Keyboard navigation enabled.
TAB or Shift+TAB to navigate across. Down ↓ to open menu. ESC to close menu.
Down ↓ to select section. Right → to activate. Up ↑ / Down ↓ / Tab to traverse all. ESC to exit.
Watch Product Demos
Access our demo library to view BeyondTrust products in action.
Learn More Learn MoreBuyer's Guide for Complete PAM
Complete your PAM journey with detailed guidance, hands-on capability checklists, and more.
Learn More Learn MoreGartner® Magic Quadrant™ for PAM
Learn why Gartner® has named BeyondTrust as a PAM Leader once again.
Learn More Learn MoreSee what customer success looks like
Explore how customers are using our solutions to advance security and productivity.
Learn More Learn MoreFind a Partner
Offering a wide array of services and benefits tailored to your specific needs
Learn More Learn MoreLeader in Privilege-Centric Identity Security
Learn how BeyondTrust solutions protect companies from cyber threats.
Learn More Learn MoreWhat can we help you find today?
Watch Product Demos
Access our demo library to view BeyondTrust products in action.
Learn More Learn More








 The U.S. federal government last week moved to ban the use of a Russian brand of security software, Kaspersky Lab products, by federal agencies amid concerns the company has possible links to Russian state-sponsored cyberespionage activities.
For organizations concerned about how this ban will affect their IT operations, BeyondTrust can assist U.S. federal government agencies in discovering known and unknown assets (i.e. shadow IT) with Kaspersky Lab products installed on them. In four simple steps using
The U.S. federal government last week moved to ban the use of a Russian brand of security software, Kaspersky Lab products, by federal agencies amid concerns the company has possible links to Russian state-sponsored cyberespionage activities.
For organizations concerned about how this ban will affect their IT operations, BeyondTrust can assist U.S. federal government agencies in discovering known and unknown assets (i.e. shadow IT) with Kaspersky Lab products installed on them. In four simple steps using 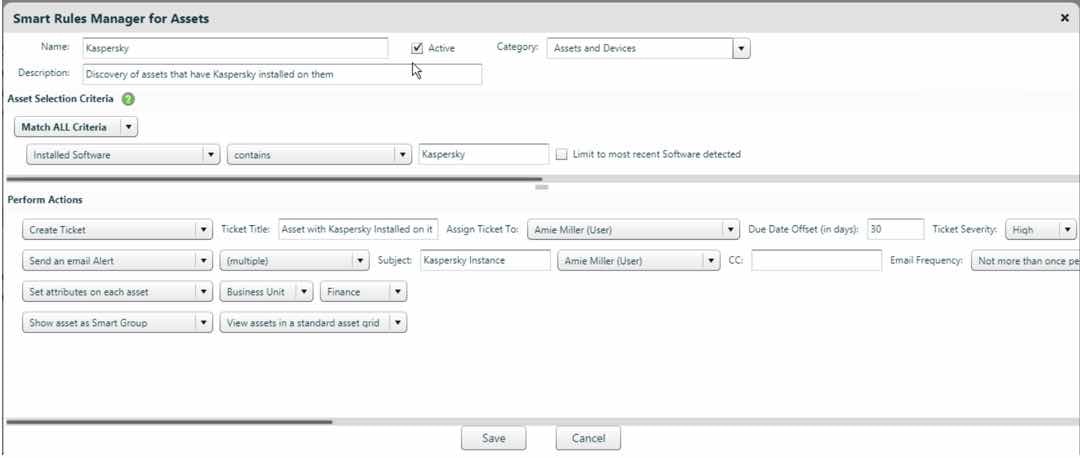 3) Once the smart rule is created you can run a Software Report scan against it to discover all the assets with Kaspersky Lab products on them within your environment, or run a Software Report scan on various IP address groups within your environment. Any asset discovered within your environment will be automatically assigned to the smart group and have the action performed on it as outlined within the smart rule.
Note – BeyondTrust common practice is to run a scan with privileged credentials for best results.
4) Once ALL (known/unknown) of the assets with Kaspersky Labs are discovered within your environment, BeyondTrust – by means of its robust reporting functionality, Analytics and Reporting – will allow you to systematically track progress by using one of its 270+ reports such as the report titled Asset Software Delta Trend. You will be able to display the changes (added, removed and current) in the software installed on the selected assets.
For a representation of this capability, please see the screenshot below.
3) Once the smart rule is created you can run a Software Report scan against it to discover all the assets with Kaspersky Lab products on them within your environment, or run a Software Report scan on various IP address groups within your environment. Any asset discovered within your environment will be automatically assigned to the smart group and have the action performed on it as outlined within the smart rule.
Note – BeyondTrust common practice is to run a scan with privileged credentials for best results.
4) Once ALL (known/unknown) of the assets with Kaspersky Labs are discovered within your environment, BeyondTrust – by means of its robust reporting functionality, Analytics and Reporting – will allow you to systematically track progress by using one of its 270+ reports such as the report titled Asset Software Delta Trend. You will be able to display the changes (added, removed and current) in the software installed on the selected assets.
For a representation of this capability, please see the screenshot below.
 Next Steps
If your organization must be compliant with the mandate to remove Kaspersky Lab products, or would like to see a demonstration on the critical discovery and automation capabilities of Retina CS Enterprise Vulnerability Management,
Next Steps
If your organization must be compliant with the mandate to remove Kaspersky Lab products, or would like to see a demonstration on the critical discovery and automation capabilities of Retina CS Enterprise Vulnerability Management,