 What do Twitter, Spotify, SaneBox, Reddit, Box, Github, Zoho CRM, PayPal, Airbnb, Freshbooks, Wired.com, Pinterest, Heroku and Vox Media properties have in common on the morning of October 21, 2016?
What do Twitter, Spotify, SaneBox, Reddit, Box, Github, Zoho CRM, PayPal, Airbnb, Freshbooks, Wired.com, Pinterest, Heroku and Vox Media properties have in common on the morning of October 21, 2016?
They Are All Pretty Much Down
Check out this graphic from downdetector.com to see just how many sites have been impacted. (click to enlarge)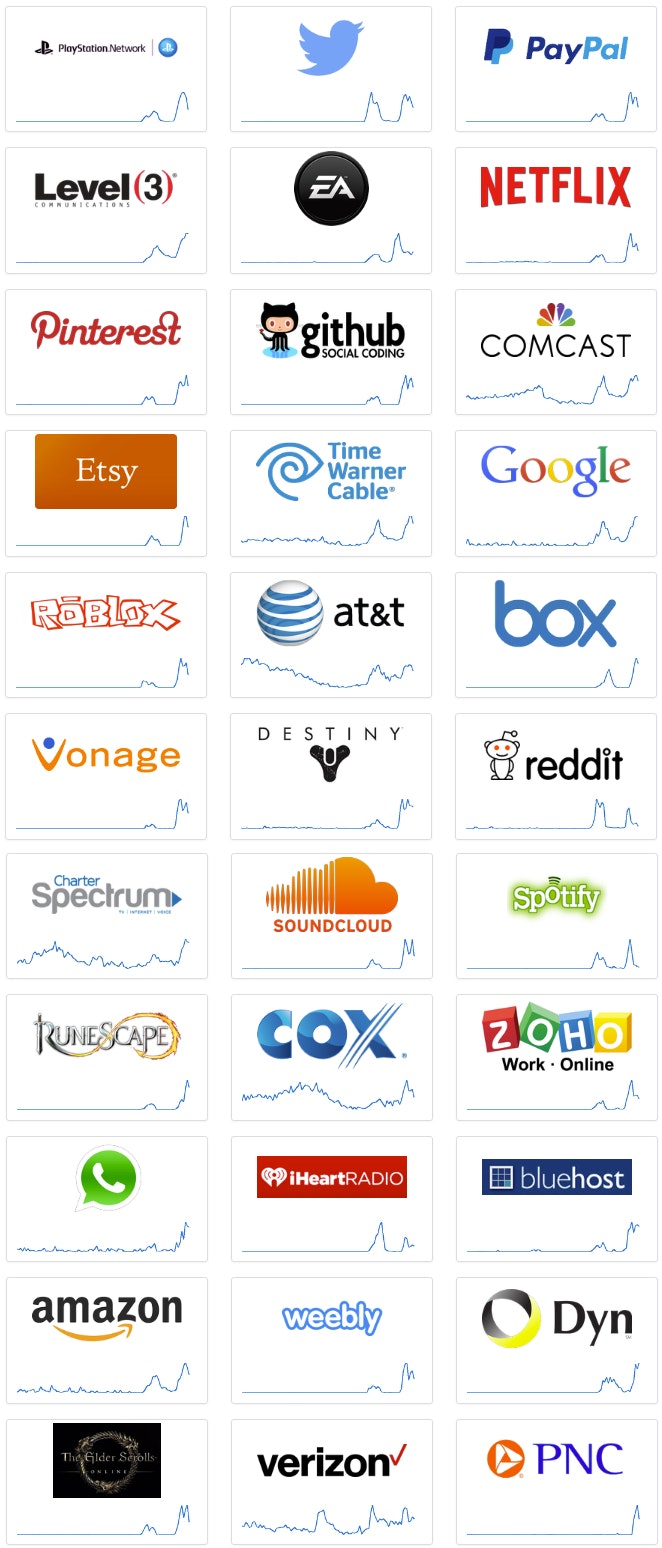 One of the largest risks to the Internet is if critical services are attacked or compromised. As a result, vast numbers of companies, services, transactions, and operations can go completely dark. Today, a massive Distributed Denial of Service attack is affecting much of the east coast of the United States and crippling these websites, their commerce, and making them nearly unavailable according to The Hacker News. This story is now becoming the hot news across CNN and the Wall Street Journal, with journalists scrambling for details on the attack and the outage.
One of the largest risks to the Internet is if critical services are attacked or compromised. As a result, vast numbers of companies, services, transactions, and operations can go completely dark. Today, a massive Distributed Denial of Service attack is affecting much of the east coast of the United States and crippling these websites, their commerce, and making them nearly unavailable according to The Hacker News. This story is now becoming the hot news across CNN and the Wall Street Journal, with journalists scrambling for details on the attack and the outage.
While the true source of the attack is still unknown, theories about the technology currently being used in the DDoS range from DVR IoT devices (used in a similar attack a few weeks ago in France) to a sponsored nation state. There are indications that a sophisticated variant of the Mirai DDOS malware named Hajime has started to propagate, and may have been a cause of these latest outages. Hajime is a self-propagating IoT worm that uses brute-force attacks to infect systems, relying on hardcoded or default credentials in IoT source code.
The US Department of Homeland Security warned on October 14, 2016 that hackers where infecting internet connected routers, printers, and smart TV’s to build armies of bots for potentially such a purpose. The financial impact is something everyone should take notice of. When more details emerge about the who, what, when, and where we will certainly keep you up to date. For now, everyone wants their services restored and a deep comprehensive report on how this happened, what devices did they use, and who was behind it. Then, and only then, can we figure out how we can stop it from happening again. Stay tuned for more…
Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








