
The holiday season is upon us. Thanksgiving, in the United States, is around the corner where thousands of pounds of turkey will be eaten. Then we will weather the chaos Black Friday sales. But for merchants it's time to think about a week from now - Cyber Monday (the Monday after Black Friday). In the past, we have recommended cybersecurity best practices for purchasing goods online, and many other vendors will cover how to securely use credit cards and touchless payment systems to protect your identity and purchases.
This year however, we want to focus on merchants. Consumers will always be a target for theft during the holiday season, but how are merchants themselves being compromised, and how can they protect themselves against the latest threats?
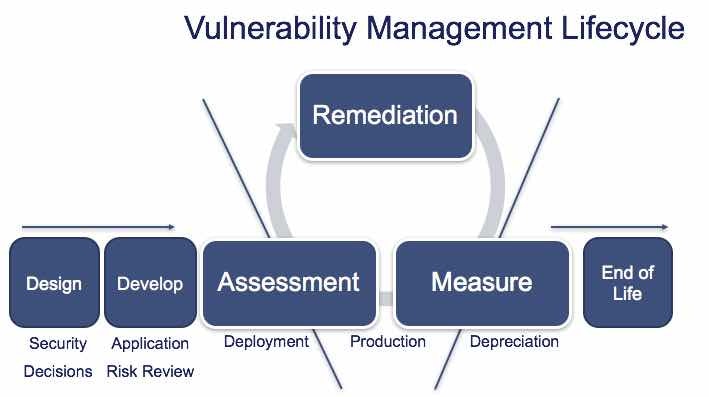
Let us start with basic cybersecurity hygiene and discuss the vulnerability management lifecycle. See the graphic below.
 Design
Design
The beginning of every vulnerability management lifecycle starts with the design. Whether this is a custom application, purchased program, or even DevOps with automation; the design or purchase should take into consideration basic security hygiene. This includes security basics regarding coding, storage of sensitive information, to the crown jewels of the enterprise and merchants. If security questions are not asked up front, the implementation of any solution could pose an unacceptable risk to the business and lead to a breach of client data.
Development
The development, proof of concept, and deployment of any new technology should be tested, code reviewed (if applicable) and assessed for risks before product implementation. This not only includes vulnerability assessments but also configuration hardening and placement in secure zones within the environment. It is one thing to accept the risks of a known application, but entirely another to place it on a high-risk network or directly on the Internet. Development, and accompanying deployment, begin the cyclical portion of a vulnerability management lifecycle.
Assessment
As resources are placed in production, periodic vulnerability assessments are required. An assessment is the act of actually looking for risks through any vehicle like a network scanner or patch management solution. Vulnerability management is the lifecycle of an assessment including remediation (mitigation) and re-measurement. For merchants, if these are not done on a routine basis, gaps in security will form and be targeted by threat actors.
Measure
The vulnerability management lifecycle requires periodic and frequent measurements to determine if new vulnerabilities are present, and if mitigation and remediation strategies are effective. Typically, measurements are performed using service level agreements to age a vulnerability:
- Date of public disclosure
- Date of Audit Release in an Assessment solution
- Discovery date of vulnerability
- Date of mitigation or remediation
- SLA measurement for date of discovery to closure
- Age of outstanding risks critical to the business
- Number of acceptable Exclusions or deviations
This will help make sure any exposure is minimized to a merchant by tracking when new risks are present and when they are closed.
Remediation
The action for a vulnerability can come in multiple forms:
- Remediation – the actual application of a security patch (update) to fix a vulnerability
- Mitigation – the removal of software, changing of a configuration, or the intentional modification of a resource to block the vulnerability (local HIPS for example) and potentially its corresponding exploit (if available)
- Exclusion – the acceptance of the vulnerabilities risk (also called a deviation) due to remediation or mitigation strategies that will impact the business
These are currently the only acceptable classifications for a vulnerability remediation. Any identified vulnerability that does not fall into these categories is aging and considered open and an attack vector for a threat actor.
Rinse and Repeat {Cycle}
The vulnerability management lifecycle requires that assessment, measurement, and remediation be implemented by policy and enforced periodically. This process is continuous and is expected for every asset, resource, and application throughout the environment.
The Risk of "End of Life" Technologies
End of life technologies represent an exceptional risk to any business regardless of the mitigation strategy. The underlying risk will always exist until the technology is removed and replaced with supportable business resources. For merchants, this is most commonly seen in point of sale systems based on EOL technology like Windows XP.
Threat actors can leverage a vulnerability and accompanying exploit to penetrate a merchant environment. Once they establish a beach head, they can steal personally identifiable information including credit card data for future nefarious activities. The longer they can stay present without being detected, the more data they can steal. And, as the holiday season is the busiest for transactions, more occur in a shorter period of time making the target even more attractive.
For more information on how BeyondTrust can help you better automate the vulnerability management lifecycle, download our white paper, Change the Game in Vulnerability Management, or contact us for a demo today!

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








