Thanks Palo Alto, we’d love some data!
With BeyondInsight 5.6, Palo Alto Networks showed up to the party – and they brought a fresh batch of firewall data to help flag in-progress threats. The new Clarity Threat Analytics Connector for Palo Alto Firewalls enables our threat analytics engine to consume and analyze network traffic data from Palo Alto’s next-generation firewalls. Clarity can now correlate Palo Alto firewall data with user and application event data – as well as vulnerability, malware and attack information – from BeyondTrust solutions. This means our customers gain an even more informed view of the risks to assets in their environments.
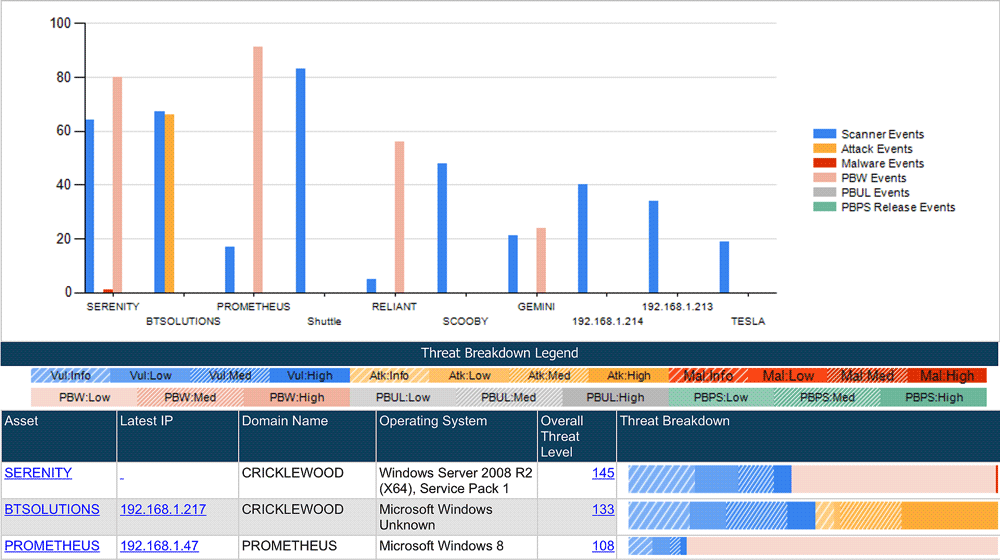 Palo Alto firewall events are automatically correlated to assets and normalized as Attack, Scanner (Vulnerability), and Malware threats
Palo Alto firewall events are automatically correlated to assets and normalized as Attack, Scanner (Vulnerability), and Malware threats
Watch out: new alerts flag user, account and asset threats. So there’s more useful data available to our threat analytics engine, and we’ve also added another way to get actionable data out … with new threat analytics alerting capabilities. Now, when Clarity sees that a user or asset is demonstrating risky behavior, it can alert BeyondInsight users via email, SNMP and/or Syslog feeds. Clarity can let you know about potentially risky events, such as:
- First-time application launches in the environment
- Privileged access requests by applications associated with untrusted users or not digitally signed
- After-hours system access, first-time after-hours access, or simultaneous access to multiple systems after hours
- Launches of processes, services and applications associated with malware
- Unique asset vulnerabilities not present anywhere else in the environment
- And many other key indicators of risky user, account and asset behavior
Hey little guy! We now support Amazon AWS micro and small instances. In 2012, BeyondTrust offered the first cloud connectors for identifying, classifying and assessing assets in Amazon AWS. This industry-unique technology has yet to be duplicated by any other vendor. With BeyondInsight v5.6, we’ve added asset discovery and vulnerability assessment capabilities for Amazon AWS small and micro instances. The connector’s asset discovery capabilities are available to all BeyondInsight customers, and vulnerability assessment capabilities are available to those using Retina CS in the BeyondInsight platform environment. This means the “little guys” won’t get left out of your security initiatives.
We’re releasing least privilege management for Mac next week. Did I just say that out loud? OK, well I might as well tell you that BeyondInsight customers may see some references to “PowerBroker for Mac” in their v5.6 interfaces. That’s because, next week, we’re unveiling a simple, graphical solution for removing admin rights from Mac users (without killing their productivity). This will make BeyondTrust the first to offer unified least privilege management across all major platforms – Windows, UNIX, Linux … and now Mac. Allowing Macs on the corporate network is about to get a little less freaky for IT.
That’s not all! BeyondInsight is also getting Active Directory Federated Services login support and several new reporting and UI updates. You can get more info on these additions, and everything mentioned in this post, by checking out the BeyondInsight 5.6 New Features Overview.

Chris Burd,
Chris brings over 20 years of technology sales and marketing experience to BeyondTrust, where he is responsible for corporate communications and digital marketing. Prior to BeyondTrust, Chris led marketing communications at Core Security, where managed the company’s positioning, branding, and inbound marketing initiatives.








