 How much would your organization pay in ransom to stop the early release of its intellectual property? Can you place a monetary value on a breach of this type? In the case of the weekend Netflix breach notification, they paid nothing. Does the breach of an entirely new season of Orange is the New Black actually hurt Netflix, or does it provide a low cost, unintentional and extreme promotion for one for their most popular shows?
How much would your organization pay in ransom to stop the early release of its intellectual property? Can you place a monetary value on a breach of this type? In the case of the weekend Netflix breach notification, they paid nothing. Does the breach of an entirely new season of Orange is the New Black actually hurt Netflix, or does it provide a low cost, unintentional and extreme promotion for one for their most popular shows?
Not another Sony?
Sony experienced similar euphoria with their breach in 2014 and theft of a few movies; but their breach had deep security ramifications, from emails to financials. The negative press and effect on senior executives rippled through the company and industry with unparalleled waves. We would hope media companies would have learned some hard lessons from that breach; but apparently not. To that end, it is important to note that Netflix themselves did not leak the series in a breach like what happened with Sony. The digital copies were stolen from Larson Studios, an audio production company authorized to have copies for automatic dialogue replacement. The hackers (TheDarkOverlord), claims Larson agreed to pay the ransom but in fact did not and now they are trying extort money from Netflix. To make this situation worse, the studio produces work for several major US TV studios. This breach, and subsequent torrent episode releases (the first 10 from the latest unreleased season) may just be the tip of the iceberg for stolen media. And, for those in the business, this fact emphasizes the weaknesses in any supply chain and the ramifications of security flaws along the entire workflow when multiple companies share information with a single vendor that is not properly segregated. As for the breach itself, in a public comment from the hacker, they indicated "You're going to lose a lot more money in all of this than what our modest offer was. We're quite ashamed to breathe the same air as you. We figured a pragmatic business such as yourselves would see and understand the benefits of cooperating with a reasonable and merciful entity like ourselves. And to the others: there's still time to save yourselves. Our offer(s) are still on the table - for now." Clearly, reasonable is out of the question and extortion and ransom are their only goals.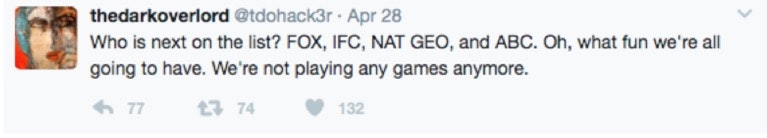 The breach confirms findings from the 2017 Verizon Data Breach Report that 73% of all attacks are financially motivated and no business, or vertical, is immune from attackers.
As with any breach, a detailed analysis will reveal recommended mitigations and remediation to prevent future incursions. Most of the time these include security basics such as implementing privileged access management and vulnerability management. Sensitive data of any type should always have additional controls, including file integrity mnitoring, least privilege, network segmentation, and auditing. These best practices are low hanging fruit. If organizations can get these basics done right, many of these breaches, and the incidents leading up to them, can be prevented. If you need help figuring out how, contact us today.
The breach confirms findings from the 2017 Verizon Data Breach Report that 73% of all attacks are financially motivated and no business, or vertical, is immune from attackers.
As with any breach, a detailed analysis will reveal recommended mitigations and remediation to prevent future incursions. Most of the time these include security basics such as implementing privileged access management and vulnerability management. Sensitive data of any type should always have additional controls, including file integrity mnitoring, least privilege, network segmentation, and auditing. These best practices are low hanging fruit. If organizations can get these basics done right, many of these breaches, and the incidents leading up to them, can be prevented. If you need help figuring out how, contact us today.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








