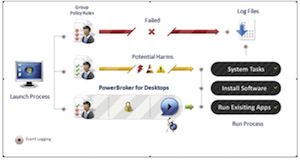
 An effective least privilege solution implemented for desktops will transparently plug into Active Directory and Group Policy in order to manage the elevation of privileges based on role and policy. This is what is called least privilege because you get the minimum amount of privilege in order to do a specific task only when it is needed. If the user has no privilege, then every attempt to do these tasks will be met with a UAC prompt asking for more privilege; if the user already has admin rights, then they are at risk for inten- tional, accidental, or indirect damage to their data.
Without least privilge a desktop user has either too much privilege (being setup as the default admin) or too little privilege (being set as standard user). If they have too much privilege then they can misuse that intentionally, accidentally or indirectly. If they have too little then help desk costs will rocket up while productivity falls quickly.
An effective least privilege solution implemented for desktops will transparently plug into Active Directory and Group Policy in order to manage the elevation of privileges based on role and policy. This is what is called least privilege because you get the minimum amount of privilege in order to do a specific task only when it is needed. If the user has no privilege, then every attempt to do these tasks will be met with a UAC prompt asking for more privilege; if the user already has admin rights, then they are at risk for inten- tional, accidental, or indirect damage to their data.
Without least privilge a desktop user has either too much privilege (being setup as the default admin) or too little privilege (being set as standard user). If they have too much privilege then they can misuse that intentionally, accidentally or indirectly. If they have too little then help desk costs will rocket up while productivity falls quickly.

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








