 There has been a fundamental shift in the Unix/Linux market in the last several years as organizations continue to migrate workloads away from Unix and to Linux in order to support hyper scale datacenters and take advantage of other innovations available in Linux. But with the decline of Unix in favor of more open-source Linux to support tier 1 operations security must be a paramount concern. A core security (and compliance for that matter) requirement on Unix/Linux is privilege management, but many customers still rely on sudo for basic privilege elevation and delegation management.
We surveyed more than 100 Unix and Linux experts in January/February of this year to learn what capabilities are needed to improve security on those systems, and ultimately replace sudo. Findings from this study are summarized below. I encourage you to use this data as a benchmark – i.e. how do you stack up?
There has been a fundamental shift in the Unix/Linux market in the last several years as organizations continue to migrate workloads away from Unix and to Linux in order to support hyper scale datacenters and take advantage of other innovations available in Linux. But with the decline of Unix in favor of more open-source Linux to support tier 1 operations security must be a paramount concern. A core security (and compliance for that matter) requirement on Unix/Linux is privilege management, but many customers still rely on sudo for basic privilege elevation and delegation management.
We surveyed more than 100 Unix and Linux experts in January/February of this year to learn what capabilities are needed to improve security on those systems, and ultimately replace sudo. Findings from this study are summarized below. I encourage you to use this data as a benchmark – i.e. how do you stack up?
Unix/Linux is Considered Mission Critical, But a Small Percentage of sudo Still Exists
Although 75% of our experts consider more than 50% of their Unix/Linux servers to be “mission critical” to their organization, 40% of respondents are still using sudo on just a small percentage of servers. What percentage of your Unix/Linux estate is mission critical? How much sudo do you still have on those servers?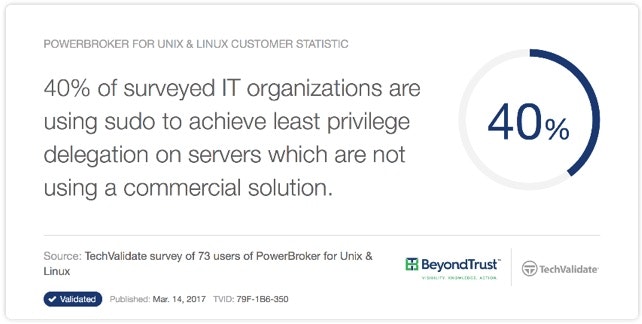
For the Hosts Where sudo is Still Being Used, Our Experts Say Help is Needed
We all know sudo’s weaknesses.- Sudo requires you to manage policy on every Unix/Linux host separately. That can drain important resources from more important projects. Sudo is more labor-intensive to manage than most commercial solutions.
- Sudo lacks official support or QA testing. For a highly-regulated enterprise, or one with strict access control limitations, it seems awfully risky to depend on an open source system that is rife with vulnerabilities. You can’t afford downtime, the cost of a data breach, or the lasting implications.
- Sudo lacks data integrity and log security. It’s hard to prove chain-of-custody when a system’s data is not tamper-proof, and that could lead to longer, more drawn out (read: expensive) audits.

Top Use Cases for Unix/Linux Least Privilege
As with anything, you can’t boil the ocean. So, what are the top uses cases to address in Unix/Linux least privilege to get started quickly? Our panel of experts say that root shell elevation, auditing, logging and command control are the places to start in achieving their operational, compliance and security goals.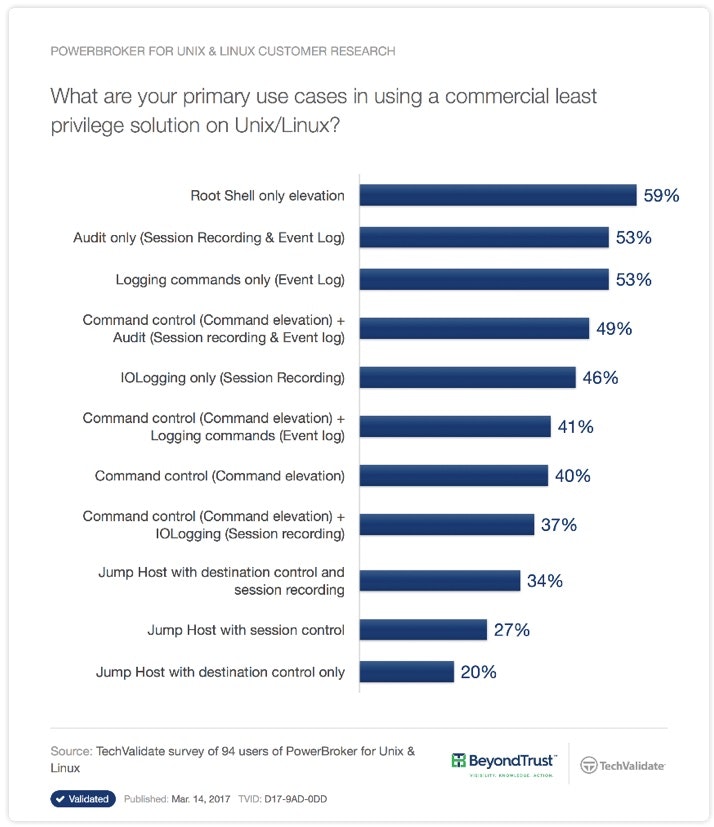
What Benefits to Expect From Using a Commercial Least Privilege Solution
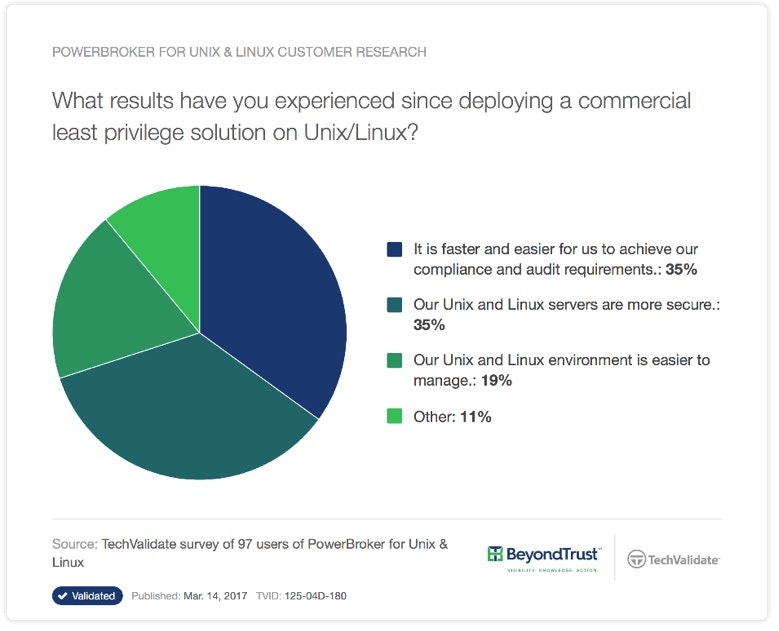
Overwhelmingly, after deploying a commercial least privilege solution on Unix/Linux, our experts say that they experienced improvements in:- Speed in achieving their compliance and audit requirements
- Security of their server estate
- Ease in managing their Unix/Linux environment
Where to go From Here
Unix/Linux is mission critical for most organizations, yet a small percentage of sudo still exists for least privilege delegation. To get started in replacing sudo, tackle the basics first: root shell elevation, auditing, logging and command control. Then, for those servers where you can’t eliminate sudo, implement a centralized repository of multiple sudoers policy files. Ultimately, by deploying these solutions, you should expect to achieve your compliance and audit requirements more quickly, see better security in your Unix/Linux estate, and simplify its overall management. To learn more about what our panel of experts believe are the real, tangible benefits of using PowerBroker for Unix & Linux to achieve least privilege on Unix/Linux servers, visit our customer research portal. Or, contact us for a strategy session on improving Unix/Linux operations, security and compliance.
Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








