 On January 12, 2016 Microsoft will end of life Internet Explorer (IE) 8, 9 and 10, and that has the media in a bit of frenzy, with the news even trending on social networks like Facebook. What’s got everyone buzzing about? After Tuesday, only Microsoft IE 11 and Edge will continue to receive updates and security patches leaving millions of people at risk from new cyber threats, unless they upgrade their browsers or operating systems.
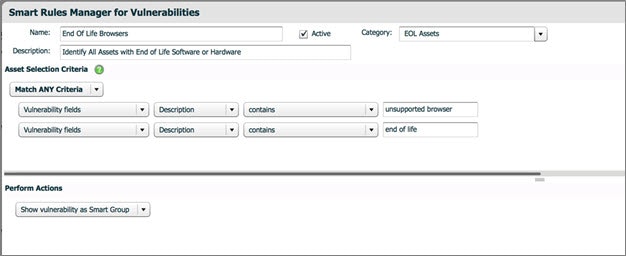
This problem is not only confined to personal computers, but also affects many businesses who depend on older browsers due to custom plugins and legacy applications, that don’t render in modern browsers. Consequently, identifying which assets have older versions installed and upgrading them is critical for maintaining security and compliance. Alternatively, this risk can be mitigated by switching to another browser altogether. If you decide to switch, make sure you disable the end of life'd versions of IE since malware and exploits may still target them and initiate a compromise.
In traditional Microsoft fashion, the end of life announcement is not black or white. There are exceptions to the end of life notice that every business should be aware of:
On January 12, 2016 Microsoft will end of life Internet Explorer (IE) 8, 9 and 10, and that has the media in a bit of frenzy, with the news even trending on social networks like Facebook. What’s got everyone buzzing about? After Tuesday, only Microsoft IE 11 and Edge will continue to receive updates and security patches leaving millions of people at risk from new cyber threats, unless they upgrade their browsers or operating systems.
This problem is not only confined to personal computers, but also affects many businesses who depend on older browsers due to custom plugins and legacy applications, that don’t render in modern browsers. Consequently, identifying which assets have older versions installed and upgrading them is critical for maintaining security and compliance. Alternatively, this risk can be mitigated by switching to another browser altogether. If you decide to switch, make sure you disable the end of life'd versions of IE since malware and exploits may still target them and initiate a compromise.
In traditional Microsoft fashion, the end of life announcement is not black or white. There are exceptions to the end of life notice that every business should be aware of:
- Windows Vista and Windows Server 2008 will still receive updates for Internet Explorer 9, as that is the most current supported version on those operating systems.
- Windows Server 2012 will still receive updates for Internet Explorer 10, as that is the most current supported version on that operating system.
- Windows 8 is no longer supported, so customers must update to Windows 8.1 in order to receive Internet Explorer 11.
- 56423 - Windows 8 End-of-Support
- 56424 - Microsoft Internet Explorer End-of-Support - Vista/2008
- 56425 - Microsoft Internet Explorer End-of-Support - 7/8.1/2008R2/2012R2
- 56426 - Microsoft Internet Explorer End-of-Support – 2012
 Retina CS and Retina Network Security Scanner vulnerability management solutions deliver unmatached reporting, scalability and coverage. For more information on any of our cyber security solutions, contact us today.
Retina CS and Retina Network Security Scanner vulnerability management solutions deliver unmatached reporting, scalability and coverage. For more information on any of our cyber security solutions, contact us today.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








