Hot on the heels of the annual Verizon Data Breach Investigations Report comes this year’s Ponemon Institute Cost of Data Breach Study. Not surprisingly, costs are going up – to the tune of a 23% increase in total costs of data breaches since 2013, and a 12% increase in per-record cost.
I’ll avoid the blow-by-blow – check out Kelly Jackson Higgins’ article on Dark Reading for an excellent re-cap of the report. Instead, I want to zero-in on the factors that mitigate the cost of the breach. Particularly, what’s missing from that list of factors.
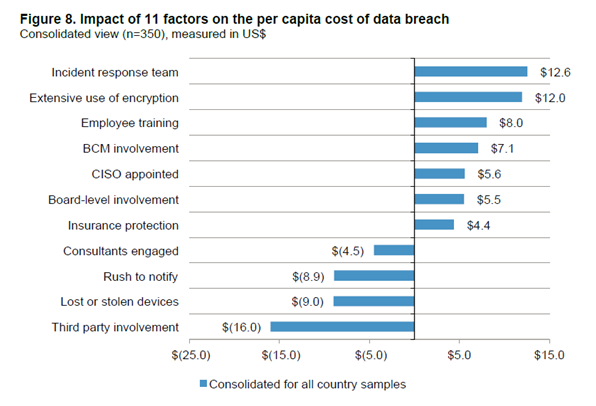
As the report will show you, factors such as having an incident response team, extensive use of encryption, employee training, business, continuity management, CISO leadership, board-level involvement, and insurance protection will help decrease the per capita cost of data breach. Ponemon says that third party involvement in the incident, lost or stolen devices, a rush to notify affected parties, and consulting services increase the per capita cost of data breach. But what’s not on this list speaks volumes. Check out the chart below. Source: Ponemon Institute.
What’s missing from this list?
I would argue that one of the most significant factors to reduce data breach costs is having greater controls and visibility over privileged access – the accounts, users, systems, applications, and others with the keys to your kingdom. Why is that not a factor on this list?
You can have all the encryption money can buy, the best education and training available, an aggressive CISO and knowledgeable board, but if you don’t have control and visibility over who is accessing the critical systems that house your data, it all goes to waste.
That privileged access isn’t on the list of factors isn’t that surprising, our own Privilege Gone Wild study showed that over 25% of organizations have no privileged access controls in place. Yet, nearly half of the survey respondents admitted they have employees with access rights not necessary for their current role. What’s more is that 84% of respondents believe the risk to their organizations from privileged users will increase over the next few years – especially in the area of access to business critical information.
Mitigating the costs with privileged account management
I’m certainly not saying that you should ignore all the other factors – rather do NOT ignore this one. To mitigate the costs of data breaches, start by examining your privileged account management strategy, answering the following questions:
1) Can you quickly discover privileged accounts, passwords, systems, and applications, and place them under unified management?
2) Are you considering application risk using vulnerability data to decide on privileges? (Imagine denying a privilege escalation request simply because you knew the application was unpatched and had known vulnerabilities.)
3) What is your strategy for implementing and enforcing least privilege across your desktops, servers, Windows, and *NIX platforms? How simply can this be done without impacting users?
4) Are you actively eliminating cross-platform complexities by consolidating and enabling authentication into Active Directory?
5) Are you able to then audit and recover changes made to critical objects in across AD, Exchange, SQL, WFS, and others?
Answering these questions will help you prioritize areas in privileged account management to tackle first. The good news is, to lower data breach costs you can start anywhere in this process. If you’d like to learn how, contact us today!

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








