
If you have not heard of Pokémon Go, you might as well be in living in the Stone Age. In merely seven days, the volume of users on this game has exceeded Twitter and generated millions of dollars for Nintendo. The augmented reality game is addictive and has sparked several crimes, including robbery and muggings. In addition, it poses a massive security risk for any user that logs into Google+ to create an account.
What’s the risk?
Pokémon Go requests Full Access to your Google account, which includes everything from access to your emails (read, write, send and delete) to your Google Wallet. While Nintendo has issued a statement saying that they are not harvesting this information, and will change the permissions to the application soon, the simple fact is that the application has unrestricted access to everything in your Google account. And I mean everything!
Now, if you use your Google account for business, and decided to play the game with the same Google account, you have potentially exposed everything in your business to Nintendo. While the risk is realistically low that something will happen, the unintentional consequences of unknowingly allowing a third party potential access to your business is quite high.
Think of it this way. If you have a brick and mortar business, would you leave the backdoor of the building unlocked and let someone know it was unlocked? Of course not. Well, Pokémon Go does exactly that for cybersecurity. It leverages social media login capabilities of Google+ to create an account and exposes everything in Google+ to them. You have effectively given permissions to a third party for everything you store in Google – from your calendar to text messages.
How to reduce the risk of allowing a third-party to access your account?
Unfortunately, you are now aware of the risk and must remove Pokémon Go privileges from Google Security until this can be properly fixed. Until Nintendo patches the application’s permissions, you best bet is to:
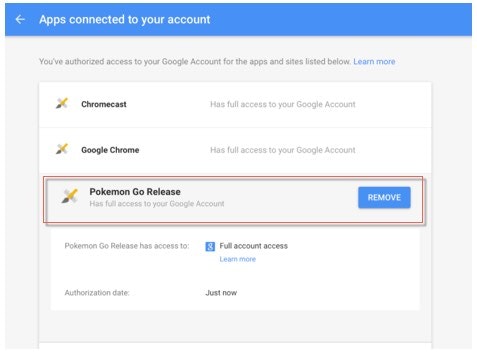
- Remove Full Access and avoid playing the game. Simply click on Pokémon Go and Remove access. See below for a screenshot on how to disable this.
- Create a secondary Google account with minimal information in order to play the game.
- If you have an MDM deployment, prohibit employees from loading the game.
- Do not use the “Lore” feature in the game. This has been associated with physical robbery crimes and exposes the user’s information to other Pokémon Go players.
Most people do not have multiple Google accounts, and if it is being used for business too, your risks are unjustifiable to use this application. In addition, if you remove permissions, every time you now launch the game, it will reinstate privileges.
While this game has taken adults and children by storm, it also leaves a striking message regarding cybersecurity. A simple game can expose too much information, have too much access to our accounts, and create an unnecessary risk if users chose to use the same accounts for business and pleasure. As a security professional, we all need to be aware of these risks and the potential harm they can cause.
We’ve built a business around helping customers understand the consequences of misused enterprise passwords. For guidance on how we can help you eliminate the sharing of accounts, contact us today!

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








