I normally don't write blogs reviewing books or even new products (unless it is for BeyondTrust of course). Occasionally, I will blog on the latest breach, like Under Armour, but we have become so numb to these events, there is really nothing new to write. Under Armour lost email addresses, names and hashed passwords for 150 million people. The mitigation is the same as it is for other similar breaches:
- Have a unique password for every application, and
- If you reused the password with Under Armor’s fitness application, please go and change it every place else.
Simple fixes, right? You would think so. Today, however, is an exception and requires a special place in my dark heart for cybersecurity. I need to do a simple book review, and it does relate to Under Armour. The book is called the “Internet Password Journal,” by Mia Charro, and represents everything that is wrong with cybersecurity today.
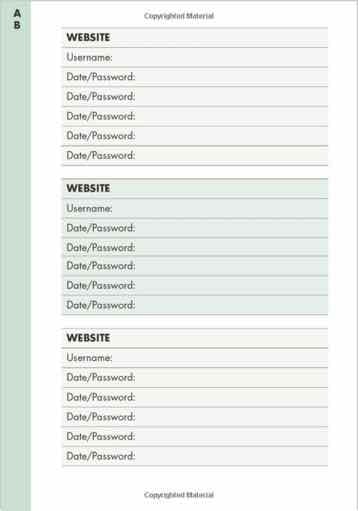
The diary style book is available on Amazon for $9.99 and is organized like a traditional phone book with tabs for all the letters of the alphabet (see the screenshot above). The introduction does have a few relatively good pages on password security and recommendations, but the rest of the book is exactly the same on every page. The concept is to list the website or application, and the current password, all in one location.
Do NOT Write Your Passwords Down in One Location
While this book is definitely consumer-based, the security around writing them down in one insecure journal is clearly wrong. If this book is used for business, it is even a grosser violation of cybersecurity best practices – even for break glass scenarios. You are listing every password in one place, with no additional security, and physical access to the book (even if it is a physical safe or strongbox) reveals every other password for every site documented. There is no benefit outside of a place to “remember” unique passwords. In this day and age with free password managers and password management being built into the operating system (Apple iCloud Keychain for example), this book represents a step backward in cybersecurity and how to manage credentials. I am stunned it even exists.
Under Armour and Password Re-use
So how does this relate to Under Amour? The password re-use concept. While the book goes backward in implementation, it does enable a user to list every application and its current password – hopefully all different. The goal is to keep them all unique even though the documentation process is flawed. If you re-used the same password with Under Armour’s fitness application and any place else, you are now vulnerable to exploitation. Documenting the same password in a book like this is a moot point. You could have used a single Post-It note to document the re-used password every place you used it. And, I would still never recommend that.
Best Practices for Managing Passwords
For businesses and consumers, please follow these recommendations based on lessons learned from Under Armour and this book:
- Never physically write down all your passwords in place. If they need to be documented for break glass scenarios, keep each one in a separate sealed envelope so all of them are not exposed if one is accessed. Anytime they are physically written down, they should be secured in a safe or lockbox as well.
- Do not re-use passwords anywhere. They all should be unique – every time.
- If you do use a book like this, please do not use it at work. It is truly a consumer product and should be secured like precious jewelry. Someone with physical access could own you (even with unique passwords because they would know every single one), which is far worse than common identity theft.
Finally, to be fair, there is one use case I can think of for a book like this, and it would have value. If a consumer used it as a part of the last will and testament and kept it up to date (a little morbid in my opinion), then this book may make sense. For everyone else, it should be avoided, and the concepts of password re-use and the ramifications of the latest public breach should be heeded.
If you are looking to secure passwords in your environment, BeyondTrust can help. Password Safe can securely store your privileged credentials and ensure security best practices are followed for storage and retrieval forgoing the need to ever write them down. For a cybersecurity strategy session, contact us today.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








