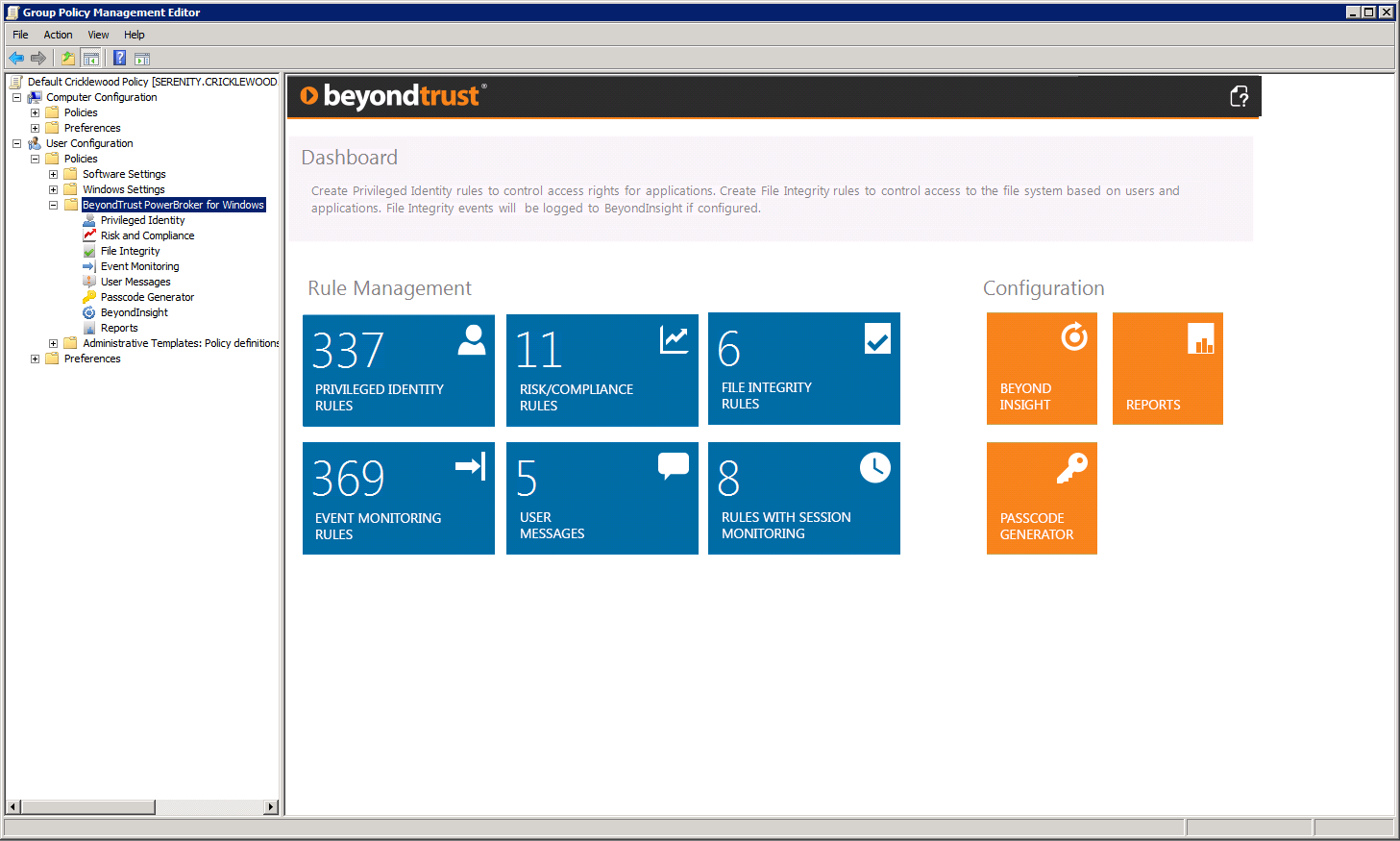
- Session Monitoring (SM) – Advanced screen capturing, keystroke logging, and mouse-click recording of a privileged session for the duration of access. Results are encrypted and sent to the BeyondInsight IT Risk Management Console for later searching, reporting, forensics, download, and DVR-style playback.
- File Integrity Monitoring (FIM) – The monitoring, logging, and even denial of access to the file system based on users, to ensure privileged access does not alter the file system in an undesirable way. FIM is a persistent function within PBW and operates even when no user is interactively logged in. The results are also sent to the BeyondInsight IT Risk Management Platform console for alerting and reporting.
- Event Log Monitoring (ELM) – As users interact with a host, critical functions like services and drivers generally write to the Windows Event Log. PBW contains pattern-based Windows Event Log Monitoring and reporting to track all types of access (privileged and non-privileged). As a privileged user, it is possible to create local users or even disable security tools if PBW rules were written to do so. ELM allows for the logging of these activities and provides a deeper view into system interaction.
- Risk Compliance – The decision to elevate an application via rule can have some shortcomings if the application possesses an unnecessary risk based on vulnerabilities. Risk Compliance is a part of Vulnerability-Based Application Management (VBAM), which allows rules to be created for privileged access based on an application’s published vulnerabilities. This allows auditing of applications based on their risk, regulatory compliance violations, and permissions all through BeyondInsight to determine the health of applications when given administrative privileges. It completes the auditing perspective because you not only can track what privileged users do with complete context, but also audit the applications themselves to round out the documentation trail.
- White paper: “Powerbroker for Windows: Risk Compliance”
- Short videos of the Windows privilege management features referenced in this post

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








