In InfoSec these past few weeks it has been impossible to miss the news that the secretive spyware company known as Hacking Team has been breached and their files posted online. This compromise has resulted in 400GB of confidential data being released online and caused widespread embarrassment for the company and clients alike.
Included in the massive data dump were several 0 day vulnerabilities including a previously unknown exploit for Adobe Flash media player - CVE-2015-5119. This exploit allowed attackers to execute code on a victim's machine just by getting them to browse to an infected website. The Hacking Team boasted in their documentation that this was exploiting "the most beautiful Flash bug for the last 4 years".
The publically disclosed proof of concept exploit in Adobe Flash lets the attacker execute code as the logged on user on the targeted system - in this case launching calc.exe to prove that the system has been compromised. In a malicious attack this could be used to launch malicious commands or download and execute further malware payloads.
Here at Avecto we're happy to show how effectively Defendpoint's proactive security stands up to these advanced attacks and 0 days. We took this publically available exploit code and tested it against Defendpoint with our standard corporate policy without any updates or changes.
So what happened? Defendpoint blocked the attack proactively without any need for signatures, updates or threat intel. The malicious website was automatically isolated in the Sandbox along with the vulnerable version of Flash preventing any access to the user's data.
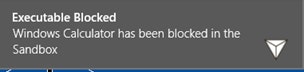
When Adobe Flash was exploited not only was it isolated from the users profile but attempts to execute were blocked by Defendpoint's unique context aware Application Control which can distinguish between user interactions and content executing in the Sandbox.
The policy is configured to pop up a simple message to warn users and record an event in the log for security teams to review.

To extend the exercise further and show how our layers of protection work we decided to allow the exploit to fully run and so disabled our advanced application control. This resulted in the exploit launching its chosen payload in our isolated Sandbox environment. This meant that even if allowed to run, the exploit could still not access the user's data or persist on the system.
So there you have it, proactive defences against zero day threats that stands up to real world attacks.

James Maude, Field Chief Technology Officer
James Maude is the Field Chief Technology Officer (FCTO) at BeyondTrust. With his broad experience in security research, both in academia and industry, James has spent the past decade analyzing cyber threats to identify attack vectors and trends in the evolving security landscape. He is an active member of the security community and hosts Adventures of Alice and Bob, a podcast that shines a light on the people making a difference in security. As an expert voice on cybersecurity, he regularly presents at international events and hosts webinars to discuss threats and defense strategies.








