
I am pleased to announce the latest release of BeyondTrust’s cloud-based vulnerability scanner, BeyondSaaS. Version 3.1, released publicly today, now conducts fast, affordable scans beyond public-facing network infrastructures and web applications, but also now internally as well! Keep reading below for more on this and other enhancements.
Internal Scanning Improves Coverage, Reduces Risks
Originally introduced as an external/perimeter scanner, with BeyondSaaS 3.1 customers can now scan their internal networks as well. With BeyondSaaS 3.1 organizations can deploy one or multiple scanners inside their perimeter, and centrally manage them from the cloud. Available for an additional fee, all customers need to do to begin is download the BeyondSaaS Remote Agent from their BeyondSaaS instance and execute this small agent on an internal system. This agent will download, install, and manage the scanner’s connection with your BeyondSaaS instance.
By leveraging BeyondSaaS for internal scanning, customers can now easily manage multiple scanners from one easily accessible location, the cloud - BeyondSaaS. Gone are the days of having to remotely connect to distributed scanners to perform vulnerability assessments or PCI scans. Now both internal and external facing assets are easily managed via a single interface. With this new addition, BeyondSaaS now offers complete coverage for both internal and external assessments as well as comprehensive external Web Application scanning.
BeyondSaaS internal and external scanning technology is based on the award-winning Retina Network Security Scanner.
Flexible Reporting Options
BeyondSaaS version 3.1 now automatically generates and makes available all reports upon scan completion. With this enhancement, customers are no longer tied to the report they initially wanted to generate as part of the scan process; while customers can still select a primary report to be auto generated and emailed after the scan completes, now they have the option to select any completed scan jobs and browse through all other available reports for viewing within the BeyondSaaS user interface or download all reports as a .zip file. This new capability helps security teams get the data they need to make better decisions, faster.
New Asset View/Grid
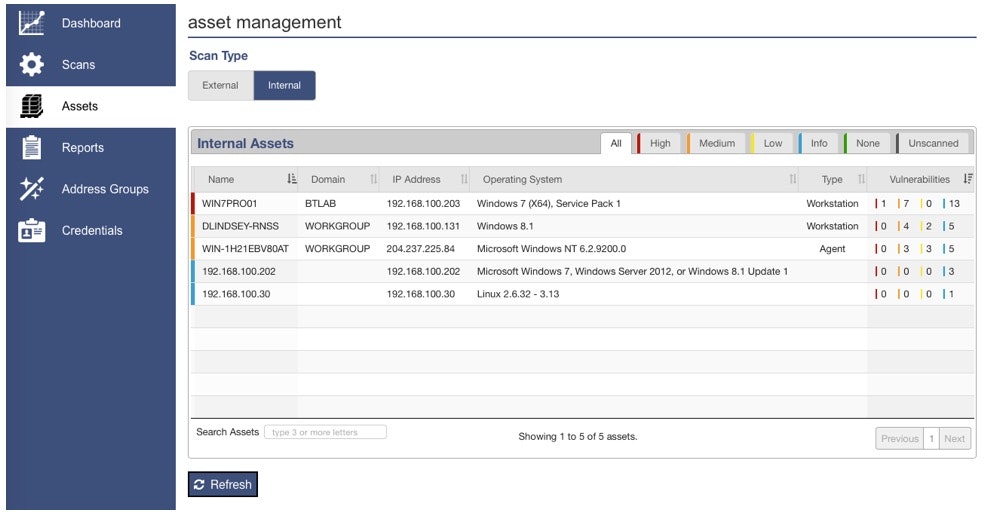
The other major features available in BeyondSaaS 3.1 is the new Assets View. This view dynamically populates as assets are scanned, and displays important information such as the asset attributes of asset name, operating system, IP address as well as a summary of detected vulnerabilities broken down by severity. This new asset grid supports drill down capabilities so that customers can click into any asset to see more information such as an asset’s vulnerability, description and fix information.
This enhancement gives the user an interactive method to review scan results and to reduce the need to open and review static reports. For a representation of the new feature, check out the screenshot below.
You can begin using these new capabilities the next time you log on to BeyondSaaS. For a complete demonstration of these new features – including how to add internal scanning to your current BeyondSaaS usage, watch this brief video. And get the complete details in the new features document.
This latest release of BeyondSaaS is the latest in cloud-based security innovations across our vulnerability management and privileged access management products. Watch for more coming soon!

Alejandro DaCosta, Product Manager
As Product Manager, Alex DaCosta is responsible for designing the company’s Vulnerability Management solutions. Alex joined BeyondTrust via the company’s acquisition of eEye Digital Security, where he held senior positions as Security Engineer in both pre and post sales operations. As a Senior Security Engineer, Alex was responsible for the success of demonstrating, architecting and implementing the Company’s enterprise solutions. Alex graduated from California State University, Long Beach with a Bachelors of Science Degree in Management Information Systems.








