If you are reading this post, it’s likely that you already know Intel Security has announced the end of life (EOL) for McAfee Vulnerability Manager (MVM). And with that, Intel will no longer provide support or software updates, including critical vulnerability checks for new and emerging threats – leaving organizations (possibly yours) exposed and at risk of a breach. MVM customers now have to find a new vulnerability management solution, but from who? The clock is ticking, your attack surface is growing, and your adversaries are lurking in the shadows. What will you do?
You could go with the vendor that Intel suggests, but then again, you’ve already been burned by them, once. It’s time for a real change, and not just switching brands. What you want is a cyber security partner, not just a vendor. And isn’t it about time you get more from your vulnerability management solution than simply reams of data?
Welcome to BeyondTrust, where more than just our logo has changed. With Retina CS Enterprise Vulnerability Management, current McAfee Vulnerability Management customers can safely and easily export their existing vulnerability data directly to Retina CS. Once there, you have the ability to centralize all your scan data for prioritization, clearly communicate risk throughout the organization and discover unknown dangers with advanced threat analytics.
We believe that security professionals deserve more from their vulnerability management solution. That’s why we deliver vulnerability data in the proper context. Our award-winning Retina CS architecture empowers organizations to
- See data differently with over 270 customizable security, audit and compliance reports.
- Accelerate the patch process through automated remediation of Microsoft, JAVA, Adobe vulnerabilities, and more.
- Find soft target threats with exploit correlation against Metasploit, Exploit-Database, Canvas and Core Impact.
- Expose hidden malware by checking active processes against over 50 Antivirus solutions.
- Make better decisions with data from other scanners and PowerBroker Privilege Management.
- And much more…
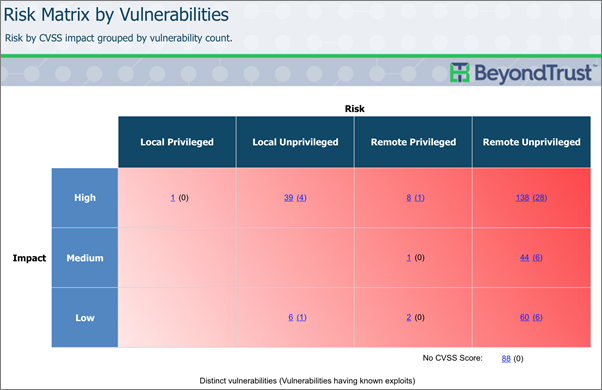
Risk Matrices and Heat Maps empower you to work smarter by alerting you to critical vulnerabilities in a meaningful and actionable way.
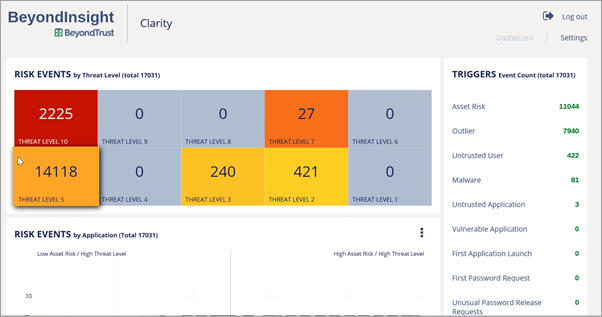
BeyondInsight Clarity Dashboard quickly allows organizations to identify threats by asset, user and application.
Christopher Kissel, Network Security Industry Analyst at Frost & Sullivan recently said, “BeyondTrust is a company that recognizes there is so much more that goes on in vulnerability management than the scan. In addition to scanning endpoints, BeyondTrust platforms can offer privileged access management, detect indicators of compromise in applications, and monitor transitions of users and assets in smart groups.”
Here are just a few more examples of what elevates Retina CS above the competition and keeps you steps ahead of the bad guys.
- Analyst coverage: See what Frost and Sullivan had to say and why Retina CS won their 2015 Global Vulnerability Management (VM) Enabling Technology Leadership Award.
- Customer insights: Listen to what our customers say makes the Retina Difference.
- Video: Learn about the 5-keys to context-aware vulnerability management.
If you haven’t yet evaluated Retina CS, welcome. And if you’re returning after a couple of years to see what has changed, welcome back. Either way we think you will be delighted with what you find.\
Don’t let the company that abandoned you lead you down the wrong path again. There is a better alternative. But don’t take our word for it. Come see for yourself what you’ve been missing! Learn more about Retina CS, or contact us now.

Scott Lang, Sr. Director, Product Marketing at BeyondTrust
Scott Lang has nearly 20 years of experience in technology product marketing, currently guiding the product marketing strategy for BeyondTrust’s privileged account management solutions and vulnerability management solutions. Prior to joining BeyondTrust, Scott was director of security solution marketing at Dell, formerly Quest Software, where he was responsible for global security campaigns, product marketing for identity and access management and Windows server management.








