I think we have all been there before. We pilot a solution, run the gambit of tests in the lab, and when it comes to production, the scalability falls flat on its face. It does not matter if the solution was architected correctly for the environment with multiple nodes, high performance database, and tons of CPU and RAM to spare, it just does not work. This is when we realize the vendor failed to create the technology with the scalability needed to address the challenges often encountered in enterprise deployments. The outcome is that we end up living with a scaled back implementation, or worse, waste time and money before picking another vendor. This is a challenge BeyondTrust is acutely aware of. Why? Because many of our clients have been there with a different vulnerability management solution and discovered that Retina was designed from the ground up to be scalable, portable, and architecturally flexible to meet the heavy demands of a true enterprise environment. For example, take the screen shot below:
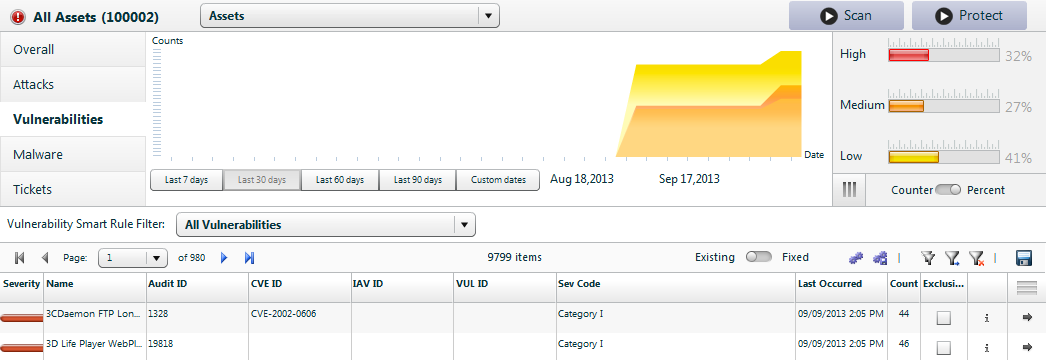
This is from one of our test lab environments used for client demos. It is sanitized client data that has been scaled for testing. The supporting database contains over 100,000 assets and is fully functional for searching, filtering, reporting, and role-based access. It is used to demonstrate that with a single pane of glass, an organization can truly realize that they can perform vulnerability management for every asset in their organization, not just servers or PCI environments.
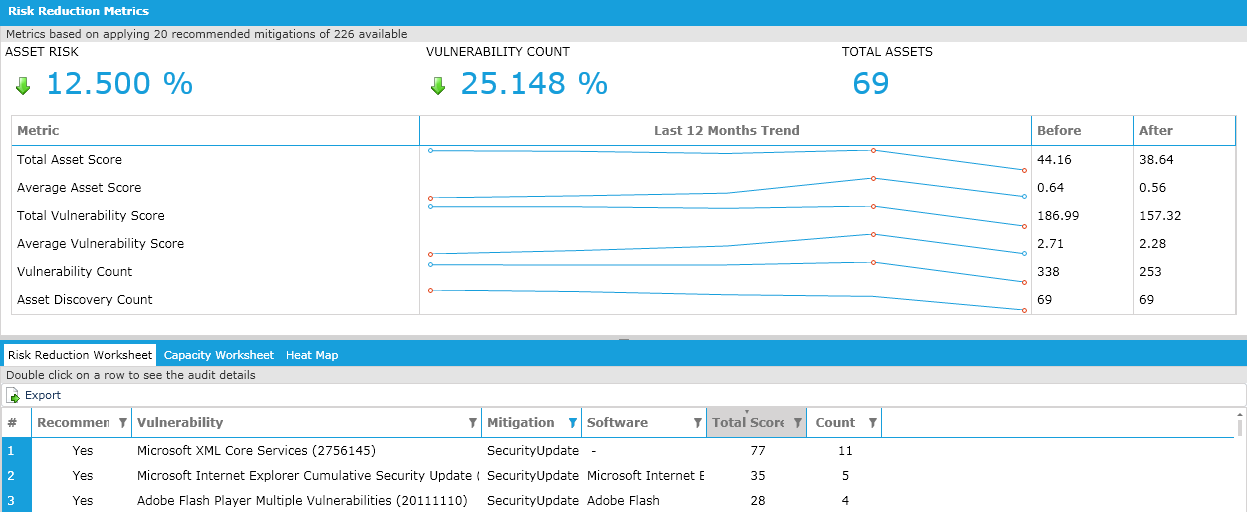
Consider the following report that literally takes a few seconds to generate using our embedded data warehouse (Retina Insight) that ships with the solution. It helps take that list of 100,000 devices and prioritize which devices should be remediated first, in lieu of a phone book of potentially a few million pages for every asset and vulnerability. Believe it or not, some our leading competitors still can only generate the long laundry list vulnerability report and do nothing to help the enterprise prioritize remediation activities.
We have all been there before. We have all had tools that work great on our desktops, in labs, but can not handle what truly awaits in the enterprise. With over 260 reports available out of the box, a true ad-hoc report engine that can build customized reports based on all the data collected, and a scalable platform that can handle hundreds of thousands of assets, why have you not looked at Retina yet? Get more info.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








