
I cannot begin to tell you how much spam regarding GDPR I received before May 25th – everything from sales emails to privacy statements flooded my inbox. I am over it, and I bet you are too. Outside of BeyondTrust being compliant, I have been asked by customers, managed services providers, and media what features BeyondTrust products have become GDPR compliant. I’ll answer that question here.
First, take a look at this blog: "The EU General Data Protection Regulation (GDPR) – 5 Ways to Compliance". It helps form the basis of how BeyondTrust solutions can shield sensitive data using privileged access management. The goal is to restrict personal information to a need-to-know basis and purge information when it is no longer needed. This is perfectly reasonable and in line with regulations. The second part to determine BeyondTrust solutions’ applicability to GDPR is identifying which features in BeyondTrust solutions can obfuscate (or stop) the collection of personally identifiable information during least privilege or vulnerability management so there is no risk. To that end, please consider the following settings in Retina CS and PowerBroker for Windows.
Retina CS Enterprise Vulnerability Management for GDPR Compliance
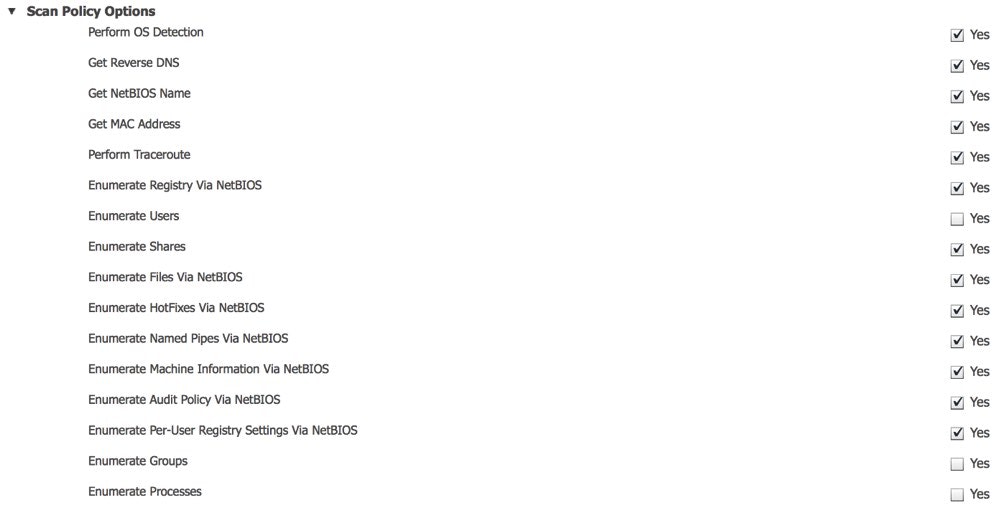
By default, during an all audits scan, and during a detailed discovery scan, Retina automatically discovers all users, user group information and identifies rogue accounts for automatic onboarding into PowerBroker Password Safe. While this information is essential for automation, depending on how it is reported, exported, or managed, it could be in violation of GDPR regulations. This is not true for every organization and is use case and implementation-based. For example, if you send a user report via email to HR or it leaves the country, you may have to consider the GDPR ramifications. Therefore, if you do not need to discover, store, and report user information, just turn it off.
Within BeyondInsight, Edit Scan Settings in the appropriate report template used for an assessment and just uncheck Enumerate Users, Enumerate Groups, and Enumerate Privileges. All three should be disabled to prevent collection. This will leave no question in anyone’s mind that usernames and login information are not being collected. Of course, if your workflow has no violations, this is still a great method for automation and to look for indicators of compromise. See the screenshot below.
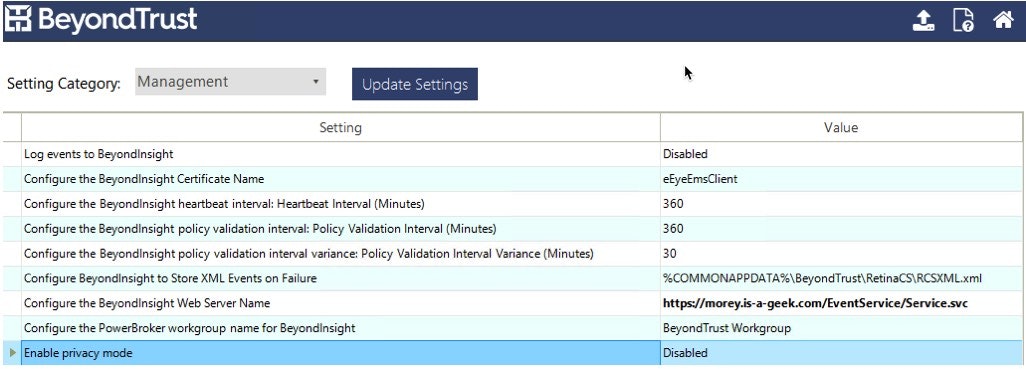
PowerBroker for Windows Privilege Management for GDPR Compliance
PowerBroker for Windows has a data privacy feature that allows BeyondInsight to continue to collect detailed information about application launches and rule matching per user but obfuscates the username in order to meet compliance mandates. In privacy mode, reported usernames are replaced by unique hashes. The same username on a different host will have the same hash so statistics and usage patterns can be reported accurately but encrypted. BeyondInsight does not have a method to determine who the username is since it is hashed at the agent and transmitted with no linkage to the source. This ensures user privacy is never compromised or decoded and threat detection and privilege reporting can still occur on a normal basis. To turn this setting on, enter the setting menu for the policy and change Privacy Mode to Enable. See the screenshot below.
 GDPR does not need to be a scary monster. For more on how BeyondTrust can help report on your GDPR compliance, check out this white paper or contact us today.
GDPR does not need to be a scary monster. For more on how BeyondTrust can help report on your GDPR compliance, check out this white paper or contact us today.

Morey J. Haber, Chief Security Advisor
Morey J. Haber is the Chief Security Advisor at BeyondTrust. As the Chief Security Advisor, Morey is the lead identity and technical evangelist at BeyondTrust. He has more than 25 years of IT industry experience and has authored four books: Privileged Attack Vectors, Asset Attack Vectors, Identity Attack Vectors, and Cloud Attack Vectors. Morey has previously served as BeyondTrust’s Chief Security Officer, Chief Technology, and Vice President of Product Management during his nearly 12-year tenure. In 2020, Morey was elected to the Identity Defined Security Alliance (IDSA) Executive Advisory Board, assisting the corporate community with identity security best practices. He originally joined BeyondTrust in 2012 as a part of the acquisition of eEye Digital Security, where he served as a Product Owner and Solutions Engineer, since 2004. Prior to eEye, he was Beta Development Manager for Computer Associates, Inc. He began his career as Reliability and Maintainability Engineer for a government contractor building flight and training simulators. Morey earned a Bachelor of Science degree in Electrical Engineering from the State University of New York at Stony Brook.








