In recent days, Saudi Arabia has warned organizations in the kingdom to be on the alert for the Shamoon computer virus, a variant of which gained notoriety after being linked to attacks against Saudi Aramco in 2012 and reportedly damaged over 30,000 systems.
Shamoon is an attack campaign delivering an aggressive malware strain known as Disttrack which destroys target systems by wiping data rendering them unable to boot.
In late 2016 Shamoon 2 appeared and has been increasingly active in targeting organizations in the Middle East. Several Government ministries and chemical companies have been attacked. With many believing this is just the start of a renewed campaign many are wondering what can be done to prevent this latest threat.
So how does it work?
As with most advanced threats, the Shamoon campaign is modular and composed of three main components.
Shamoon Dropper – This is the initial point of infection and used by the attackers to establish a foothold.
Shamoon Wiper – This inflicts the damage by installing a malicious disk driver to overwrite data.
Shamoon Reporter - This reports back to the attacker the domain of the target machine and the number of files that have been overwritten.
This modular approach allows the attacker to reduce the risk of being detected, as not all the malicious code is delivered at once and droppers can be quickly evolved to evade AV and other detection technologies.
Although there are few available details of how exactly the attack is delivered, phishing emails or stolen credentials are the most likely source.
Once the attack begins, the malware rapidly embeds itself into the target system and uses several tricks to appear legitimate and maintain persistence. In the observed attacks, we see that exploiting admin rights and the ability of unknown payloads to execute is key to the success of the campaign.
The files dropped to disk are not commonly detected by AV solutions and use filenames that appear legitimate to avoid arousing suspicion.
How can it be stopped?
Defendpoint takes proven best security practices and combines them to offer multiple layers of proactive prevention on the endpoint. This allows organizations to stay secure and prevent attacks such as Shamoon and Disttrack.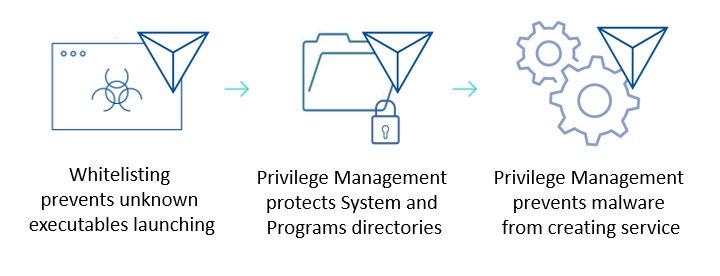
As shown on this revised attack chain, Defendpoint’s layers of proactive prevention offer multiple ways to mitigate the risk of the attack. As with many advanced modular attacks, there are a number of points at which Defendpoint can break the attack chain and prevent the attack.
Looking beyond Shamoon
Many organizations are concerned about not only the current Shamoon campaign but what the next attack will be. With an ever-increasing number of attacks, the traditional approaches of relying on detection technologies simply can’t stay ahead of the threats as the attacks continually evolve.
With Defendpoint, organizations can stay ahead by significantly reducing the attack surface of their endpoints using proactive measures to stop even the most advanced cyber attacks. This technology is simple to deploy and simple to manage, offering protection from day one.
For more detail and analysis on the Shamoon virus as well as how it can be mitigated download our article.

James Maude, Field Chief Technology Officer
James Maude is the Field Chief Technology Officer (FCTO) at BeyondTrust. With his broad experience in security research, both in academia and industry, James has spent the past decade analyzing cyber threats to identify attack vectors and trends in the evolving security landscape. He is an active member of the security community and hosts Adventures of Alice and Bob, a podcast that shines a light on the people making a difference in security. As an expert voice on cybersecurity, he regularly presents at international events and hosts webinars to discuss threats and defense strategies.








