I speak to many IT professionals who don’t have visibility over the endpoints and don’t really understand the day to day work behaviors of their staff. When asked to “secure the endpoint” by their management, there are many misconceptions about the effectiveness which naturally arise.
In a survey of 500+ IT and IT security professionals by Ponemon, a hierarchy of perceived effectiveness was revealed. The table below highlights the tools and technologies IT Professionals ranked in order of importance, which is completely contradicted by the analysis and recommendations of experts such as the Cyber Security Council in association with SANS, GCHQ, CESG, NIST, ADoD. All of which focus on the reduction of the attack surface, as a priority.
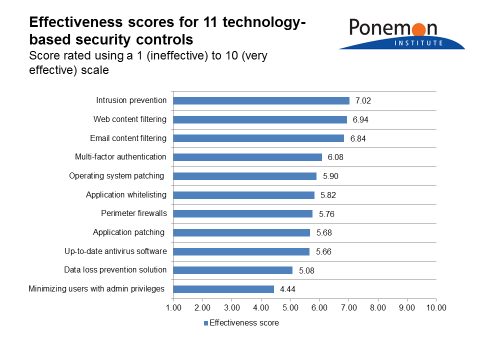
Looking at the above table the top 3 technologies are essentially reactive “block listing” technologies based on detection. Reactive technologies simply do not work but are often implemented because they are understood and perceived to be easier to roll out.
55% of IT professionals do not have visibility over their endpoints and as a result, try to avoid implementing technology that touches the end user. However, this puts them at extreme risk.
Navigating the polarised opposites of security and freedom is not easy; this is further compounded when IT departments are under pressure to bring new systems to market that will provide their organisations with a competitive edge.
So many times, I have seen security become an afterthought, rather than being an integral part of a design from the outset. Good security design is not always visible and thus not well understood by the c-suite, who pile on the pressure to release systems or improve user freedom.
Poorly implemented security will come to the forefront when, not if, a breach occurs. The pressure applied to release a system will quickly be forgotten about! To make matters worse, many IT professionals have a limited understanding of security. This lack of understanding often comes from security not being “sexy”, or worse, an unwanted headache.
There is a risk that endpoint security may reduce your ability to respond to ever-changing business needs. When Least Privilege Security inhibits flexibility or the speed at which IT can respond, it will result in a failed project. So, where security is not an absolute necessity, it is regularly omitted for an easy life.
Securing IT systems to provide business continuity must be balanced with the ability to innovate. Organisations that move slowly will lose out to the competition, as IT systems play a key role in an organisation’s agility. However, this is not an excuse for poor security design.
For more information on the recommendations from the industry bodies mentioned above, please take a look at my book The Endpoint Security Paradox available on amazon <click here>








