Assets, users, vulnerabilities and exploits; all are common themes in my posts on BeyondInsight. With BeyondInsight v5.1, we unveiled a new way to view exploitable assets. Sure, most vulnerability management solutions link vulnerability data to exploit information, allowing tools like NeXpose and QualysGuard to list an asset, its vulnerabilities, and any related exploits. BeyondInsight does this and then takes it to the next level.
Taking Prioritization to the Next Level
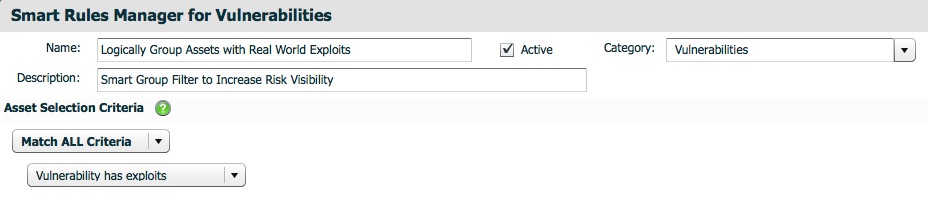
With version 5.1, BeyondInsight adds Vulnerability-Based Smart Rules to its Asset Smart Rules (which we’ve had for years and other vendors are just beginning to introduce). This is an industry-unique feature because it allows users to pivot and group information based on vulnerability results and findings, rather than solely on groups of assets. As a result, they can better prioritize remediation efforts by filtering vulnerabilities and isolating those currently targeted by known, active exploits.
Focusing on the Vulnerability Data You Care About
Now, BeyondInsight users can easily narrow assessment results down to only those Asset Smart Groups containing vulnerabilities with current exploits – with no data bleed or errant findings. The new Vulnerability Smart Rule also incorporates Boolean logic for additional vulnerability details such as vendor, description, CVE, etc. This allows specific operational teams to tailor vulnerability assessment findings to their specific areas of responsibility. For example, an operations team may only want to view desktops that contain exploitable Microsoft Office applications. The Smart Rule can easily be modified to display only those vulnerabilities relevant to Microsoft Office.
Revealing the Implications of Zero Day Threats
For another example, consider the recent Microsoft Word zero-day vulnerability recently published and previously discussed in our blog. Given this threat, BeyondInsight can document the following:
- Which assets the zero-day vulnerability is present on
- Which assets are exploitable based on the zero day
- What is the documented vulnerability and proper mitigation until a patch is available
- Which tools have a published exploit for the zero day
- Whether the zero day is exploitable from within a common malware framework
BeyondTrust redefines how organizations use vulnerability data. This latest feature helps prioritize vulnerability information by filtering not only the vulnerability list for exploits, but also the asset list. It allows organizations to gain context-aware security intelligence by refining assessment results for the teams that need it most and filtering the risks for dangers that require immediate attention.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








