We all hear about US Federal Government data breaches in the news. When malicious hackers get into an agency system they have access to our nation’s most critical infrastructures and the personal, identifiable information of tens of thousands of citizens. Although agencies like NIST, OMB, and DoD collaborate on mandates and frameworks to address security in our agencies, it appears that adoption is slow.
BeyondTrust recently surveyed Government Information Technology pros as part of the 2016 Privilege Benchmarking Study. In the report you will see how top and bottom tier organizations view privileged access in their environments. All indications are that our government agencies remain at high risk for breached through privilege account misuse or exploitation.
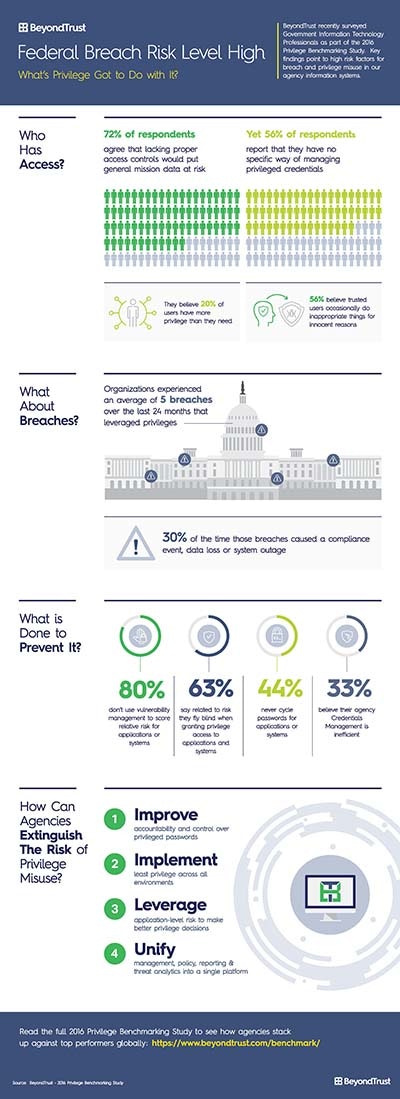 72% of respondents agree that lacking proper access controls would put general mission data, including PII, at risk
72% of respondents agree that lacking proper access controls would put general mission data, including PII, at risk- Yet 56% report that they have no specific way of managing privileged credentials
- And 63% say related to risk they fly blind when granting privileged access to applications – and systems
Want more detail on the best practices, including how to make them work in your government agency? Download the results paper – or, take a look at the infographic for a summary.
Why the Threat Still Exists
We’ve all heard the definition of insanity…so why do we continue to see numbers like these in the face of highly publicized breaches? The truth is, our Federal IT teams face immensely complex environments made up of technology from across the ages and from a multitude of brands. Let’s face it- agency information systems are the golden goose. If malicious actors can penetrate these environments there is a treasure trove of data- so they try to gain entry at an astounding rate.
Our government networks are under siege. Making a change while still supporting an organization’s mission is hard. Change itself is wrought with risk, but I challenge that we’ve come to the day where the risk of change is outweighed by the risk of doing what we’ve always done. It is time to move swiftly to adopt technologies to thwart the insider threat, and malicious actors that cloak themselves in exploited privileges to look like insiders.
Experience Matters
Here at BeyondTrust we have a seasoned Federal Security Team that understands your needs and challenges. The BeyondInsight IT Risk Management Platform helps agencies secure their environments and fulfill regulatory requirements through its integrated suite of IT security solutions that reduce user-based risk and address security exposures. With behavioral analytics to understand anomalies, compliance reporting, and the ability to leverage third-party data, the platform reduces risks while helping to maximize the value of existing security investments. The BeyondTrust platform integrates two foundational security methodologies: privileged access management and vulnerability management.
Want more detail on the best practices, including how to make them work in your federal agency? Download the results paper – or, take a look at the infographic for a summary.
If your agency is struggling to prioritize risks in the face of ongoing breaches, contact us today for a strategy session.

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








