Secure Computing is one of those overused terms that gracefully died on the vine. During a recent customer meeting, we discussed a new context for Secure Computing that’s worth sharing with our blog readers. Here it is in a nutshell:
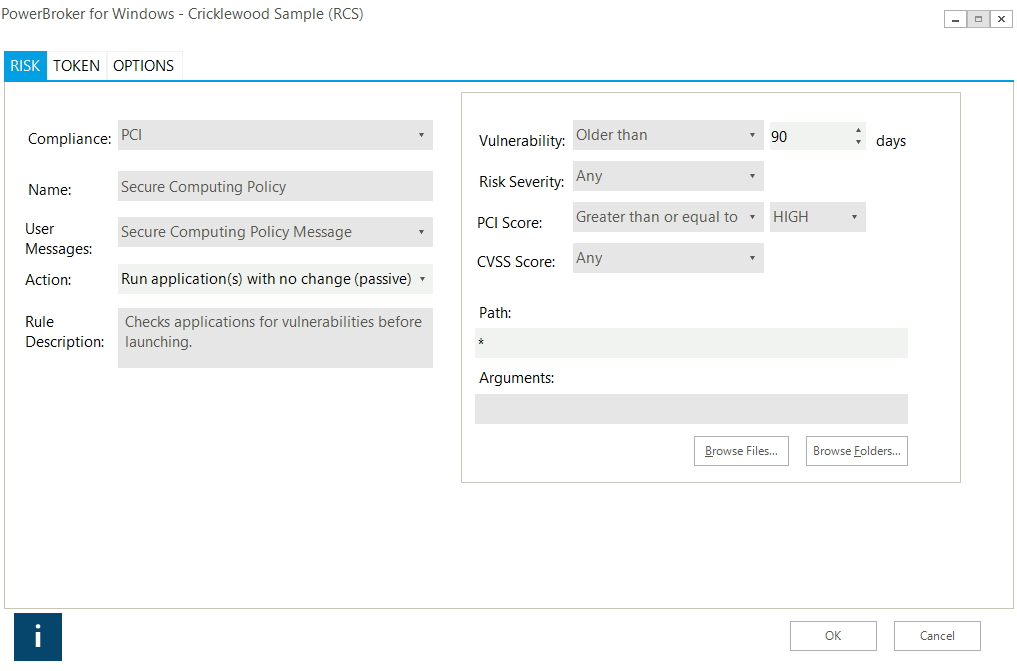
Consider Secure computing in the context of PowerBroker for Windows Risk Compliance. If you’re not familiar with the patent-pending technology, it essentially evaluates an application at runtime to decide what privileges the application should have based on a vulnerabilities, age, risk, and even regulatory relevance. This could include blocking a vulnerable application if it represents too much of a risk to the business. While this extreme action could disrupt operations, in some cases it may be exactly what is needed to prevent an application’s exploitation.
Effective Secure Computing falls between the extremes of providing root access and denying access altogether. To our customer, it means alerting the end user and the help desk that a launched application is in violation of an acceptable patch remediation cycle – and instructing the end user to contact the help desk to get the system mitigated. This places Secure Computing in the hands of all stakeholders by alerting them to risk and facilitating procedures to assist in remediation.
For example, launching a vulnerable version of Adobe Acrobat that is older than 90 days could display a message like this:
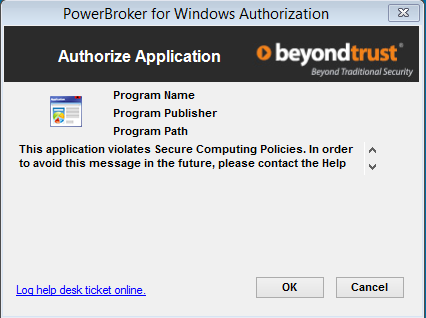
It does not stop the execution, but alerts them much like an antivirus solution and, more importantly, helps track when processes fail for patch management. All the user needs to do is click “OK” to continue.
This approach enables Secure Computing by proactively alerting the end user, the help desk, and the operations team to applications being executed out of compliance. In addition, it allows for application-based vulnerability assessment and can meet continuous vulnerability assessment requirements as users execute applications.
Two additional practices that organizations are striving for (with little success) are using passive scanning technology and deploying complex multi-vendor integrations. These allow for application-based vulnerabilities to be detected as they are communicating across the network. However, they don’t assist with local applications or applications that transmit encrypted communications. PowerBroker for Windows makes this simple. For instance, here’s a PowerBroker rule for PCI compliance concerning critical vulnerabilities over 90 days old (without the need for span ports):
Secure Computing does not have to be the responsibility of the security or operations teams alone. PowerBroker for Windows takes a proactive approach and empowers the end user to notify teams when their applications are not meeting standards.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








