On September 1st, a new bug was quietly leaked that has far reaching ramifications for all Android users. The bug is in the open source Android Browser that is a part of the webkit, Android Open Source Platform (AOSP). The vulnerability allows malicious sites to inject JavaScript into other sites. The result is the ability for the malicious JavaScript to read cookies, password fields, submit forms, keystroke logs, and do almost anything else you can manipulate JavaScript to do.
This manipulative technique uses a vulnerability in the browsers Same Origin Policy (SOP) to execute scripts from two different sites like and http://mybank.com. It breaks the protective design of SOP that manages a website's elements by protocol, domain, and port. In theory SOP should never allow this to occur, but on an Android Browser, it can.
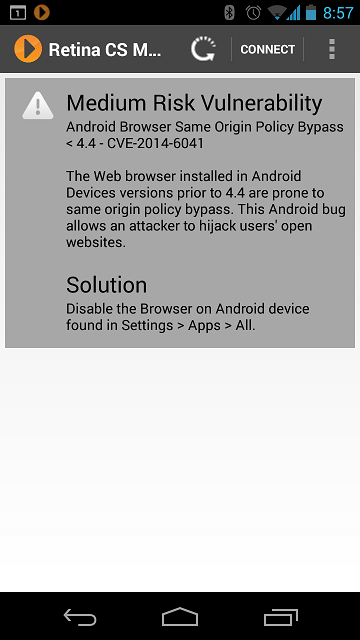
Credit for this vulnerability goes to Rafay Baloch, the researcher who discovered the SOP implementation flaw (CVE-2014-6041). His technique uses JavaScript in a malicious design to bypass SOP and compromise another site with no detection and complete access to other sites the user may visit (or be automatically redirected too). Thus, any site the end user visits, after visiting a malicious site first, the flaw could be stealing sensitive data and you would never know it.
As of this post, Android 4.4 and Chrome are not affected which should be a relief to a relatively small sample of leading edge Android users. Patches have been made available for earlier versions of Android to correct AOSP, but the honest truth is the vast majority of end users will have no idea how to apply them:
1.) https://android.googlesource.com/platform/external/webkit/+/1368e05e8875f00e8d2529fe6050d08b55ea4d87
2.) https://android.googlesource.com/platform/external/webkit/+/7e4405a7a12750ee27325f065b9825c25b40598c
Users must wait for updates on Google Play, switch to Chrome as their Browser, or wait for Over The Air (OTA) updates from their cellular carrier. These are by no means ideal solutions compared to Microsoft's Patch Tuesday since many versions of cellular phones are just not being updated any more (think Windows XP).
To give you perspective on the problem, look at these statistics from other sites:
> ARSTechnica reports that the flawed Android Browsers accounts for between 40-50% of all Android web traffic despite newer releases of Android (4.2+) that use Chrome.
> Google reports that only one quarter (24.5%) of Android users are running version 4.4 which is not vulnerable to the attack. A slim portion of all Android users.
 To make matters a little worse, the default Android Browser present in older versions of Android is likely to be embedded in third-party products. Those statistics are not readily available but conceivably could be in media boxes, multi-function devices, and even android on a USB stick devices that may be used worldwide.
To make matters a little worse, the default Android Browser present in older versions of Android is likely to be embedded in third-party products. Those statistics are not readily available but conceivably could be in media boxes, multi-function devices, and even android on a USB stick devices that may be used worldwide.
Identification of the flaw can be tricky due to embedded versions of AOSP in other applications and third party browsers. In order to report on these vulnerable devices, BeyondTrust has the Mobile Assessment Agent which brings industry-leading zero-gap vulnerability assessment capabilities to your Android phone. With this technology, IT security teams can identify and analyze potential vulnerabilities on their organization's mobile assets, just as they do on servers and desktops. Individual smart phone users can also leverage the Agent to find vulnerabilities on their own devices. This is all for free and include the Android Browser vulnerabilities. For enterprise users, all of these findings can be securely reported to BeyondInsight.
As a small footnote, for older Android users, you can avoid much of the exposure by switching to Chrome, Firefox, or Opera. These are not vulnerable. They provide a simple mitigation path until a formal patch (if ever) is released. Learn more about BeyondTrust and our Mobile Vulnerability Assessment capabilities. Mobile devices represent the last mile of devices connecting to your infrastructure and a risk we all need to manage.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








