- Passive scanners can’t identify network traffic routed outside of the span port, such as all local subnet traffic.
- Passive scanning can’t handle encrypted traffic; only packets sent in clear text.
- Devices on the network, but not communicating (e.g., in listen-only mode), are never discovered.
- There is a high false positive rate for patched applications that do not modify headers or banners when communicating on the network. This is especially true for Linux variations with clear text protocols such as FTP and Telnet.
- Large quantities of passive scanners are required to sufficiently cover highly routed and geographically disperse networks.
- Environments that’s have invested in 10GB networks or faster can’t use span ports effectively for this technology.
 This philosophy and superior method has the following advantages:
This philosophy and superior method has the following advantages:
- No need for span ports or special network changes
- Throttle Scans, Retina Scan Pooling, and Scan Windows can quickly discover large address spaces.
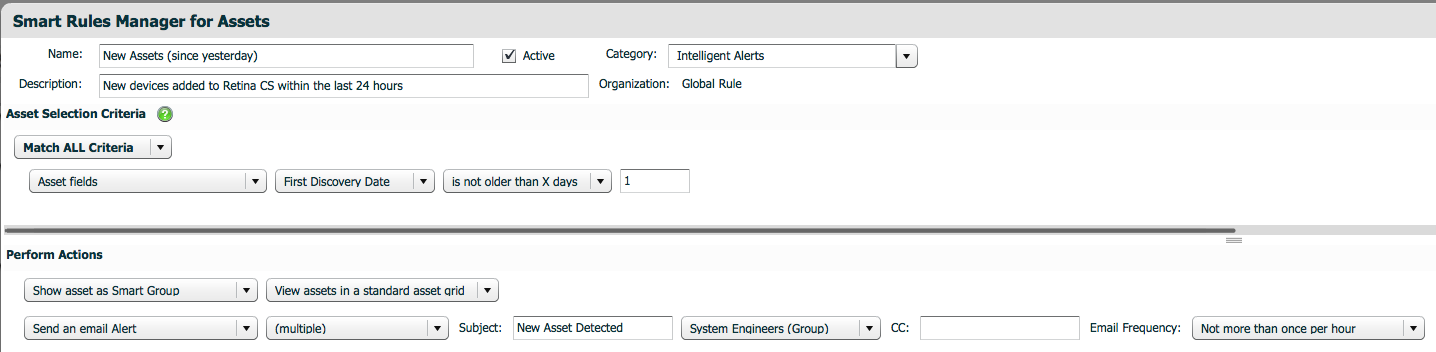
- New devices or services are identified immediately and alerted on or grouped for assessments.
- Vulnerability assessments can be targeted reliably on devices using Smart Rules based on device age, open ports, or other techniques that would be associated with clear text protocols (i.e., Telnet or FTP detected).
- Devices communicating on the same subnet, or not communicating at all, are identified and classified.
- False positives are minimized because a true vulnerability assessment is performed, instead of an inference model that relies on network traffic to identify vulnerabilities.
- Discovery scans can be scheduled multiple times per day for continuous monitoring initiatives to isolate and identify devices requiring assessment.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








