A few years ago, I wrote a blog post about finding personal information online. I recently Googled myself again to see who knows what about me. I expected to find some posts and papers I’ve written, and maybe some of my contact details. Instead, the majority of the first-page results associate my name with a certain John Titor, “time traveller” from the year 2036. Sadly, this isn’t true (I’d be a much richer man if it were).
So what does this have to do with BeyondTrust? Well, it’s about the power of search and the importance of being able to find the information you need. With the overload of data available from security solutions today, the ability to quickly find relevant, meaningful information can mean the difference between maintaining a secure environment and suffering a breach.
Let’s take a look at the search capabilities within the BeyondInsight IT Risk Management Platform, which serves as a centralized management, analytics and reporting console for several of our vulnerability and privilege management solutions. To start with, all grids and panels in the BeyondInsight console have powerful search and filter bars:
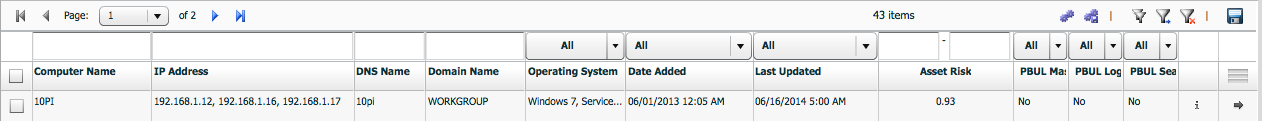
BeyondInsight users can enter any expression or word to search for a specific asset, vulnerability, attack, user, event, etc. While this is basic functionality, the sheer fact that this functionality exists in every management grid is incredible. This means that if you ever find yourself overwhelmed with results, you can filter and search to home in on the data you need. Even more importantly, the old-school floppy disk icon allows you to save the results view to a CSV or XLS.
So what else can we turn up in BeyondInsight? Lets take a look at the Analytics and Reporting Module, which delivers over 260 reports plus a structured big data warehouse. If you’re not sure where to look, you can find specific report by entering a simple query, such as “Export”:
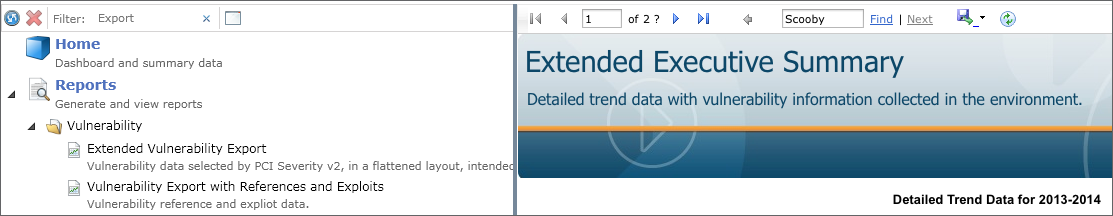
The results for “Export” include all the reports capable of exporting data in flat formats. We can then drill down further by searching within the reports for specific assets, accounts, vulnerabilities, etc.
In this day and age of omniscient Internet search engines, you’d think these seemingly basic search capabilities would be standard in all software solutions. However, take a close look at other security solutions, and you’ll find search capabilities to be lacking to say the least. Users are often forced to generate the report, download the results, and use native tools like PDF search. These long-winded approaches to pinpointing security data can be just as cumbersome as using Google to find information on a specific person. You need to scroll through pages of results, or attempt to narrow your search parameters to exactly what you need.
It would be so much easier to simply save the search filters or parameters to display exactly what you need and what you want others to see. BeyondInsight Smart Rules enable you to do just that: build targeted searches, narrow them to what you need, and save them for later use.
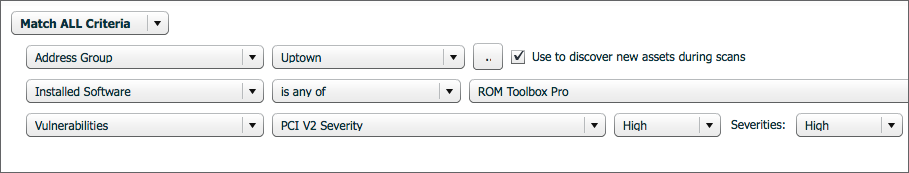
BeyondTrust solutions are designed and implemented to find the data you need to be productive and efficient. Whether you’re filtering results, finding a report template, or building saved queries, the technology delivers actionable results – not guesses based on similar fields or false positives.
As I mentioned above, a Google search of my name returns several false positives. I really need a Smart Filter to remove the garbage and show only the work I’m doing at BeyondTrust. If you’re a BeyondInsight customer, you’ll find that you have it much easier.
> Learn more about BeyondInsight for vulnerability and privilege management

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








