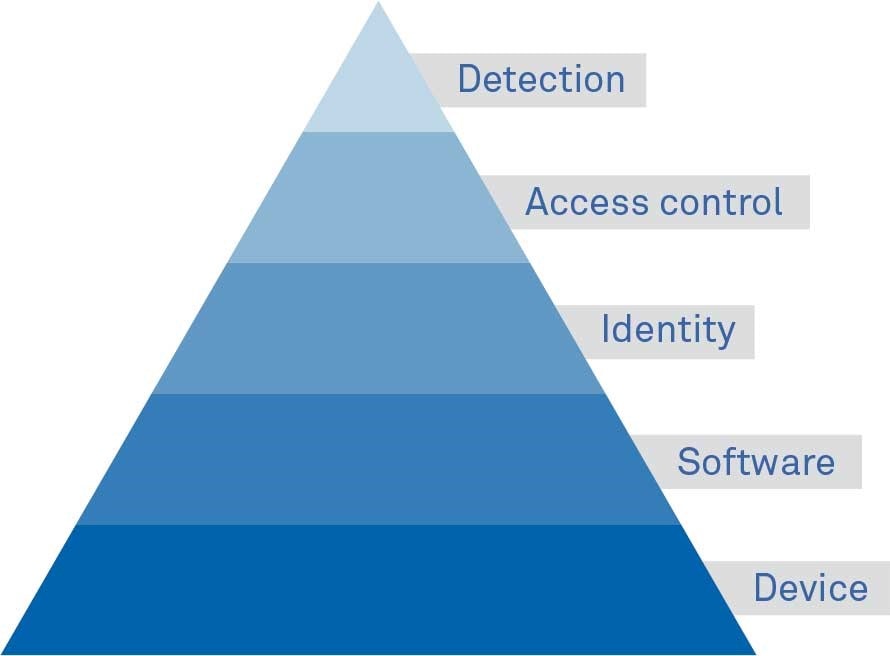
Microsoft's Hierarchy of Cyber Needs is a clear demonstration of the need to prioritize the different layers of security solutions. It shows how to work up from the device through to software and user access, adding detection as a last line of defense.
Identity management needs
You wouldn't run a bank without asking customers for identification when making withdrawals, so don't try to run your business without identity management. Security is easier with privilege management and everyone is able to get on with their jobs.
Access control needs
To avoid putting the crown jewels at risk, the advice is simple - use least privilege, make all users non admin and sandbox the most common attack vectors like links from email spam and malicious attachments. Least privilege and content isolation allow critical resources, such as sensitive data, to be segmented away and sandboxing makes these harder to get at.
Detection
Detection has an important role to play, but can't be relied upon on its own. Importantly, getting applications and content under control first means that detection solutions are not flooded with the same volume of unknown threats.
A multi-layered defense is achievable with Defendpoint, which takes a simple and smart approach to prevention on the endpoint.
You build the proactive layers before adding the final catch all of detection, rather than the other way around, as this is a far more reliable form of defense.
Find out more and download your copy of the 2016 Microsoft Vulnerabilities Study here.








