If your vulnerability assessment scans can’t produce meaningful and actionable reports, performing a scan does no good for anyone. If you’ve read my other blog posts, you know I have no qualms about stating that BeyondTrust provides the best vulnerability reporting in the industry. Ask your favorite analyst and they’ll tend to agree.
Of course, we understand that many organizations need to run multiple scanners in their environments. Fortunately, the BeyondInsight IT Risk Management Platform makes it easy to understand and act on vulnerability data from several scanners. For instance, with BeyondInsight v5.1, we just made it much easier to get comprehensive reports from your existing QualysGuard scans and data.
 BeyondInsight solves several shortcomings in competing reporting systems and allows organizations to meet their business requirements by providing prioritized, contextual vulnerability and risk data. Consider some of the common problems we hear from customers regarding QualysGuard:
BeyondInsight solves several shortcomings in competing reporting systems and allows organizations to meet their business requirements by providing prioritized, contextual vulnerability and risk data. Consider some of the common problems we hear from customers regarding QualysGuard:
- The highest cost per asset in the industry based on list pricing
- All data is present in the cloud only and must be downloaded to spreadsheets or other tools for manipulation
- Limited reporting capabilities and data longevity restrict long-term reporting needs and flexibility in output
- Network scanning technology only with no support for local agents or advanced connectors into technologies like VMware
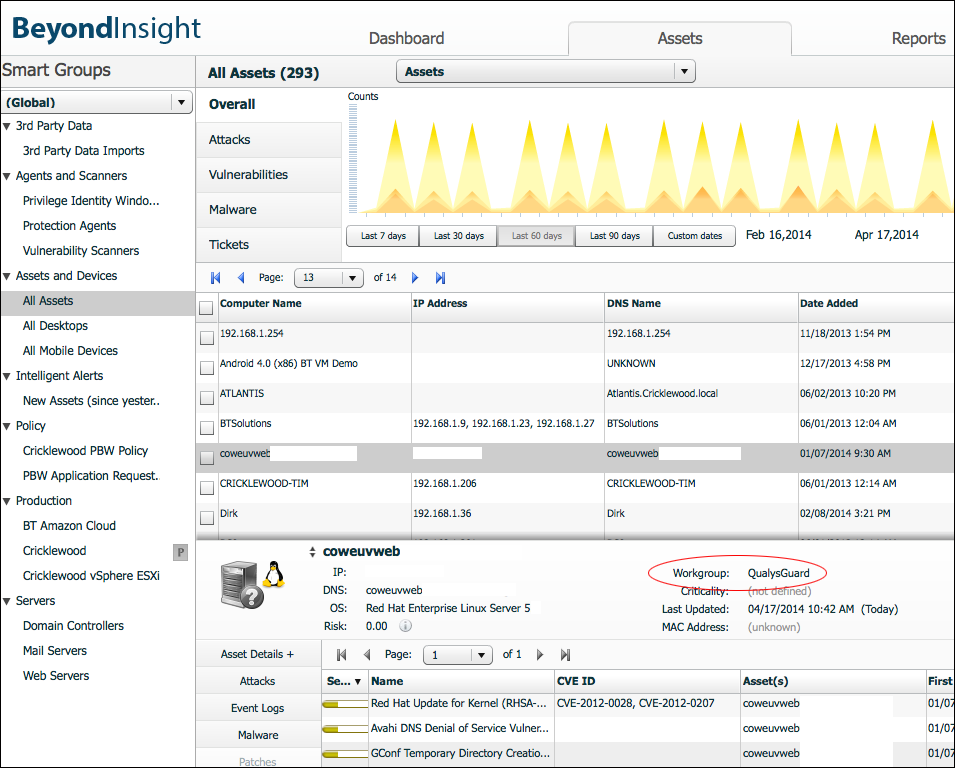
To assist our customers who are also Qualys clients, BeyondInsight v5.1 includes a new QualysGuard Cloud Connector to help bridge reporting shortfalls. BeyondInsight can now seamlessly import QualysGuard vulnerability data on an automated basis, in addition to allowing manual imports of flat files from Qualys, Tenable and Rapid7.
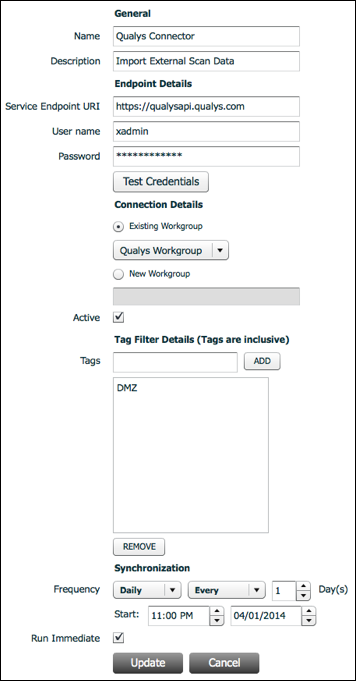
BeyondInsight’s reporting and analytics engine can present QualysGuard data alongside, or independently of, data from BeyondTrust's own Retina CS Enterprise Vulnerability Management capabilities, which operate within the BeyondInsight platform. Configuring the Qualys connector is easy and only requires a few pieces of subscription information.
Once configured, the Connector will import QualysGuard results and create assets, reports, threat analyzers, heat maps, and data consistent with the native scan results from Retina CS – including being able to set exclusions. Customers also benefit from much more data and additional differentiators when using BeyondTrust’s Retina CS vulnerability management engine. These include (but are not limited to):
- Enumeration of users, shares, services, processes, ports and installed software
- Assessment capabilities for ThinApps and other VMware technologies
- Extensive cloud connectors for Amazon, GoGrid, RackSpace, IBM and VMware
- Mobile device scanning for BlackBerry, ActiveSync and Android
- Extensive third-party integration with SEIMs, GRC solutions, Help Desk solutions, and other security tools
- Benchmark configuration compliance using STIG, Microsoft and CIS templates
- Malware and exploit toolkit information
BeyondTrust provides unmatched, context-aware visibility into the risks facing the largest, most diverse IT environments. Part of this means working well our customers’ other security solutions, even when those solutions compete with our own. Through features such as the QualysGuard Cloud Connector, BeyondInsight can help customers get more value out their scan data through superior reporting and analytics.
For BeyondTrust customers seeking to consolidate and save costs by replacing their external scanning solutions, we offer the BeyondSaaS cloud-based scanning service for assessing externally facing network and web infrastructure. The BeyondInsight platform consolidates reporting and analytics for BeyondSaaS, Retina CS (for internal vulnerability management), and – now – third-party scanning solutions such as QualysGuard. As a result, customers have a single, centralized interface through which to view, analyze and report on their vulnerability management initiatives.
> Learn more about BeyondInsight
> Request a free trial of BeyondSaaS for perimeter scanning

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








