Throughout history humans have sought to socially engineer each other, exploiting social norms and applying pressure to reveal information or gain advantage. From travelling conmen and master spies to cyber threats and phishing emails the fundamental problem is the same, humans can be manipulated.
In the digital world we are rapidly evolving multiple sophisticated layers of defence around systems and data. This means that gone are the days when the hacker, sat at a blinking VAX terminal can break into the main frame using a couple of simple commands. Instead the modern threat actor knows that not only do the users have direct access to the data they covet but they are much easier to exploit than breaking in through firewalls and access controls from the outside.
If we look at the kind of attacks that are plaguing businesses in 2016 we can see the hall marks of social engineering at play. Take for example phishing emails, these often use fake invoices, tax demands and legal threats all designed to illicit pressure on the end user to open the malicious file. These emails are often sent out at the start of business on a Monday to catch out users ploughing through an overflowing inbox and not alert to the danger.
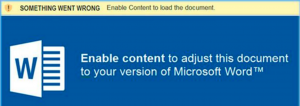
Once the file is open we see the manipulations continue as the attackers will often echo dialogues that users are familiar with in order to get them to enable active content such as macros and launch the attack. Phrases such as “this document is encrypted” or “this document is password protected” play on the users limited knowledge of security and trick them into launching a malicious script when they think they are improving security.
As well as these more obvious approaches there are many other subtle tricks that go unnoticed where employees are scouted out through social media or fake recruiters trying to harvest information that could benefit an attacker. In many organisations physical access is also a concern as social conventions say that not holding a door open or questioning someone is rude leading to attackers being able to socially engineer their way into secure locations.
One of the classic responses to these kind of attacks is to blame the users for opening the email attachments or falling for the scam. Of course hindsight is a wonderful thing and with the increasing sophistication of attacks few businesses are safe.
In reality the best thing is to build proactive defences around the user. If we focus on detecting all the suspicious emails and educating users, then we will always be one step behind the attackers who can rapidly change tactics to evade detection. If we reduce the attack surface on the endpoint so the user is not exposing admin credentials, not able to accidentally launch unknown malicious applications by isolating content such as email attachments and web links away from corporate data then we have a robust defence even if the user is socially engineered.
With social engineering and undetectable threats becoming the new norm, moving from a reactive detection stance to a proactive hardening position not only improves security but alleviates pressure on users and IT who often live in a constant state of fear. Just as a bank builds a vault and solid security around the money before layering on alarms and detection we can build solid security foundations on the endpoint before we consider detection.
In the meantime, I will be emailing you an urgent invoice so please think twice about what is protecting your endpoint and data before enabling content for “security reasons”.

James Maude, Field Chief Technology Officer
James Maude is the Field Chief Technology Officer (FCTO) at BeyondTrust. With his broad experience in security research, both in academia and industry, James has spent the past decade analyzing cyber threats to identify attack vectors and trends in the evolving security landscape. He is an active member of the security community and hosts Adventures of Alice and Bob, a podcast that shines a light on the people making a difference in security. As an expert voice on cybersecurity, he regularly presents at international events and hosts webinars to discuss threats and defense strategies.








