 It’s not news to anyone in the security game that patching known security vulnerabilities in a timely manner is critical to protecting IT systems and networks. So how is it that the most exploited vulnerability in 2014 (CVE-2010-2568) was also the most exploited bug in 2015? Or the fact that on average it takes organizations 110 days to close a single vulnerability. Is it because security teams are drowning in data? Are they worried about patches breaking other things? Or do they lack the tools to verify that a patch actually worked? Yes, yes and yes.
Want to stop drowning in vulnerability data? Try Retina CS for free!
Although software vendors continue to increase the frequency and stability of their security fixes, it does little good if no one installs them. Unfortunately, most vulnerability management solutions only provide guidance on how to mitigate vulnerabilities - leaving you to manually download, install and verify corrective patches, which can take time and leave you vulnerable in the process. Organizations need simpler and more automated ways to connect the dots between their patch processes and their vulnerability management systems.
Interested in learning how Retina can help you accelerate patching vulnerabilities? Request a demo!
Measure the Benefits Before You Patch
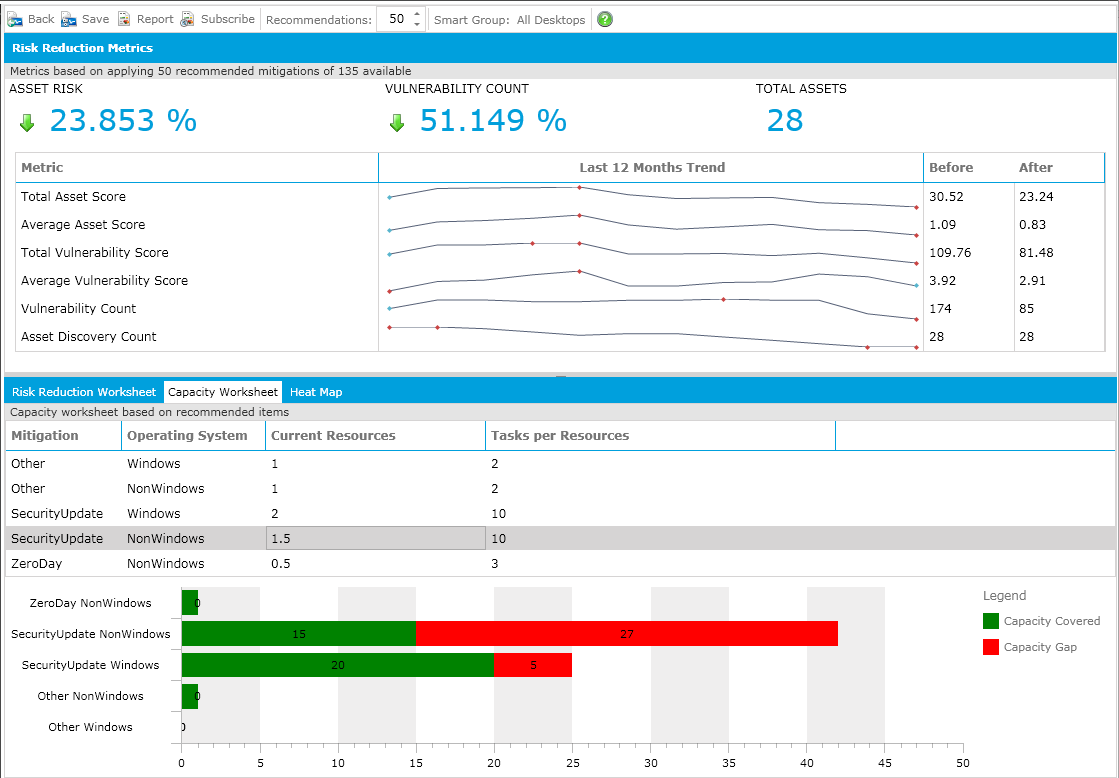
With Retina’s advanced threat analyzer, organizations have the luxury of being able to gauge the impact a particular patch will have on their security posture, before actually deploying and installing it. How much will applying patch XYZ reduce your overall asset risk? And how far will it go in reducing your overall vulnerability count? Get those answers and more – before you start the work. (click to enlarge)
It’s not news to anyone in the security game that patching known security vulnerabilities in a timely manner is critical to protecting IT systems and networks. So how is it that the most exploited vulnerability in 2014 (CVE-2010-2568) was also the most exploited bug in 2015? Or the fact that on average it takes organizations 110 days to close a single vulnerability. Is it because security teams are drowning in data? Are they worried about patches breaking other things? Or do they lack the tools to verify that a patch actually worked? Yes, yes and yes.
Want to stop drowning in vulnerability data? Try Retina CS for free!
Although software vendors continue to increase the frequency and stability of their security fixes, it does little good if no one installs them. Unfortunately, most vulnerability management solutions only provide guidance on how to mitigate vulnerabilities - leaving you to manually download, install and verify corrective patches, which can take time and leave you vulnerable in the process. Organizations need simpler and more automated ways to connect the dots between their patch processes and their vulnerability management systems.
Interested in learning how Retina can help you accelerate patching vulnerabilities? Request a demo!
Measure the Benefits Before You Patch
With Retina’s advanced threat analyzer, organizations have the luxury of being able to gauge the impact a particular patch will have on their security posture, before actually deploying and installing it. How much will applying patch XYZ reduce your overall asset risk? And how far will it go in reducing your overall vulnerability count? Get those answers and more – before you start the work. (click to enlarge)
 Manage Patching from a Single Console
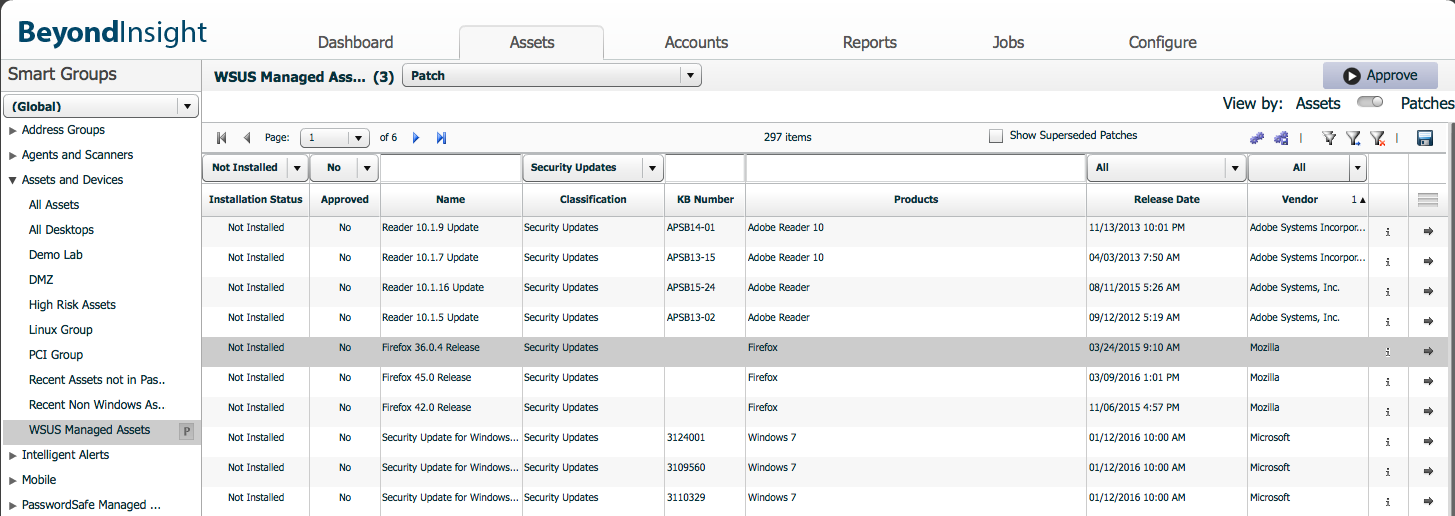
Retina’s integration with Microsoft System Configuration Manager (SCCM) and Windows Server Update Service (WSUS) lets administrators deploy the latest Microsoft product updates directly from the Retina CS console. And because Microsoft applications only represent a small percentage of enterprise software, Retina can also deploy patches for non-Microsoft applications like JAVA, Adobe, Chrome, Oracle and many others.
Manage Patching from a Single Console
Retina’s integration with Microsoft System Configuration Manager (SCCM) and Windows Server Update Service (WSUS) lets administrators deploy the latest Microsoft product updates directly from the Retina CS console. And because Microsoft applications only represent a small percentage of enterprise software, Retina can also deploy patches for non-Microsoft applications like JAVA, Adobe, Chrome, Oracle and many others.
 Verify and Report on What Worked
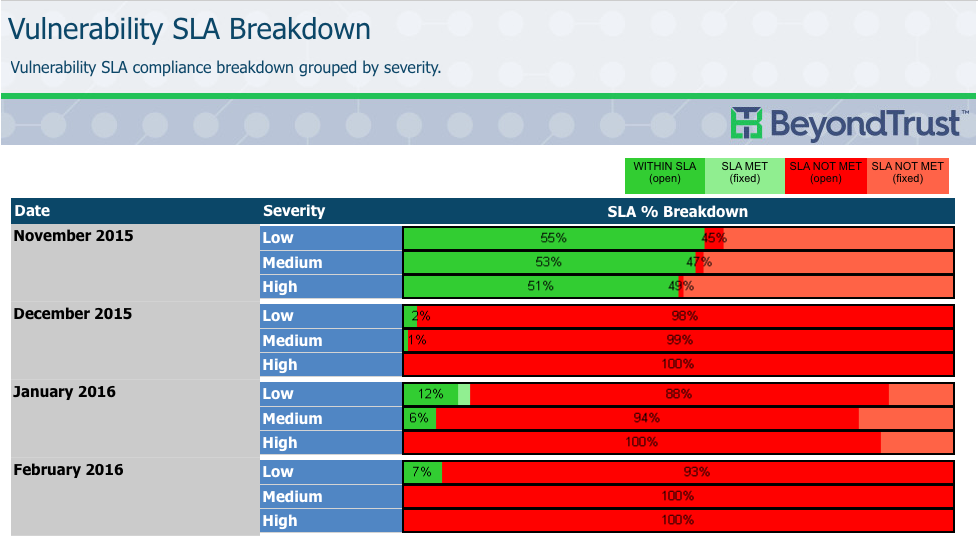
Applying patches is one thing, but being able to easily verify whether they worked or not is something altogether different, but equally important. Retina includes almost 300 standard reports that ultimately help you prioritize which vulnerabilities to patch first, second and third, as well as last. And with Retina’s historical trend reports, you will be able to take a picture of your vulnerabilities, apply patches, and then go back and easily verify which ones worked. (click to enlarge)
Verify and Report on What Worked
Applying patches is one thing, but being able to easily verify whether they worked or not is something altogether different, but equally important. Retina includes almost 300 standard reports that ultimately help you prioritize which vulnerabilities to patch first, second and third, as well as last. And with Retina’s historical trend reports, you will be able to take a picture of your vulnerabilities, apply patches, and then go back and easily verify which ones worked. (click to enlarge)
 How has Retina Eased the Pain for Others?
How has Retina Eased the Pain for Others?
“We are using Retina to validate the effectiveness of our patch management program, thereby having an independent “check” to ensure that we are comprehensively reducing vulnerabilities.” - Large Enterprise Aerospace & Defense Company
“Prior to Retina CS security patches were applied but nothing went back to verify a patch fixed the vulnerability. With Retina, we are able to take a snapshot before, apply the patch, and review our remediation efforts to ensure we properly addressed the vulnerability.” - Brent Nair, Chief Information Officer, City of Memphis, Tennessee
“BeyondTrust makes reporting actually understandable and patch management with superseded patching recognition is most helpful.” - Fortune 500 Health Care CompanyStop being a statistic. Simplify and accelerate your patching process and take a bite out of your vulnerabilities before your adversaries take a bite out of you. Need more information? Download our latest white paper, 10 Reasons to Rethink Your Vulnerability Management, and see how Retina’s cutting-edge capabilities can keep you steps ahead of the bad guys. For more, contact us today!

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








