
The world today is very much different than 10 years ago. High profile breaches and strict compliance mandates have made privileged password management solutions a common place in the workplace, as well as personal life. Whether you are a large corporation with a need to isolate and lock down your PCI environment, or a user with a basic requirement to store a complex password for your credit card account, there is a tool for every job.
But is this enough for your? Rotating credentials with secure storage is one thing, but what happens when a legitimate user turns to the dark side? With great power comes great responsibility.
I’ll give you an analogy. Let’s say you run a jewelry store, and you have a safe containing your most valuable items. I would imagine you would, at minimum, only let certain users access the safe, and you would ensure that the access combination gets rotated regularly. An item goes missing from the safe. The employees with access to the combination swear blind they had nothing to do with it. First thing you do is review the security footage of your cameras. Now, whether you identify it was an employee that took the item or see that another unauthorized individual had taken the opportunity to slip something out while the safe was unlocked, you had an indelible recording of the event to fall back on.
Things are not so different with privileged access management. You need to rotate your privileged passwords, and provide access control to make sure that the right people have access to them but what happens when users dispute misappropriation of data – what do you fall back on?
Session Management is not a nice to have add-on to password management, it’s a MUST HAVE FEATURE.
What irks me is that with a capability so critical to security, why do so many vendors charge separately for the feature? Why would you ever want to implement password management without session management? It would be like buying a car without a steering wheel. Password management and session management go together like salt and pepper, mac and cheese, peanut butter and jelly, and Beavis and Butt-head.
BeyondTrust has never sold session management separate from privilege management – it's included with PowerBroker Password Safe. We prefer customers to have all the tools available for privileged access management, not half a solution. Here is what you get with the PowerBroker Password Safe solution:
- Auto-login without revealing the credentials
- Gateway proxy for unmanaged credentials
- Video recording
- Live session monitoring
- Live session searching
- Indexed search across recorded sessions
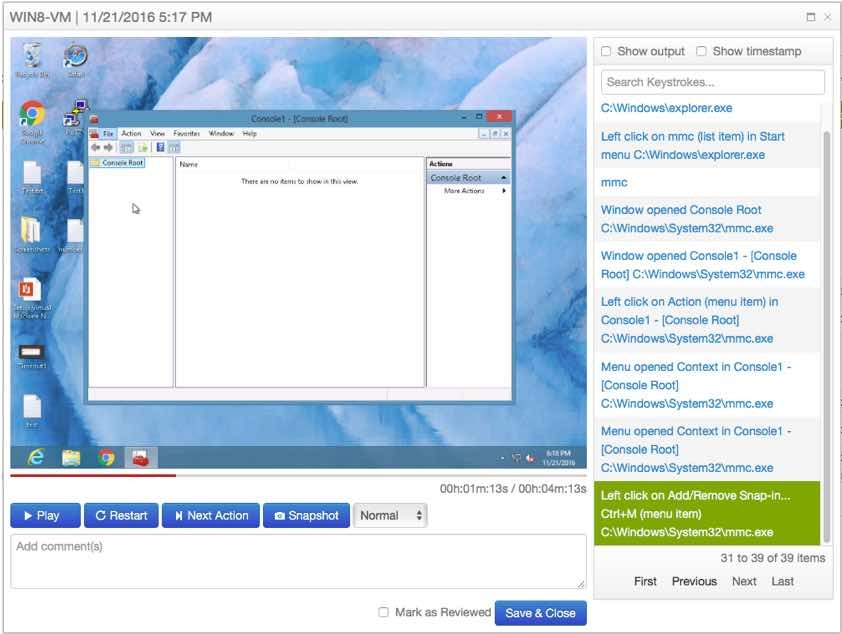
- Session replay with playback controls, and snapshot export
- Session replay audit and annotation
- Session locking
- Session termination
- Keystroke recording and indexing
- SSH output recording and indexing
- RDP paste buffer recording and indexing
- RDP click event recording and indexing
Even if you are not interested in recording administrator activity, you should at minimum ensure that you leverage auto-login so that the privileged credentials are never exposed to the user.
PowerBroker Password Safe provides secure session management, with the ability to proxy access to RDP, SSH and Windows/Unix/Linux Applications. Dynamic assignment of just-in-time privileges via Adaptive Workflow Control, allow organizations to lock down access to resources based upon the day, date, time, and location. By limiting the scope to specific runtime parameters, it narrows down the window of opportunity where someone might be exploiting misappropriated credentials. For example, if you normally expect the administrator (or third-party vendor) to be logging on from particular systems, you can ensure that access is only permitted from predefined allowable address ranges. Similarly, you can set up policies to control when the accounts are accessible, and alert when specific access policies are invoked.
On top of its granular access controls, PowerBroker Password Safe ensures managed accounts have their passwords regularly rotated – every time a password is released, it can be a one-time password for security. Passwords can be regularly changed using strong and complex policies to ensure that any credential breach, whether directly by the user or indirectly via malware, has a limited window of exploitation. Several additional capabilities in the product help to mitigate the risks of administrative/third-party access:
- Adaptive workflow control can route workflow to different groups according to runtime parameters.
- Password Safe’s application proxy can automatically log users onto resources using managed credentials with zero exposure. Passwords may also be securely passed to any Windows, Unix, or Linux application.
- All user activity may be recorded for later playback, and as mentioned above, real-time monitoring capabilities allow sessions to be monitored with options to remotely terminate or pause (lock) active sessions.
To learn more about how you can improve your organization’s security through PAM, check out SANS Instructor, Dave Shackleford's, on-demand webinar “Privilege (and Password) Management Without the Pain”. And more information on our privileged password and session management solution, feel free to contact us.

Martin Cannard,
Martin has been helping organizations solve challenges in the privileged account management and identity and access management space for over 24 years. At Dell Software, Martin managed a team of Solution Architects, focused on designing and implementing solutions in the Privileged Account Management (PAM) space. Prior to joining Dell, Martin was Sr. Product Manager for Novell Privileged User Manager, a privilege management application acquired from Fortefi, an organization where he served as Vice President, Corporate Development. Prior to this, he was Program Manager of Client Technologies at Symantec where he was responsible for many ground-breaking field and channel enablement applications. Additionally, Martin managed the European QA group at Axent Technologies and has held various management positions in consulting, systems development, and operations. Martin is a regular speaker for security events, and webinars.








