Least privilege was first put forward as a design principle by Jerry Saltzer and Mike Schroeder 40 years ago [1]. Avecto, along with many others, has championed least privilege and our 5 reasons to love least privilege shows that it is key to mitigating attacks.
Microsoft have acknowledged this approach with User Access Control (UAC) in Windows, attempting to provide a least privilege solution with an ‘all or nothing’ approach using out-of-the-box rudimentary messages. A large number of Windows features for customization and basic system maintenance are locked away behind UAC, with the standard user receiving a UAC message when they try to perform these actions.
The majority of UAC messages occur when a user starts a program that requires administrative rights to perform a task. The program runs with elevated privileges for its lifetime, despite only needing the elevated privileges for a small set of actions, like in Event Viewer purging application event logs.
However some programs have been designed to separate the administrative actions by running it as an independent activity to accomplish a specific and limited function that requires elevated privileges, such as changing the system date and time. This is known as COM elevation.
Normally when a user clicks on an assigned COM elevation action, it will trigger a UAC message which requires access to an administrator account to proceed. Every COM class has a unique identifier, called a CLSID, used to launch the action. This can be seen in the details of the UAC message.
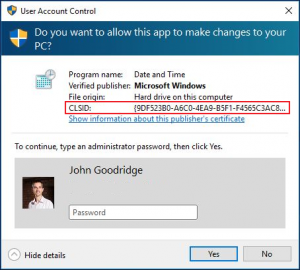
This all sounds fine, as COM elevation actions are isolated to perform a specific and limited function. However not all features that use COM elevation are as limited as they could be! Let’s take a look at the Windows Firewall.
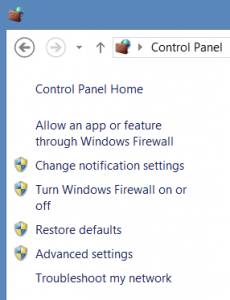
You will notice that the Windows Firewall has a number of functions locked behind the UAC shield indicating their need for elevated privileges to perform an action. For example if you select Advanced settings you will see a UAC message for Windows Firewall with a COM elevation CLSID in the message details. After entering the credentials of an administrator account, the Windows Firewall with Advanced Security window appears.
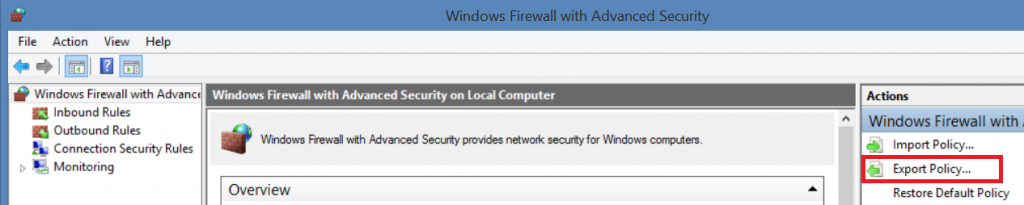
Now remember that the purpose of this window is to perform a specific and limited function that requires elevated privileges. On the right-hand pane there is an Export Policy… item, which shows the File Save As dialog. All looks normal so far?
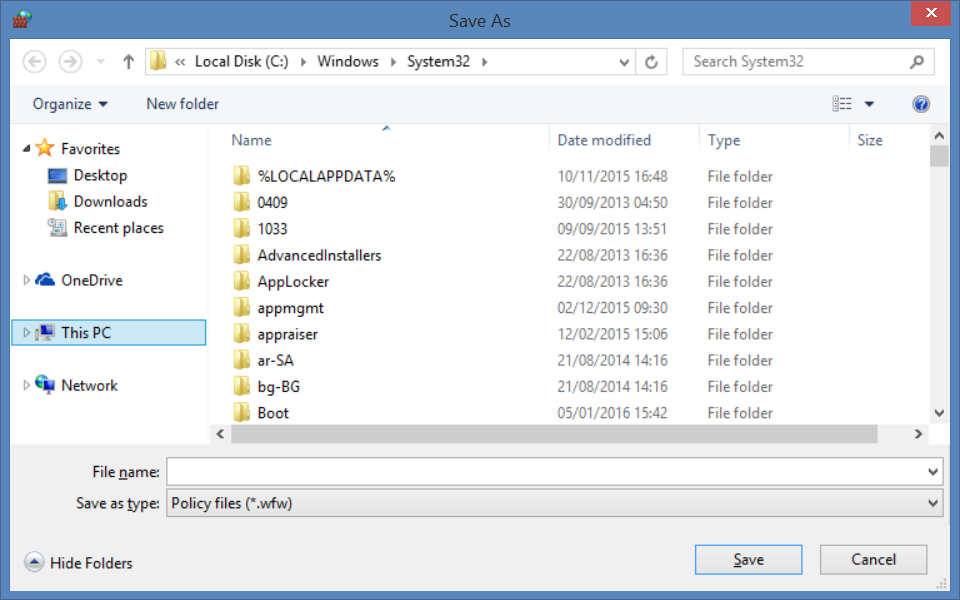
If you change the Save as Type to All files (*.*), you can now browser around the System32 folder and see all the Windows system files including applications like cmd.exe. If you select Open on this from the right mouse button (RMB) menu, an administrator command prompt window is launched. You now can perform broad and unlimited actions on the system!
With Defendpoint, you can target specific COM elevation CLSID's and assign privileges to the task without granting full admin rights to the user. COM based UAC messages can also be targeted and replaced with custom messaging, where COM classes can be allow listed and/or audited. This unique capability is reinforced by a number of international granted patents.
As an additional security measure Defendpoint will force the File Open and Save dialogs to run with the user’s standard rights, which prevents the user from tampering with protected system files or running programs with elevated privileges.
The most important step for most organisations is to remove administrator rights for standard users. Although developments in the Windows operating system have made it possible for users to run with minimal rights, the lack of granular control, introduces its own set of security challenges.
[1] SALTZER, J.H. AND SCHROEDER, M.D., ‘The Protection of information in computer systems,’ Proceedings of the IEEE, vol. 63, no. 9 (Sept 1975), pp. 1278-1308.








